How Security Behaviour & Culture Programs (SBCP) Actually Change Cybersecurity Outcomes
Feb 27

Get in touch with our HRM Specialists
Many organisations conduct regular security training, yet unsafe security behaviour persists because knowledge alone does not reliably translate into secure actions under real operational conditions. Employees may understand policies but still make risky decisions when facing urgency, authority pressure, heavy workloads, routine tasks, or limited attention. Traditional awareness programs assumed that knowing the rules would produce secure behaviour, but real-world decisions are shaped by context, incentives, and cognitive constraints.
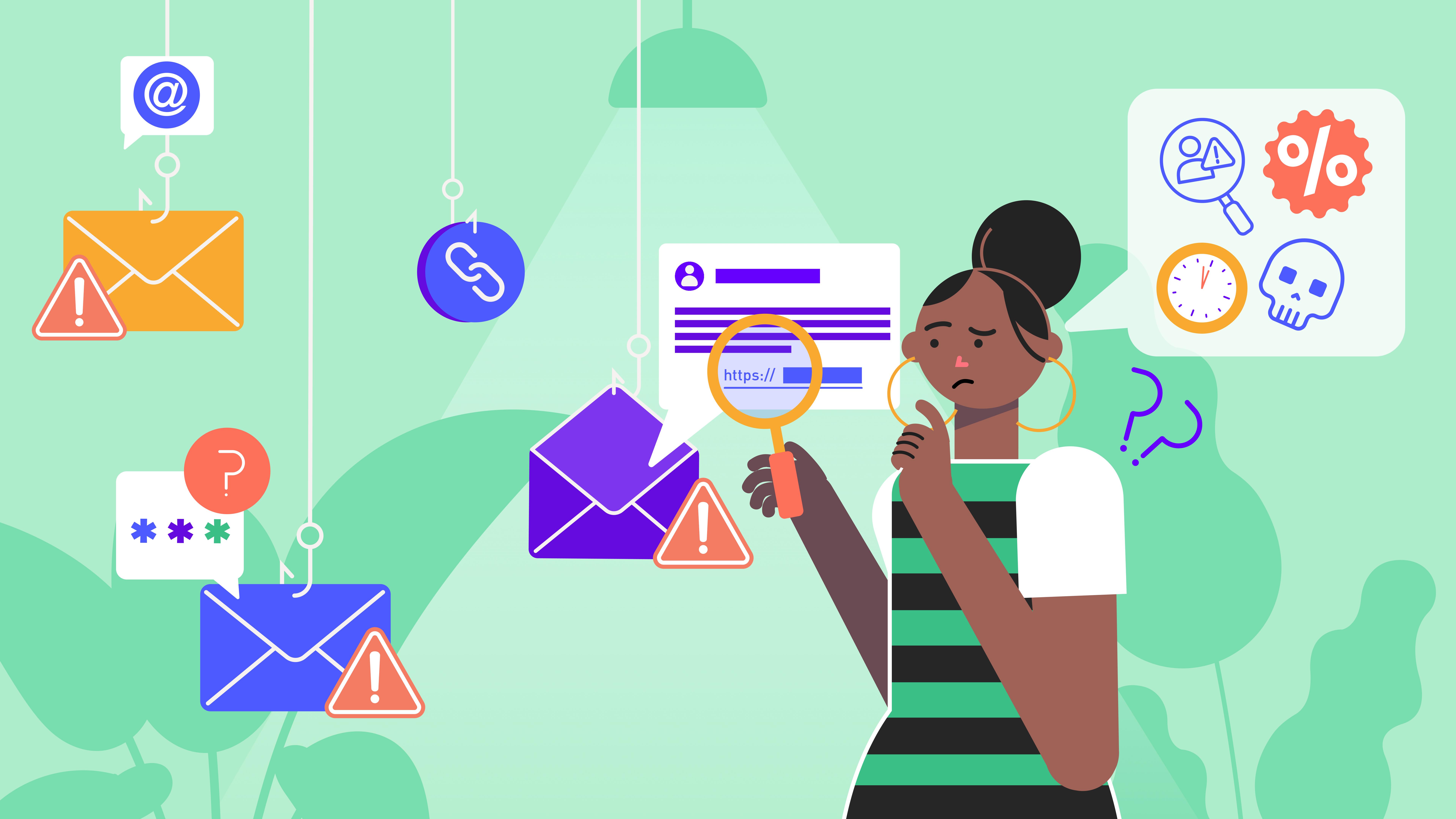
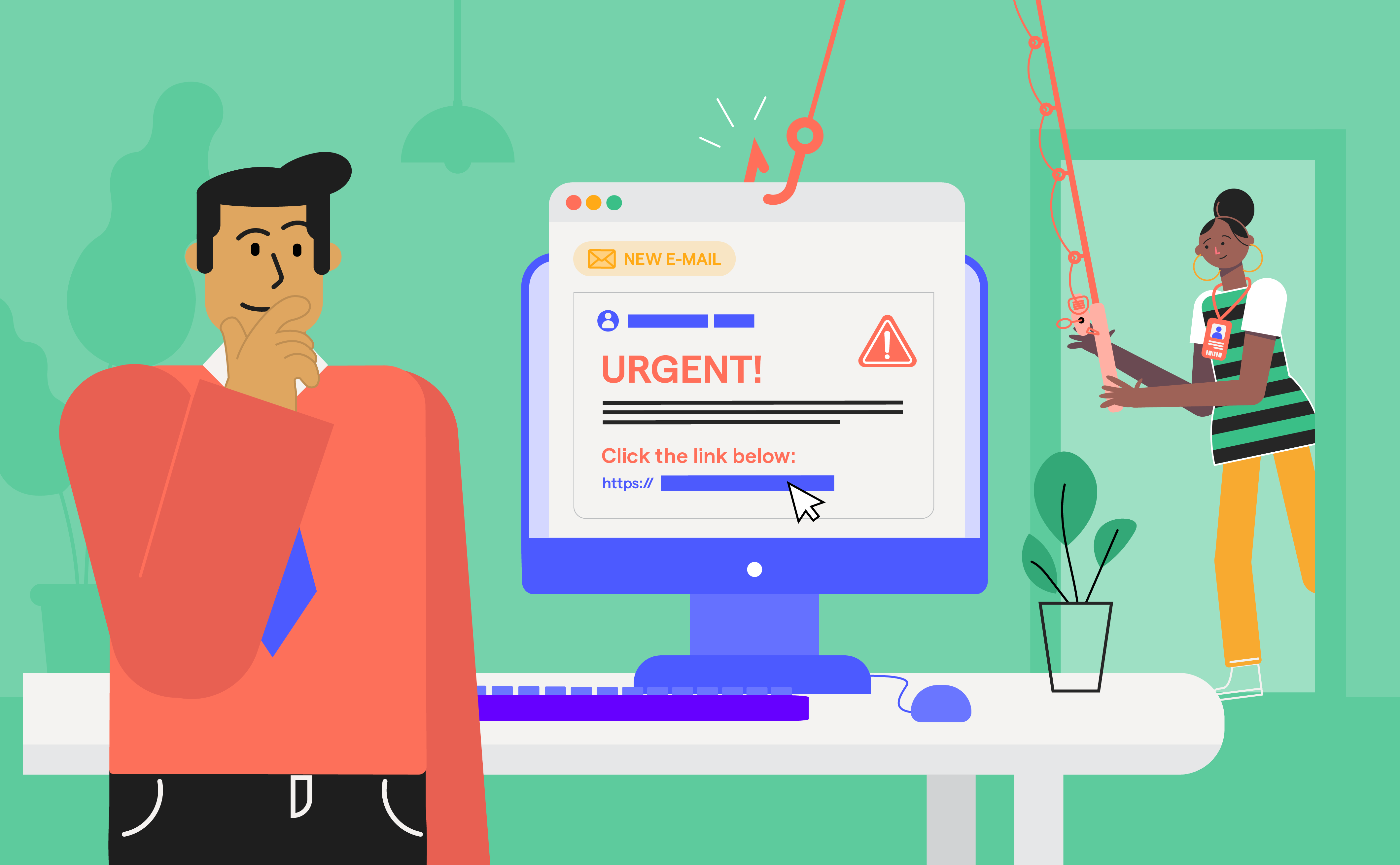
Empirical research shows that awareness efforts often fail to produce measurable improvements in secure behaviour. Large-scale field experiments have found that outcomes in phishing scenarios depend more on situational factors, such as message difficulty or perceived legitimacy, than on prior training, with click rates ranging from roughly 7% for easier attacks to about 15% for more sophisticated ones, regardless of training exposure.
