How AI Is Supercharging Smishing – and What Can Actually Prevent It
Feb 18

Get in touch with our HRM Specialists
In 2025, nearly 80% of organisations reported experiencing smishing attacks, with incidents rising sharply compared to prior years, making SMS-based phishing the dominant mobile threat. And of course, human behaviour remains the most significant breach contributor in mobile environments, with up to 39% of users in smishing simulations clicking malicious links, even when alerts are raised.
Financial impact? While overall SMS fraud losses peaked at around $80 billion in 2025, industry analysis forecasts a slight decline, around 11%, in 2026 as operators strengthen detection, yet the underlying threat persists.
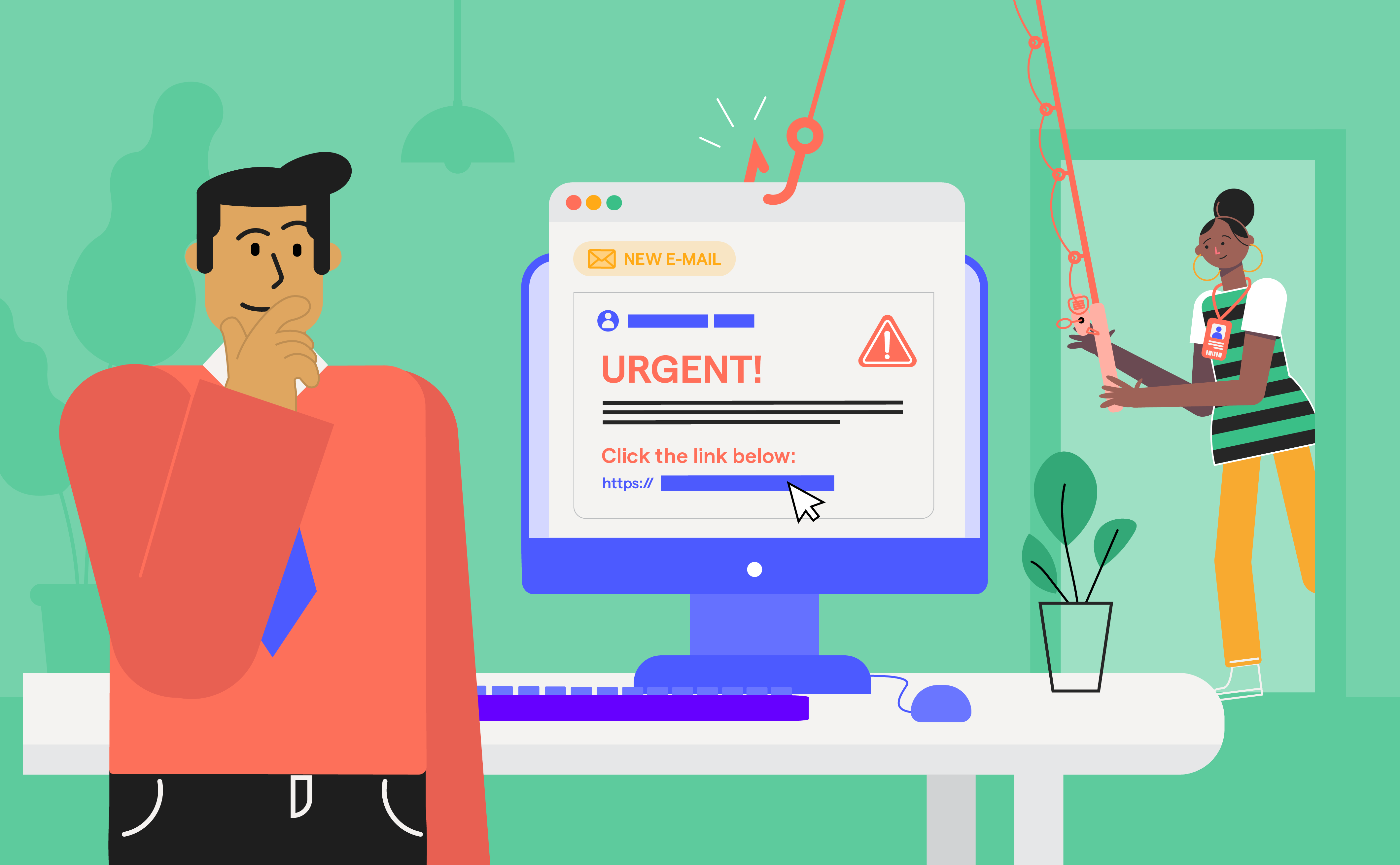
Smishing isn’t growing because employees are careless, but because SMS-based attacks exploit moments when traditional security controls simply don’t exist: personal devices, the urgency of instant notifications, perceived authority, and human trust. Unlike email, SMS bypasses corporate email gateways and endpoint controls and lands directly in a person’s pocket, where security checks are weakest.
