Your Cybersecurity Is Only as Strong as Your People
Oct 08
Experience OutThink
Even with all the latest technology in place, human error still causes most cybersecurity breaches. In 2024, a report highlighted that 95% of data breaches involved human error, according to Infosecurity Magazine.
Professor Philip Morgan, who leads the Human Factors Excellence Research Group at Cardiff University, explains it best:
“Too many organizations still either ignore the ‘human risk factor’ in their organizational resilience or apply outdated or compliance-driven 'tick-the-box' approaches to training their employees about cyber security.”
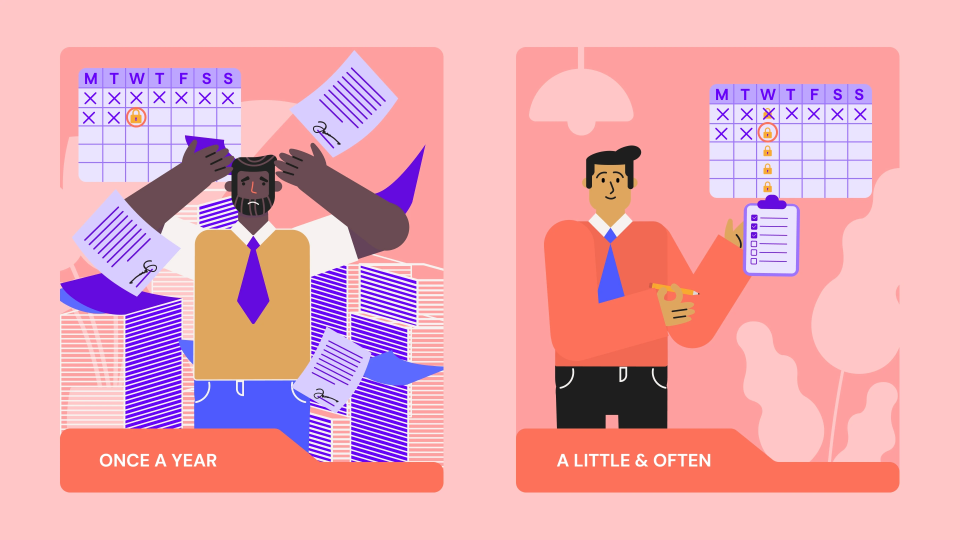
And he’s right! YOUR company might be one among the many companies who treat cybersecurity training like a checklist, something you do once a year, just to say you did it.
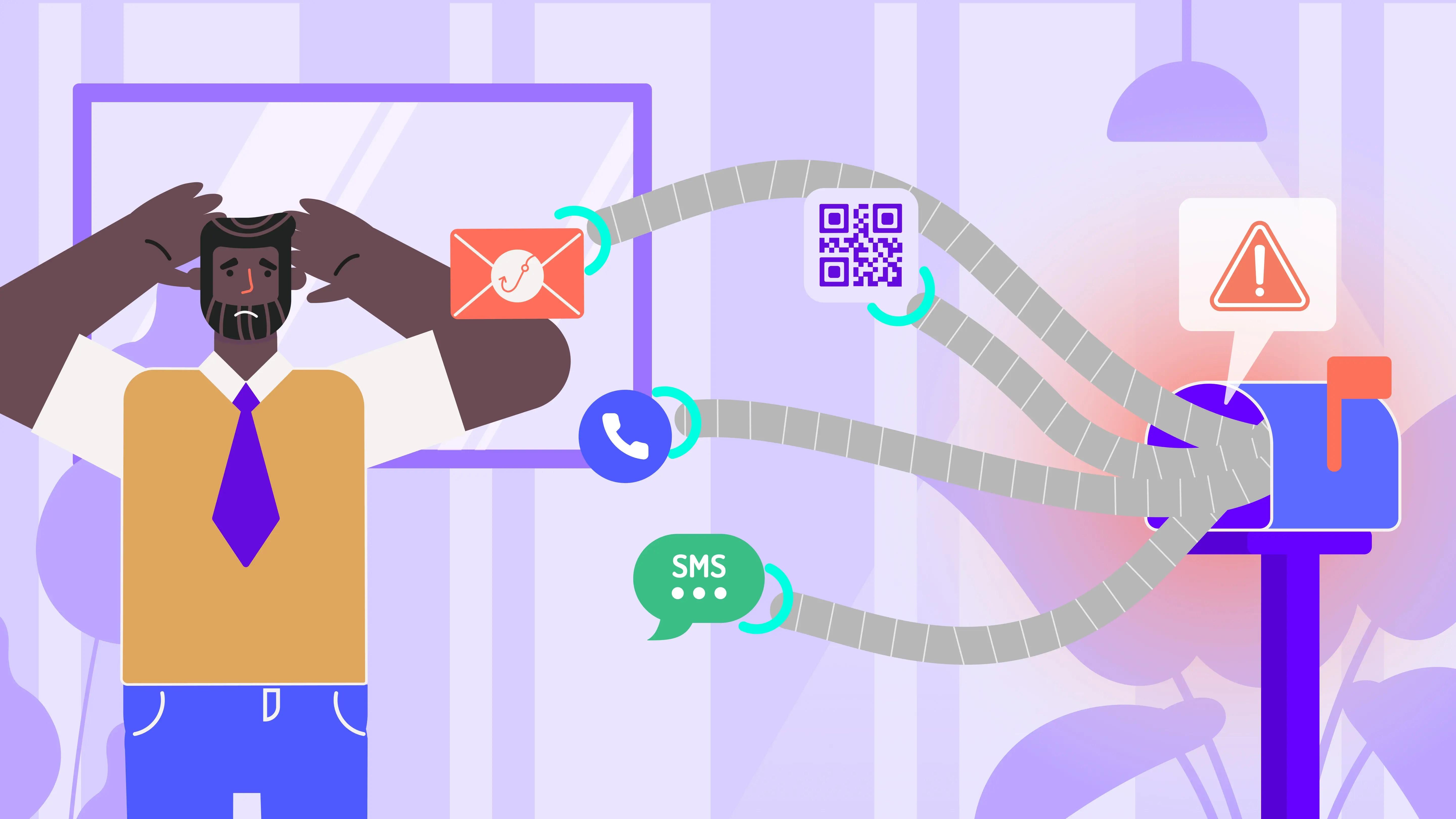
But here’s the catch: those traditional training methods don’t stick for long. Neither do they change behavior nor do they help people gear up to face the real world threats. Today’s digital world is constantly evolving, and so are the tactics used by cybercriminals. We need to adopt a smarter and more human-centric approach that helps employees actually understand what’s at stake and how to respond.
How Do You ‘OutThink’ the Human Risk Factor?
This is where OutThink’s Cybersecurity Human Risk Management platform comes in, and it’s the ‘game changer’.
OutThink treats humans as the key players in you organization’s security strategy. The platform helps companies identify, manage, and reduce human risk in real time. Here’s how:
1. Behavioral Risk Scoring
OutThink doesn’t guess where the problems are, it uses real data. The platform constantly monitors and analyzes employee behaviors to spot risky patterns. With these data-driven approaches, companies can focus their training and security efforts on the areas that need the most attention, rather than taking a blanket approach. It’s all about being precise and proactive.