At the same time, human actions now play a dominant role in cyber incidents, with estimates suggesting that around 85% of breaches involve a human element, including error, misuse, or social engineering.
These realities are driving organisations toward Security Behaviour & Culture Programs (SBCPs), which focus on influencing everyday decisions, reinforcing secure behaviour, and embedding security into how work actually gets done.
From Awareness to Behaviour Change: Why the Old Model Failed
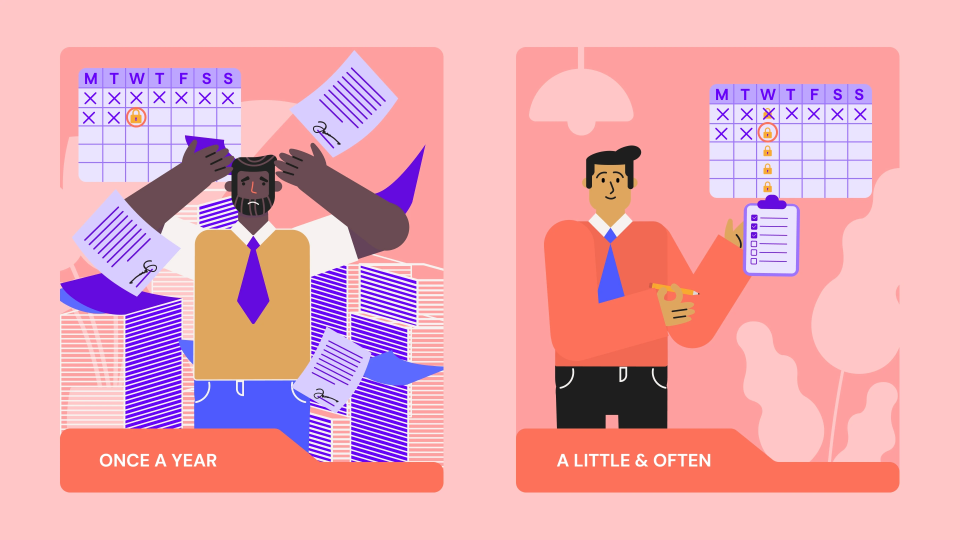
For years, organisations treated cybersecurity as a knowledge problem: teach people what phishing looks like, run annual training, send reminder emails, and secure behaviour should follow.
But real workplaces don’t operate like training slides. People respond to pressure, hierarchy, deadlines, and the need to get work done, not to theoretical rules remembered from a course months ago.
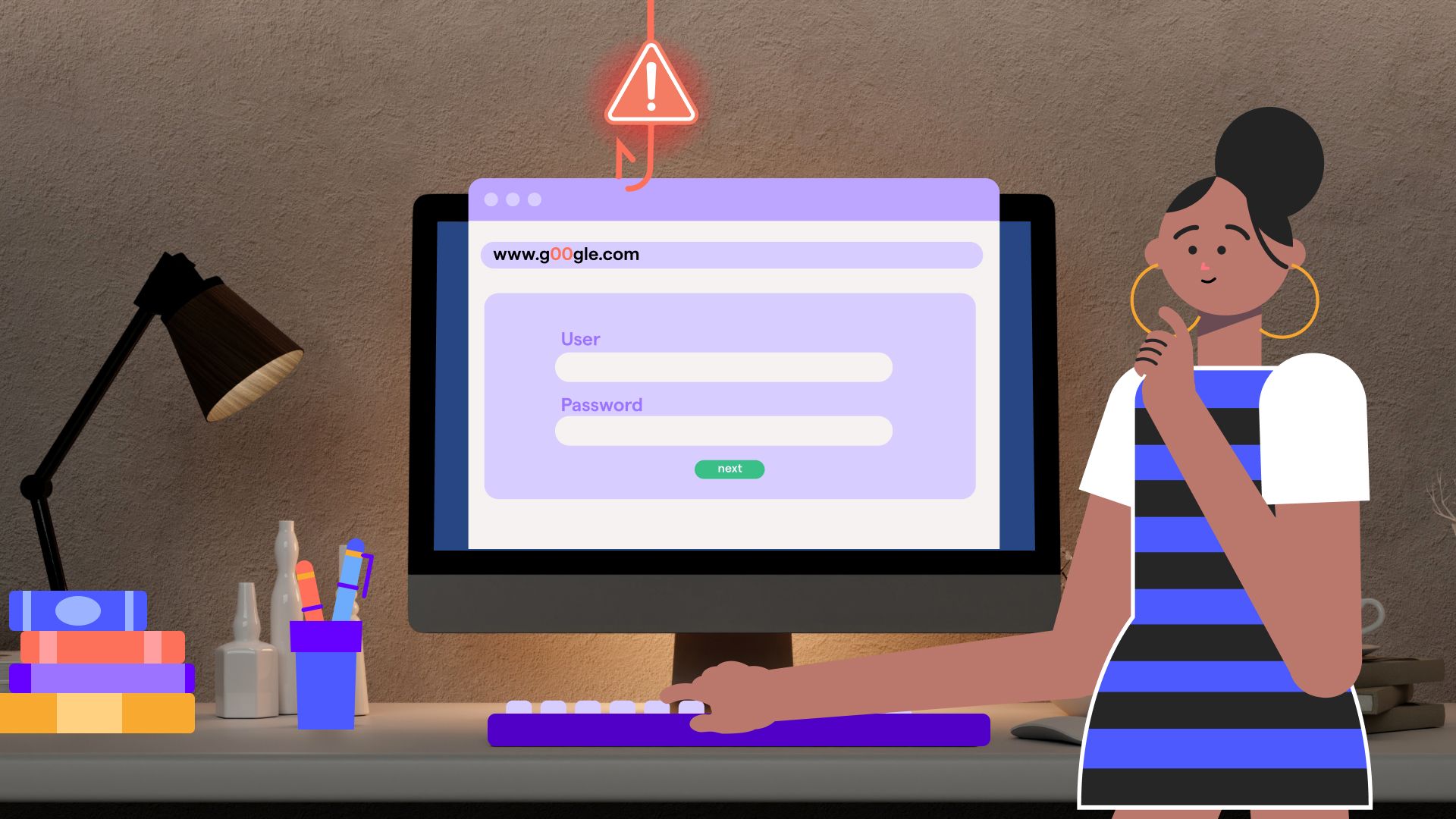
A large real-world longitudinal study of phishing awareness campaigns analysed more than 420,000 simulated phishing emails sent to employees during normal work activity over 1.5 years. Even with ongoing training, employees continued to interact with malicious messages. The researchers found that emails using psychological techniques, especially authoritative tone or curiosity, were significantly more effective than neutral messages, showing that persuasion often overrides learned warning signs in real situations.
Work context makes an even bigger difference. A long-term NIST study tracked employees over 4.5 years of embedded phishing exercises in a U.S. government organisation. Researchers found that people interpreted the same email differently depending on their role and responsibilities. Some clicked because they feared being seen as unresponsive if they ignored the message, while others avoided clicking because they feared malware. In other words, behaviour reflected job pressures, not just knowledge.
