Would You Skip an Update if You Knew What It Could Cost You?
Oct 24
Experience OutThink
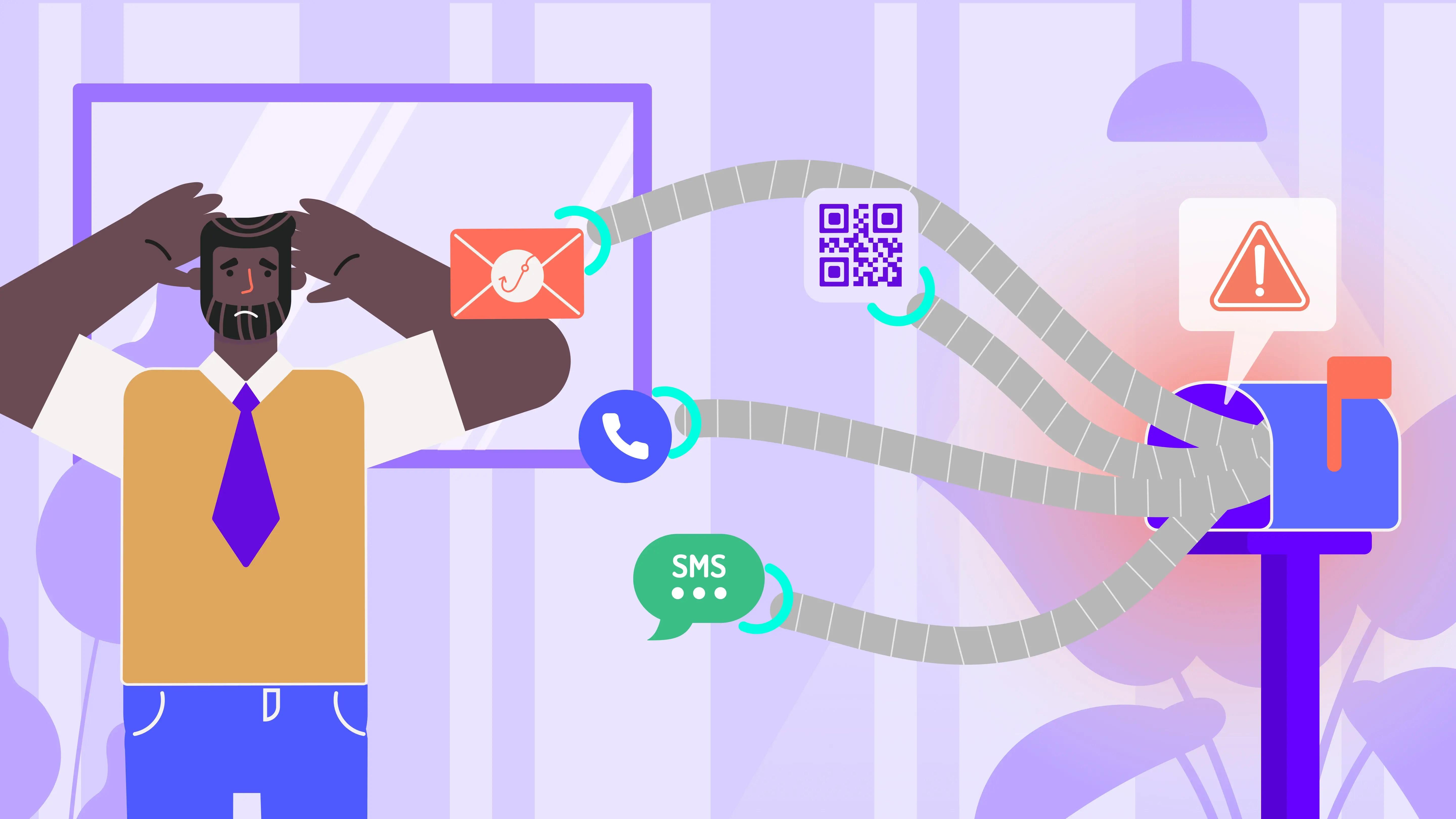
We get it! Those software update pop-ups always show up at the worst time. You’re in the middle of something, and your device suddenly wants to restart, download, or install something “critical.” Most of us hit “remind me later” and move on. But here’s the thing: every time we delay that update, we could be leaving the door wide open for cyber attackers.