2. Role-Specific Training
Let’s face it: a marketing intern doesn’t need the same security training as a system administrator. OutThink understands this. That’s why the platform creates customized learning journeys based on each employee’s role, behavior, and risk profile. Such personalized training makes it easier for employees to relate to the content and apply what they’ve learned. That’s when real change happens.
3. Continuous Engagement
Cybersecurity is not a one time event. Threats evolve, and so should your people. OutThink keeps the momentum going with regular updates, learning nudges, and ongoing training modules that reinforce good habits. This ensures that security awareness becomes part of the day-to-day culture and not just an annual chore.
Say Hello to Behavior-Based Cybersecurity!
Let’s be honest: those compliance-driven, checkbox-style training sessions never really worked, did they? OutThink is built to go well beyond legacy security awareness training. It puts behavioral insights and human risk analytics front and center. Instead of asking “Did they take the training?” it asks, “Did the training change anything?”
This shift in mindset empowers organizations to build a security-first culture, where employees feel responsible and capable, not just obligated. They become active defenders of your organization’s data, rather than passive participants.
Train Your Employees to Be Cyber Resilient
By creating an environment where people are actively involved in security processes, OutThink fosters this kind of empowered environment. It transforms employees from being potential risk factors into confident decision makers and defenders of the organization’s digital assets.