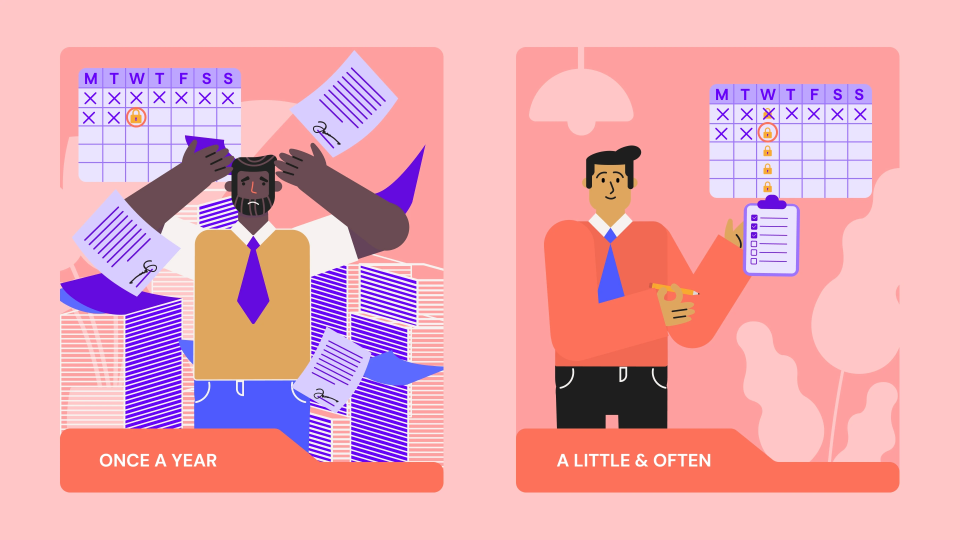
In 2026, preventing smishing is no longer about blocking suspicious messages or teaching red flags once a year. It’s about understanding how people behave under pressure, often on personal devices, outside corporate controls, and intervening before a rushed tap becomes a breach. Traditional awareness fails to measure decision fatigue, distraction, and authority bias, which are key drivers of smishing success.
This article examines why modern smishing works, where controls fail, and how behaviour-driven Human Risk Management, exemplified by OutThink, is emerging as the only scalable defence.