Large organisational experiments reinforce how powerful authority and urgency can be. In an open-access study involving 62,000 employees, spear-phishing emails that included authority cues (such as appearing to come from leadership) significantly increased the likelihood that employees would click malicious links. The research concluded that workplace factors, including hierarchy and environmental context, play a major role in susceptibility, even when awareness campaigns are in place.
These findings suggest phishing susceptibility is driven less by lack of awareness and more by workplace pressures. Employees often act based on urgency, authority cues, or job demands rather than training, especially when messages appear work-related. Even well-informed staff may take risks if delaying action feels costly.
The structured approach to closing this gap is explored in our guide on how Security Behaviour and Culture Programs actually change cybersecurity outcomes.
What a Security Behaviour & Culture Program (SBCP) Actually Is
If traditional awareness training is about telling employees what the rules are, a Security Behaviour & Culture Program (SBCP), introduced by Gartner, is about changing how people actually behave in day-to-day work. Instead of assuming that knowledge automatically produces secure behaviour, SBCPs focus on making safe actions practical, visible, and supported across the organisation.
Research shows that effective programs move beyond one-off training sessions and treat security as an organisational issue rather than an individual responsibility. A systematic review of cybersecurity culture research found that strong management support, aligned policies, and continuous engagement are essential for building a functioning security culture.