Agencies like CISA and the National Cybersecurity Alliance are reminding everyone, individuals and businesses alike, that updating your software is one of the simplest, most effective ways to protect yourself.
So….why do so many people still ignore it?
Why Software Updates Actually Matter (A Lot)
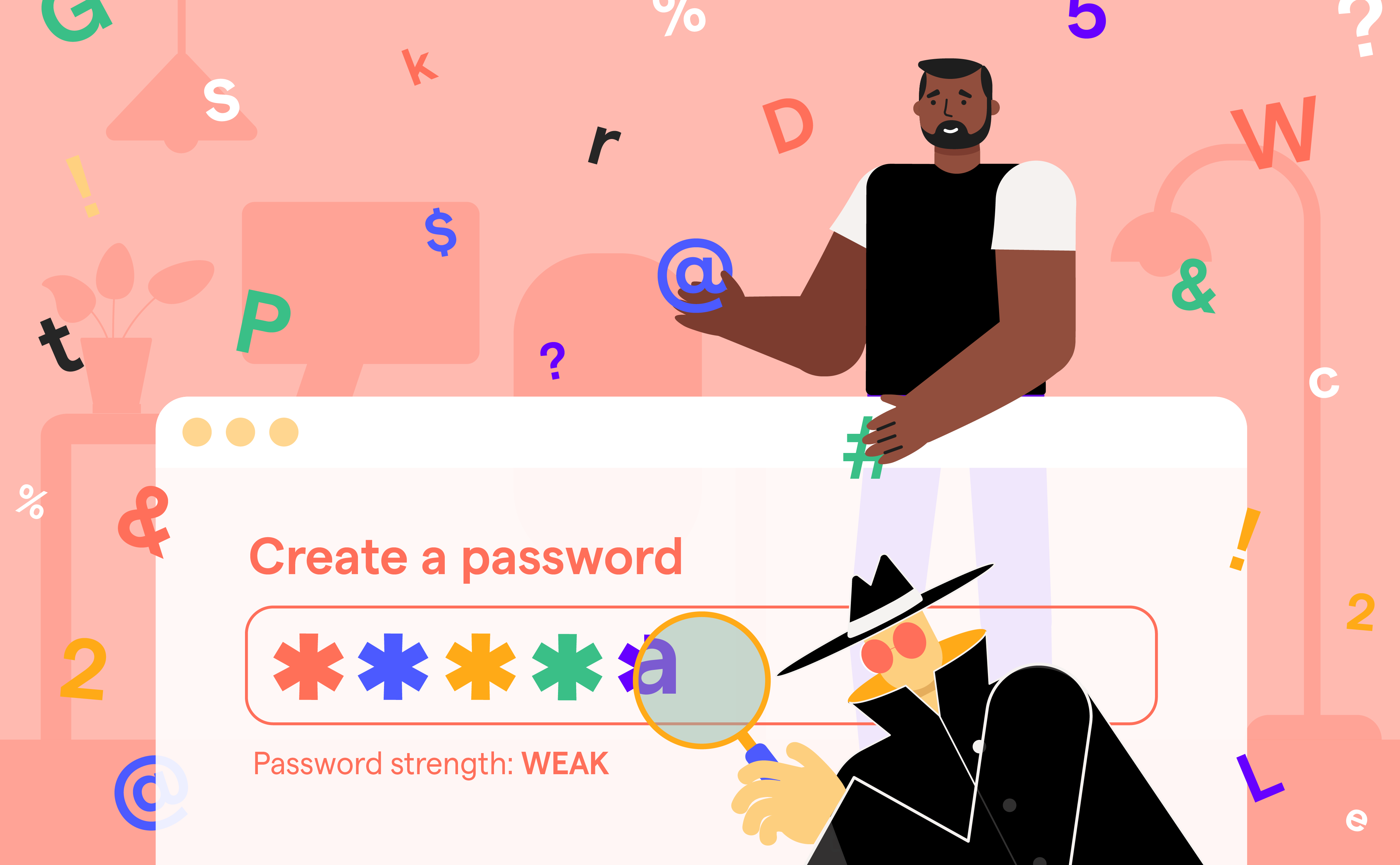
Software updates play a crucial role in patching security vulnerabilities, improving system performance, and enhancing user experience. Every software or operating system contains weaknesses that can be exploited by malicious actors. Hackers often scan for these vulnerabilities, particularly in outdated software versions, to infiltrate systems and compromise sensitive data. According to the Cybersecurity and Infrastructure Security Agency (CISA), updating software is one of the simplest yet most effective ways to prevent these attacks.