What this blog will help you understand
- Why smishing succeeds even in organisations that invest heavily in email security and awareness training
- How modern SMS attacks exploit behavioural gaps, not just technical vulnerabilities
- Why traditional phishing metrics like click rates fail to measure real smishing risk
- How AI has made smishing more personalised, scalable, and harder to detect
- What behavioural signals actually predict SMS-based compromise under pressure
- How leading security platforms differ in their ability to measure and influence smishing risk
- Why the future of smishing defence depends on predictive behavioural intelligence, not static training
Smishing Succeeds In the Gaps Between People and Security
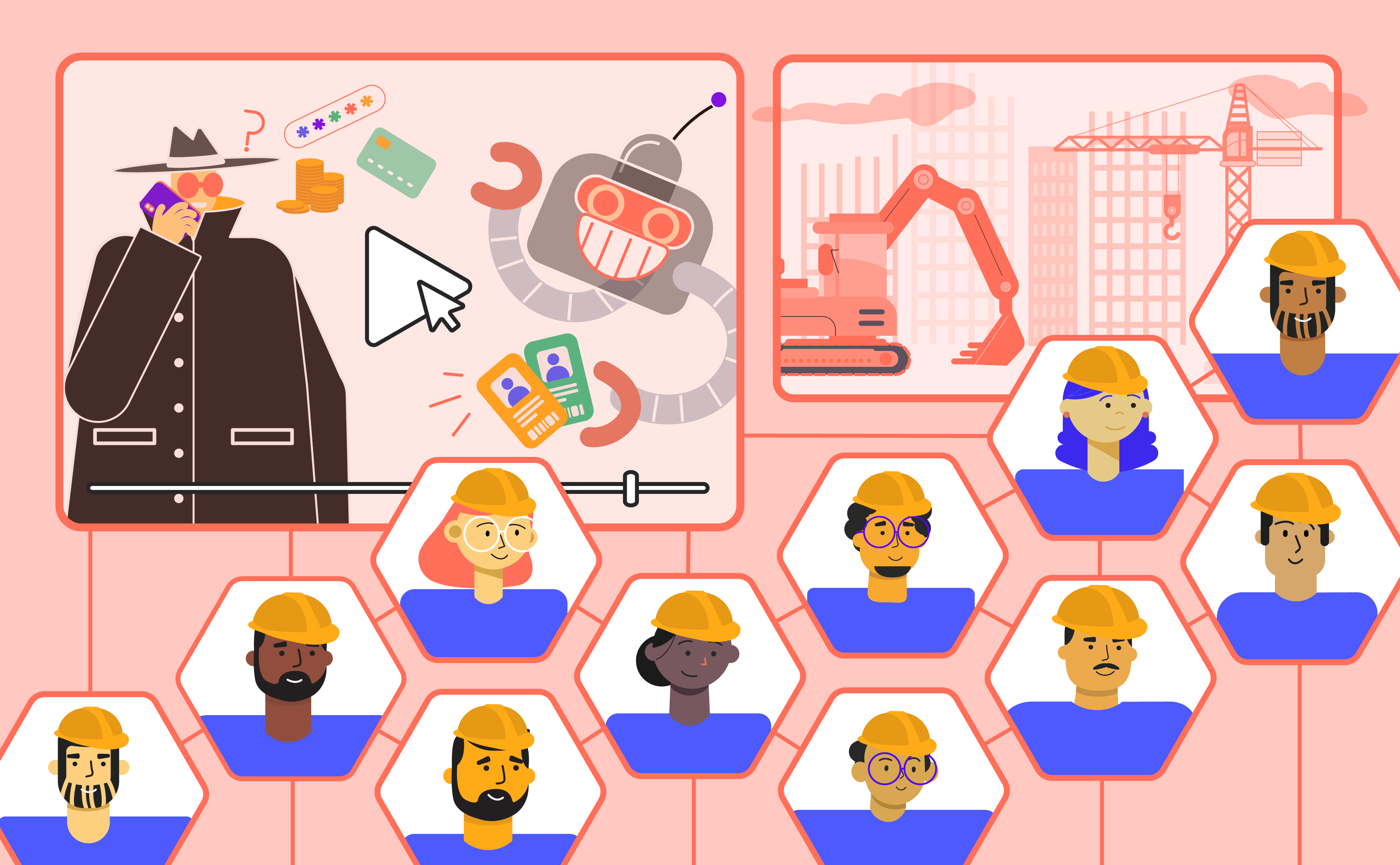
In 2025, Google filed a civil lawsuit against a China-linked cybercriminal network dubbed the “Smishing Triad”. The group allegedly ran massive SMS phishing campaigns across more than 120 countries, impersonating trusted brands and targeting millions of victims. That case made one thing very clear: smishing is no longer opportunistic spam. It is organised, industrialised, and financially motivated at scale.