And the benefits? Fewer breaches, faster threat detection, better team coordination, and a more resilient organization overall.
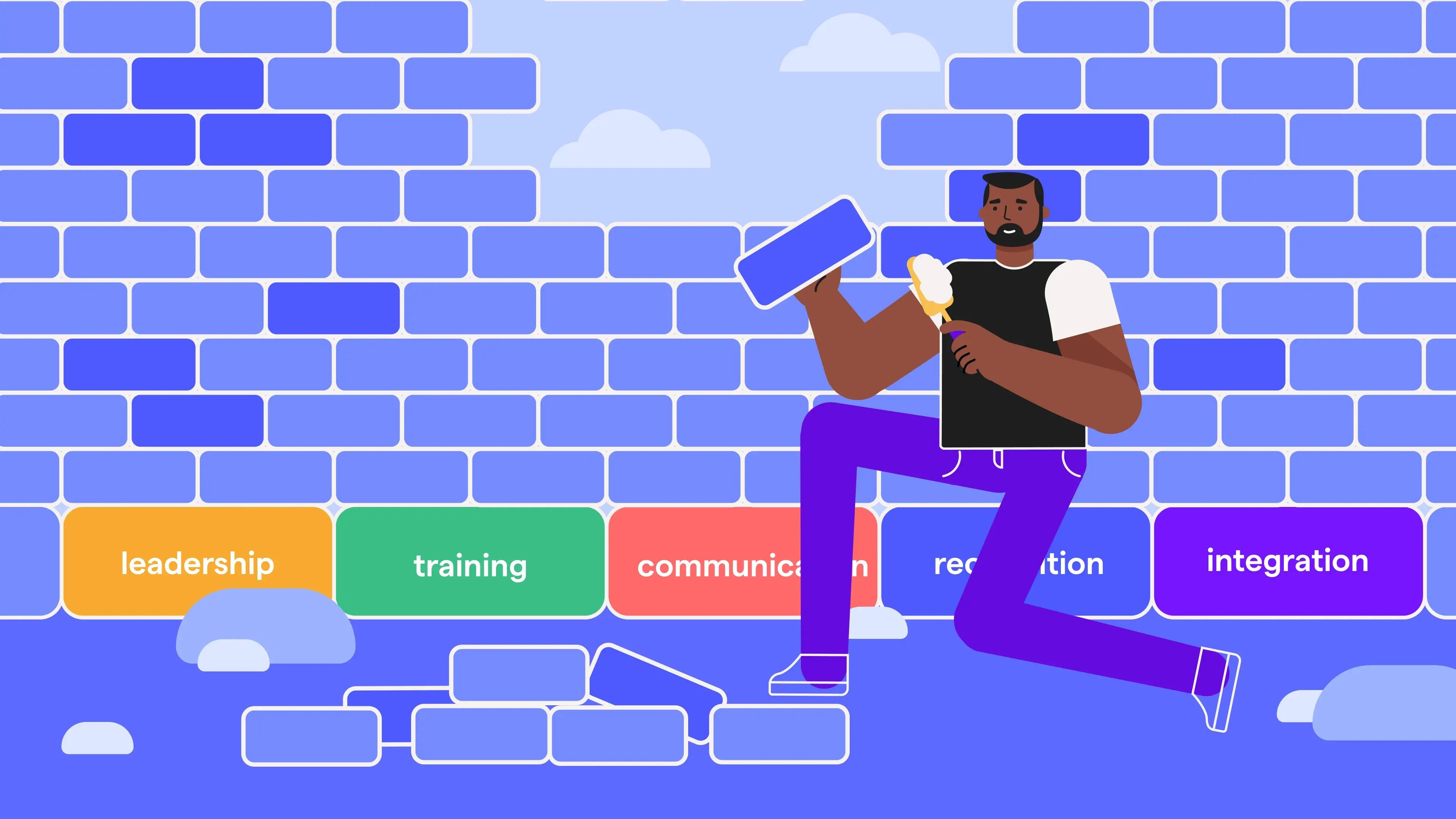
Building a Stronger Security Culture Starts With Your People
OutThink’s Cybersecurity Human Risk Management platform gives organizations the ability to build that readiness, by combining smart analytics, personalized training, and a human first strategy.
Curious to see how it works?
Check out OutThink’s Cybersecurity Human Risk Management platform and learn how you can turn your team into your first line of defense.