Real-world case studies of organisations that successfully improved security outcomes show that these programs are built around specific behavioural initiatives rather than generic awareness goals. Common mechanisms identified in research and practice include:
- Security champion networks embedded within teams
- Internal campaigns that keep security visible
- Ongoing communication rather than periodic messaging
- Embedded support so employees can seek guidance during real tasks
These approaches help reinforce secure behaviour continuously instead of relying on employees to remember training from months earlier.
Other research highlights that continuous, relevant learning - especially when supported by leadership - helps organisations build a proactive security culture by addressing human factors alongside technical controls. This approach recognises that employees operate within business pressures and competing priorities, so secure behaviour must be reinforced repeatedly to become routine.
Industry guidance also emphasises that awareness-centric programs alone are no longer sufficient to manage human risk. Organisations are encouraged to foster context-appropriate security cultures that influence everyday decisions, not just responses to obvious threats.
SBCP treats human behaviour as part of the security system itself. The aim is not only to educate employees but to create an environment where secure behaviour becomes the normal and supported way of working.
How SBCPs Actually Change Behaviour
Knowing what to do and actually doing it are two very different things. Security Behaviour & Culture Programs work because they focus on influencing everyday decisions rather than just delivering information. Instead of expecting employees to remember rules from a training session, these programs reinforce secure behaviour repeatedly in the flow of work.
Research on behaviour change shows that people respond best to relevance, repetition, and social cues. Successful programs often borrow techniques from marketing and behavioural science - making the secure choice visible, easy to access, and hard to ignore. That means delivering guidance through multiple channels, tailoring messages to specific roles, and using real-world scenarios that feel immediately applicable rather than theoretical.
Common approaches include short reminders before high-risk actions, role-specific examples that mirror actual tasks, and messaging that connects security to business impact. Peer influence also plays a role: when employees see colleagues taking security seriously, secure behaviour becomes a social norm rather than an optional extra.
Practical engagement tools frequently used in these programs include quick checklists, short stories or case examples, news-based lessons tied to current threats, and regular reminders that keep security top of mind without overwhelming people. These methods help employees apply policies in real situations instead of trying to recall abstract guidance from memory.
Organisations are also increasingly using behavioural techniques such as nudges, which are small prompts that influence decisions at the right moment without requiring extra effort. Examples include warning messages before risky actions, prompts to verify unusual requests, or simplified reporting options. These interventions aim to shape secure behaviour in context rather than relying on deliberate reflection every time.
Measuring and Sustaining Behaviour Change
If Security Behaviour & Culture Programs are meant to change real decisions, then measuring success requires looking at real behaviour and not just training attendance or quiz scores. Traditional metrics say whether employees completed a course; modern indicators reveal whether secure behaviour actually happens when threats appear.
One of the most important behaviour-centric metrics is reporting behaviour and detection speed. Research shows that faster reporting dramatically reduces attacker dwell time and enables quicker containment. Modern programs, therefore, track how long it takes employees to report suspicious messages after receiving them - sometimes called “dwell time” or time-to-report.
These metrics now distinguish between simulated exercises and real incidents, because improvement in real-world reporting is the strongest indicator that behaviour has changed. Studies of adaptive training programs show reporting rates can increase dramatically over time, with organisations observing large gains in both simulated and real threat detection once employees develop a reporting habit.
Another emerging indicator is the report-to-failure balance, also called the resilience ratio. Instead of focusing only on who clicked, organisations assess whether employees report suspicious activity before others interact with it. This approach treats employees as a distributed detection system rather than a vulnerability.
Research also highlights the importance of collective detection behaviour. Large-scale experiments show that when employees are given simple reporting tools, organisations can crowdsource early warning of phishing campaigns, enabling faster response across the enterprise.
Speed remains a critical factor. Cybersecurity studies consistently show that reducing detection and reaction time limits damage from attacks, reinforcing why modern human-risk metrics focus on rapid recognition and response rather than passive knowledge.
Other modern indicators track whether secure behaviour is sustained over time, not just improved temporarily. These include the repeat offender rate, which identifies users who repeatedly fail simulations, and the phish-prone percentage, which measures the proportion of employees likely to engage with malicious content. Organisations also monitor dwell time (time-to-report), which means the time between receiving a threat and reporting it, because shorter dwell time directly reduces exposure. Additional indicators, such as real threat reporting rate and reporting participation rate, assess whether employees consistently detect and escalate actual attacks, not just simulated ones.