For enterprises, however, the real concern isn’t just the volume of attacks. It’s where these attacks land - in the gaps between corporate security controls and human behaviour.
Smishing works because SMS operates outside the systems that organisations are designed to monitor and defend. Corporate email gateways are highly effective at scanning links, attachments, and suspicious domains, but text messages never pass through those filters. As a result, the organisation’s main phishing controls never come into play. EDR tools are engineered to monitor malware and abnormal activity on laptops and servers, not to analyse incoming SMS content on mobile devices and that leaves a digital blind-spot.
In BYOD environments, MDM solutions often avoid deep inspection of personal text messages for privacy and technical reasons, meaning SMS traffic typically falls outside enforcement policies. At the same time, SOCs rely on logs and telemetry flowing into SIEM platforms. Because SMS delivery and content are rarely integrated into these data streams, attacks often remain invisible until after an employee has clicked a malicious link or approved a fraudulent login request.
This architectural gap explains part of the problem, but technology alone does not make smishing effective. The real advantage begins the moment the message reaches a person.
Modern smishing is psychologically precise. It targets personal devices, like the phones people check first and treat as intimate spaces. Text messages feel immediate and urgent in a way that email rarely does. Attackers amplify this by creating time pressure, such as warning that an account will be locked or a delivery will fail, pushing individuals to prioritise speed over scrutiny.
They also mimic authority and routine. For example, messages appearing to come from “HR,” “IT,” or a trusted bank lower defences, whereas fake MFA prompts, payroll alerts, or delivery updates blend seamlessly into everyday workflows.
Unlike email phishing, smishing captures attention in real time, offers fewer visible verification cues, and triggers reflexive action. It succeeds not because organisations ignore phishing, but because SMS sits outside traditional monitoring frameworks while directly tapping into human habits. Closing that gap requires rethinking both visibility and behaviour and not simply adding another filter.
But understanding where smishing slips through security is only part of the story. To reduce the risk, we first need to understand how modern smishing attacks are actually constructed.
Anatomy of Modern Smishing Attacks
If old-school phishing was largely about spotting a suspicious link or poorly written email, modern smishing is far more refined because it focuses on shaping behaviour rather than merely tricking the eye. Instead of clumsy “click this obvious scam” attempts, today’s SMS-based attacks are carefully engineered around trust, urgency, familiarity, and increasingly, artificial intelligence, making them feel less like threats and more like routine digital interactions.
Modern smishing campaigns may vary in theme, but they consistently rely on a set of repeatable behavioural triggers. Below are the most common formats seen across industries today, each designed not just to trick users, but to guide them toward fast, uncritical action.
- Impersonation / Brand Spoofing: Attackers send SMS messages posing as trusted entities such as banks, courier companies, telecom providers, or government agencies, using familiar names and branding cues to lower suspicion and collect personal or financial information.
- Account Suspension / Security Alerts: These messages warn that an account has been locked, compromised, or flagged for suspicious activity, prompting users to “verify” their credentials immediately, often through a fraudulent login page.
- Missed Delivery / Package Scams: Capitalising on high e-commerce activity, victims receive fake delivery notifications claiming a package is delayed or requires confirmation, with phishing links designed to harvest login or payment details.
- Prize / Lottery / Reward Scams: Texts claim the recipient has won a prize, cashback, or promotional reward and must click a link to claim it, ultimately exposing sensitive data or payment information.
- Charity / Donation Scams: Exploiting crises or emotional appeals, these messages request urgent donations or financial support for fabricated or dubious causes, directing victims to fake payment portals.
- Malware Link Delivery: Instead of credential theft alone, some smishing attacks deliver malicious software through links disguised as updates, security patches, or document downloads, compromising the device itself.
- Service Cancellation / Renewal Scams: Users are warned that a subscription, utility service, or account will be cancelled unless they update their details immediately, leading them to convincingly cloned websites.