Outdated software is like an unlocked door, while it might not immediately invite trouble, it certainly makes an attack easier. Many high-profile data breaches and ransomware incidents occurred because an organization failed to install a security patch in time. CISA underscores the critical need to "understand patches and software updates" because failure to do so could lead to costly consequences. By updating your software, you’re closing these vulnerabilities and making it harder for attackers to exploit systems.
How Do You Turn Update Habits Into Cyber Resilience?
Here’s where things get interesting!
Most cybersecurity conversations focus on technology, the firewalls, the antivirus tools, the patches. But what about people? That’s where OutThink comes in.
As a leader in cybersecurity human risk management, OutThink recognizes the importance of integrating the human element into cybersecurity measures like updating software. While most organizations focus on the technical aspect of patching vulnerabilities, OutThink goes a step further by emphasizing the behavioral aspect.
Instead of just pushing policies, OutThink helps organizations understand why people procrastinate, who is more likely to do it, and how to shift those behaviors toward better habits.
The Risks of Delaying Updates
Putting off updates isn’t just risky, it’s expensive.
When organizations delay updates, they inadvertently give cybercriminals more time to exploit known vulnerabilities. A prime example is the infamous WannaCry ransomware attack, which took advantage of a known vulnerability in Microsoft systems that had already been patched. Organizations that had updated their systems were protected, while those who delayed the patch suffered significant financial and reputational damage.
Additionally, outdated software is more susceptible to malware and other forms of cyberattacks. According to CISA’s resources on software updates, the longer software remains unpatched, the greater the risk of exposure to increasingly sophisticated threats. By regularly updating, users can stay ahead of attackers, ensuring that they have the latest security measures in place.
Automate Where You Can, Educate Where You Can’t
One easy win? Turn on automatic updates wherever possible. CISA and the National Cybersecurity Alliancerecommend this across all devices. It takes the decision (and the procrastination) out of the equation.
But automation alone won’t cut it, especially in workplaces where employees use personal devices or delay updates for “just a few more hours.” That’s where OutThink’s platform jumps in. It not only encourages automation, but also helps organizations spot employees who tend to delay updates. Then, it delivers timely nudges, personalized training, or check-ins, all based on actual behavior.
Here’s How You Build the Culture That Stays Compliant
Ensuring that your software is updated should be a standard operating procedure across all levels of an organization. The National Cybersecurity Alliance provides straightforward guidelines for implementing a company-wide update policy. However, awareness alone isn’t enough.
OutThink helps organizations create real change by:
- Integrating update reminders into employee workflows
- Tailoring messaging to the behavior of different user groups
- Reinforcing the importance of patches with relevant, engaging training
When employees see the why behind the what updates stop feeling like an interruption, and start becoming part of a secure routine.
Remember to Update Your Software!
In today’s fast-moving threat landscape, waiting even a few days to update could leave you exposed. The good news? Software updates are completely in your control, and they offer one of the best returns on your cybersecurity investment.
Don’t just talk about security. Act on it. And help your team do the same.