- QR Code Smishing: Messages include malicious QR codes that redirect users to phishing sites, leveraging the fact that mobile users often scan QR codes without verifying the destination URL beforehand.
How has AI changed smishing
Artificial intelligence has significantly strengthened these tactics because it enables highly localised language that reflects regional tone and cultural context, while also producing polished messages that closely mimic legitimate brand communication styles. Automation further allows attackers to optimise timing, sending messages during busy work hours or moments of fatigue when decision-making is weaker. At scale, AI generates thousands of slight variations of the same message, making pattern-based detection more difficult, and in some cases, smishing is combined with AI-driven voice phishing in multi-stage attacks to reinforce legitimacy.
A defining example of modern smishing at scale is the “0ktapus” campaign, which targeted more than 130 organisations, including Twilio. Employees received SMS messages disguised as routine authentication alerts and were directed to highly convincing fake login portals. When users entered their credentials, attackers captured usernames, passwords, and even multi-factor authentication tokens in real time. Notably, the campaign did not depend on malware or technical exploits; instead, it leveraged trust in familiar workflows such as single sign-on and MFA verification.
The consequences went far beyond a few compromised accounts. Stolen credentials enabled attackers to move laterally within internal systems, access sensitive customer data, and disrupt operations. In Twilio’s case, internal tools and customer-related information were exposed, demonstrating how a single SMS entry point can escalate into significant organisational risk. The real threat lies in the repeatable behavioural pattern that attackers continue to exploit.
When attacks are engineered around behaviour, traditional awareness alone isn’t enough. The real question then becomes: what actually reduces smishing risk in measurable ways?
What Actually Reduces Smishing Risk
If smishing is engineered around human behaviour, then effective prevention must also focus on behaviour. The shift is simple but powerful: instead of only blocking messages, organisations must make user decisions observable, measurable, and influenceable over time. Below are the behavioural levers and KPIs that matter most:
What effective smishing defense measures track
- Hesitation vs Impulse: The time a user pauses before interacting with a suspicious SMS reflects whether they are engaging critical thinking or reacting automatically. Even a few extra seconds of hesitation can significantly reduce risk.
- Reporting Speed: How quickly users report suspicious SMS messages directly impacts attacker dwell time. Faster reporting enables quicker containment and reduces the window for exploitation.
- Near-Miss Patterns: Tracking moments where users almost clicked but stopped reveals early warning signals. These behavioural near-misses help identify rising risk before an actual compromise occurs.
- Decision Degradation Under Pressure: Measuring how users respond under urgency, authority cues, or time pressure highlights where decision quality weakens and where targeted training is most needed.
The KPIs that matter for Smishing
- Smishing Failure Rate: The percentage of users who fall for simulated or real smishing attempts, providing a clear indicator of current organisational risk exposure.
- Reporting Rate: The proportion of suspicious SMS messages that users proactively flag for review, reflecting engagement and awareness levels.
- Mean Time to Report (MTTR): The average time between receiving a suspicious SMS and reporting it. Shorter MTTR reduces potential damage and attacker access.
- Behavioural Drift Over Time: Tracking how user responses evolve across multiple campaigns ensures that improvements are sustained and not just short-term gains after a single training effort.
If behaviour is the key risk layer, the next step is evaluating which platforms can truly measure and influence it. Not all smishing protection tools operate at the same depth, and the differences matter.
Comparing Smishing Security Vendors
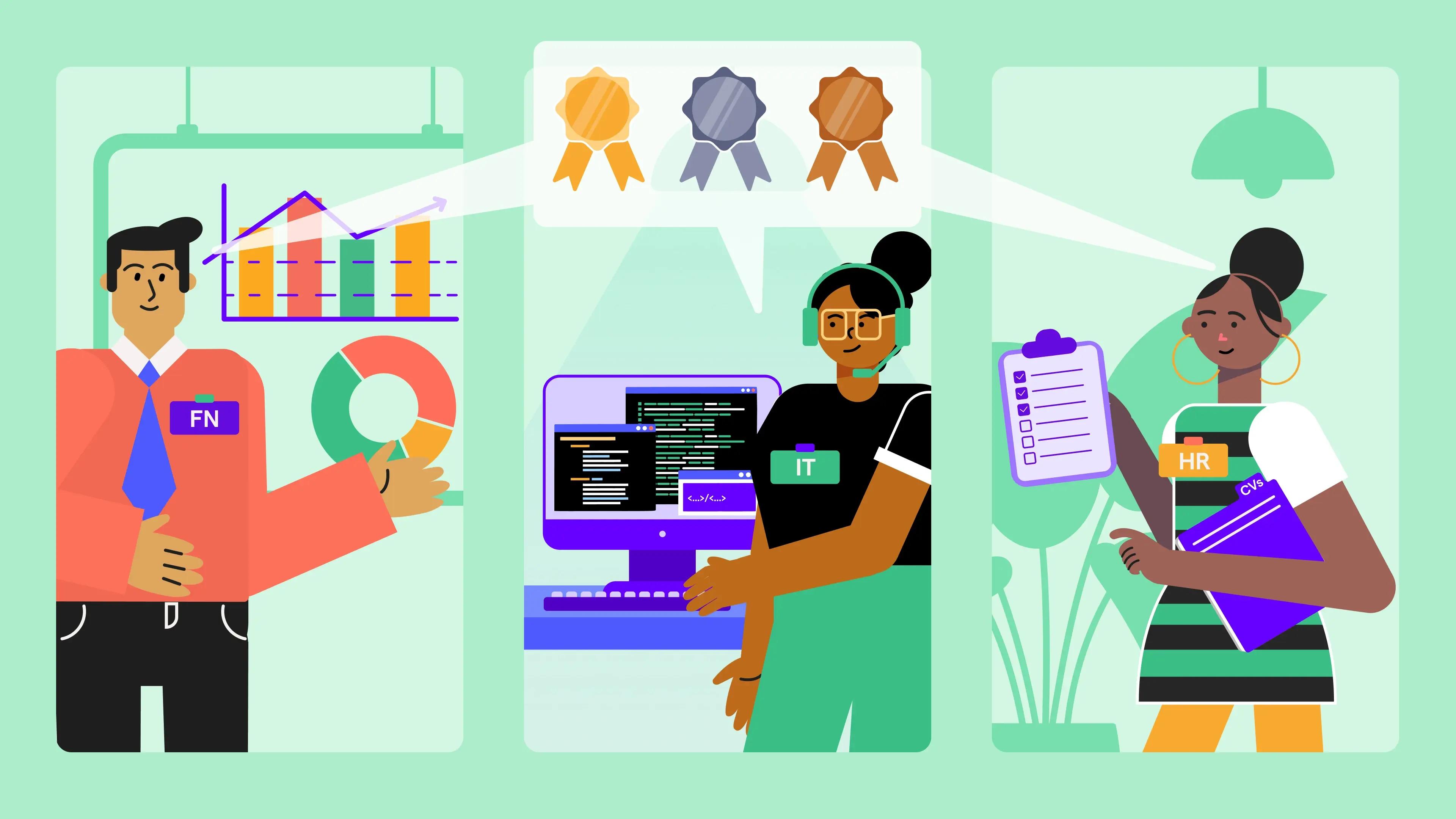
Most security vendors now claim to support smishing, but that label often hides very different capabilities. Some platforms focus on awareness content, others on phishing simulations, while only a few measure how people actually behave when SMS attacks arrive on personal devices, under time pressure, and outside corporate controls.
For enterprise leaders, the key distinction is whether a platform can observe behaviour, simulate realistic SMS threats, and influence decisions in real moments. The table below compares leading platforms using only smishing-relevant capabilities that materially affect risk:
| Vendor | Behaviour Measurement & Analytics | Adaptive/Contextual Training | Best Fit Use Case |
|---|---|---|---|
| OutThink | Very high: human risk & behaviour metrics focused on hesitation, reporting patterns, drift over time, etc. | Very high: real-time "nudges" in Teams/Slack and contextual training that adapts to specific user risk signals. | Enterprises needing behaviour-centric resilience and risk reduction |
| Hoxhunt | High: adaptive, gamified behavioural learning and reporting rates | High: AI-driven adaptive campaigns and micro-training | Organisations focused on engagement and measurable behaviour change |
| KnowBe4 | Medium: large library with reporting but less deep behaviour signals | Medium: broad training modules with some AI enhancements | Organisations needing wide awareness coverage and compliance |
| Proofpoint | Medium: integrated with threat intel, analytics tailored to email + behaviour | Medium: threat-driven and context-based training recommendations | Enterprises with SOC/IR teams and integrated threat intelligence |
| Cofense | Medium-High: rich analytics tied to incident response and reporting workflows | Medium: targeted simulations tied to threat intel | Organisations with mature SOC and IR priorities |
| Usecure | Medium: standard SAT analytics with KPI tracking | Medium: automated training and remedial flows | Small/mid teams needing simpler SAT coverage |
OutThink
OutThink positions itself as a human risk management platform rather than a traditional security awareness provider. It focuses heavily on behavioural analytics, reporting patterns, and behavioural drift over time. Instead of delivering static training modules, it adapts interventions based on real user behaviour. The platform is built for enterprises that want measurable reductions in human risk, not just compliance metrics.
Key Points:
- Deep behavioural risk scoring beyond click rates
- Tracks reporting trends, and risk drift
- Adaptive, personalised training interventions
- Strong executive dashboards focused on human risk
- Designed for enterprise-scale resilience programs
- Emphasis on long-term behavioural change
Hoxhunt
Hoxhunt focuses on gamified, adaptive security awareness designed to improve engagement and measurable behaviour change. It combines phishing and smishing simulations with AI-driven micro-learning tailored to each user’s risk level. The platform emphasises positive reinforcement and fast reporting behaviour. It is particularly strong in driving high participation and reporting rates across distributed workforces.
Key Points:
- Adaptive phishing and smishing simulations
- Gamified learning to increase engagement
- AI-driven personalised training paths
- Strong mobile engagement and reporting UX
- Measures reporting rate and behavioural improvement
- Integrates with enterprise email security workflows
KnowBe4
KnowBe4 is one of the largest security awareness providers globally, offering an extensive training library and phishing simulation tools. Its strength lies in broad awareness coverage and compliance-driven programs. While it includes reporting metrics and risk scoring, behavioural analytics are less granular compared to human-risk-focused platforms. It is well-suited for organisations prioritising scale and regulatory alignment.
Key Points:
- Large content library covering multiple threat types
- Phishing and limited smishing simulation capabilities
- Phish Alert reporting button integration
- Risk scoring and campaign-level reporting
- Strong compliance and audit alignment
- Suitable for organisations needing a wide awareness rollout
Proofpoint
Proofpoint integrates security awareness with broader threat intelligence and email protection capabilities. Its strength lies in connecting user training with real-world threat data and SOC workflows. The platform is particularly relevant for enterprises that already rely on Proofpoint’s email security stack. While behaviour analytics are present, the focus remains closely tied to threat-driven detection.
Key Points:
- Integrated threat intelligence and awareness
- Context-based training recommendations
- PhishAlarm reporting integration
- Strong SOC and incident response alignment
- Email-centric with behavioural insights
- Suitable for mature enterprise security teams
Cofense
Cofense focuses on phishing detection, reporting, and incident response workflows. Its platform is designed to turn employee reports into actionable intelligence for SOC teams. While it includes simulations and analytics, its core strength lies in operationalising user reporting within security operations. It fits organisations prioritising rapid triage and response.
Key Points:
- Strong reporting-to-SOC integration
- Incident response workflow automation
- Threat intelligence-driven simulations
- Analytics tied to reporting behaviour
- Supports mature SOC environments
- Emphasis on reducing attacker dwell time
Usecure
Usecure offers streamlined security awareness training with automated campaigns and KPI tracking. It is designed for small to mid-sized organisations seeking structured yet simple programs. While behavioural analytics are more standardised, it provides clear reporting dashboards and automated remediation flows. The platform prioritises ease of deployment and operational simplicity.
Key Points:
- Automated phishing and awareness campaigns
- Standard KPI tracking and reporting dashboards
- Remedial training workflows
- Suitable for smaller security teams
- Easy deployment and management
- Baseline coverage across phishing and smishing threats
The Future of Smishing Defences is Prediction
Smishing prevention is shifting from reaction to prediction. Earlier, organisations mainly measured results like who clicked on a malicious link or who reported a suspicious message. While that data is useful, it only tells you what has already failed. The bigger question now is: can we identify who is more likely to fall for an attack under pressure?
Behavioural risk scoring is becoming a continuous early-warning system. Instead of relying on training completion or single campaign results, organisations analyse patterns such as hesitation before clicking, reporting consistency, susceptibility under urgency, and behavioural drift over time. These signals help identify users who may be more vulnerable when pressure, authority cues, or routine workflows are involved.
Importantly, these insights are beginning to influence real security controls rather than remaining static dashboard metrics. Identity and authentication systems can apply step-up verification when behaviour suggests elevated risk. High-value or sensitive transactions can trigger additional confirmation if activity appears behaviourally unusual. Security Operations Centres can prioritise alerts linked to users with higher behavioural risk, improving triage speed and reducing potential impact.
The objective is not flawless human behaviour, which is unrealistic under time pressure. The goal is earlier detection and faster containment. Smishing isn’t defeated when people simply know more. It’s mitigated when systems understand behaviour patterns and intervene before risk escalates.
Sources
- https://zipdo.co/smishing-statistics/
- https://www.verizon.com/business/resources/T550/reports/2025-mobile-security-index.pdf
- https://www.infosecurity-magazine.com/news/sms-fraud-losses-set-to-decline-11
- https://spacelift.io/blog/social-engineering-statistics?utm_source=chatgpt.com
- https://comparecheapssl.com/100-social-engineering-statistics-in-2025-the-latest-stats-and-trends-revealed
- https://timesofindia.indiatimes.com/technology/tech-news/google-sues-china-based-hacking-group-says-misusing-big-brands-including-e-zpass-google-and-others-to-trap-users/articleshow/125272783.cms?utm_source=chatgpt.com
- https://abnormal.ai/blog/email-threats-bypassing-segs
- https://blog.kaymera.com/industry-news-and-articles/why-traditional-edr-falls-short-on-protecting-mobile-devices
- https://1password.com/blog/mdm-vs-device-trust-technical-limitations
- https://www.exabeam.com/explainers/siem-security/the-soc-secops-and-siem/
- https://blog.cleanfox.io/why-are-smishing-attacks-particularly-effective-in-2025/?utm_source=chatgpt.com
- https://wifitalents.com/smishing-statistics/?utm_source=chatgpt.com
- https://spacelift.io/blog/social-engineering-statistics?utm_source=chatgpt.com
- https://keepnetlabs.com/blog/the-most-spoofed-brands-in-sms-phishing-protect-your-business-in-2025?utm_source=chatgpt.com
- https://blog.cleanfox.io/why-are-smishing-attacks-particularly-effective-in-2025/?utm_source=chatgpt.com
- https://www.telewire-inc.com/cybersecurity/why-are-smishing-attacks-particularly-effective/?utm_source=chatgpt.com
- https://www.bitdefender.com/en-au/blog/hotforsecurity/twilio-reveals-hackers-compromised-its-systems-a-month-earlier-than-previously-thought