Longitudinal research demonstrates that continuous interventions can significantly reduce susceptibility to phishing within months, but improvements may fluctuate due to workforce changes, making ongoing measurement essential.
Together, these indicators shift the focus from compliance to capability. Instead of asking “Did employees complete training?”, organisations now ask:
- Do people notice threats?
- Do they act quickly?
- Do they help protect others?
- Does behaviour improve over time?
By treating employees as active participants in defence rather than passive recipients of training, organisations can measure whether security behaviour is truly becoming embedded in everyday work.
Why SBCPs Matter Now
Security Behaviour & Culture Programs aren’t just a new idea, they’re a response to how work itself has changed.
Today’s employees operate across home networks, corporate systems, cloud apps, personal devices, and AI tools, often within the same hour. Each context creates new opportunities for mistakes, shortcuts, or risky decisions. As a result, human behaviour has become one of the largest and least predictable attack surfaces in modern organisations.
Hybrid work is a major factor. When employees switch between personal and work environments, they are more exposed to insecure Wi-Fi, unmanaged devices, and blurred boundaries between personal and professional activity. Security policies designed for office environments often don’t translate well to these conditions.
At the same time, productivity pressures frequently compete with security expectations. Research shows employees may prioritise business outcomes such as speed, responsiveness, and meeting targets over cybersecurity considerations, especially when controls feel obstructive or irrelevant to their role.
The threat landscape has also shifted toward social engineering and behaviour-based attacks. Human error remains a leading contributor to incidents, with one Gartner estimate suggesting that by 2026, 85% of data breaches will involve a human element, including mistakes, misuse, or manipulation.
Emerging technologies are accelerating this trend. Generative AI, for example, is transforming both productivity and risk. Employees now create content, make decisions, and interact with systems in ways traditional training and controls were never designed to govern. Managing these risks requires shaping how people use technology, not simply restricting access.
Security leaders are responding by shifting from awareness to human risk management. Behaviour-driven programs aim to make employees an active line of defence rather than a passive vulnerability. Organisations that adopt this approach report improvements in control adoption, decision speed, and reductions in insecure practices across the workforce.
Critically, these programs are not standalone initiatives. Successful SBCPs operate as enterprise change efforts supported by leadership, cross-functional expertise, communication channels, analytics platforms, and continuous evaluation, exactly the enabling elements identified in modern frameworks for security behaviour and culture execution.
Looking ahead, the direction is clear. Industry forecasts indicate that by 2030, major cybersecurity frameworks will prioritise measurable behaviour change over compliance-based training as the primary indicator of human risk reduction.
In other words, organisations are moving from “teach people to be secure” to “design systems where secure behaviour actually happens.”
What enables an effective SBCP today
Modern Security Behaviour & Culture Programs are not isolated training initiatives, they are enterprise transformation efforts. Frameworks for SBCP execution highlight several critical enablers that determine whether behaviour change actually occurs.
First, sustained executive support is essential. Leadership must recognise that awareness alone does not reduce risk and must champion behaviour-focused outcomes tied to business priorities such as revenue protection, operational continuity, and reputation. Programs framed purely as compliance activities rarely gain lasting traction.
Second, organisations need a clear and engaging vision that explains why secure behaviour matters and how employees contribute to a safer enterprise. This vision must resonate across roles and functions, not just within security teams.
Third, effective implementation requires cross-functional expertise. Behaviour change involves skills beyond cybersecurity, including communication, organisational change management, behavioural economics, user experience design, and data analysis.
Fourth, programs must be executed mindfully. A one-size-fits-all approach is unlikely to succeed because employees differ in roles, motivations, access levels, and work environments. Tailoring initiatives to these differences increases participation and effectiveness.
Finally, outcomes must be evaluated continuously. Organisations increasingly rely on data from multiple sources, such as training platforms, phishing simulations, security monitoring tools, service desks, and user feedback, to assess whether behaviour is improving and to identify areas requiring adjustment.
Together, these elements illustrate that modern SBCPs operate as ongoing organisational processes rather than one-time campaigns.
That’s a wrap!
As work becomes faster, more distributed, and more dependent on human judgment, managing cyber risk increasingly means managing behaviour. Security Behaviour & Culture Programs provide a structured way to do this - turning policies into practice, awareness into action, and employees into participants in defense rather than sources of risk.
For organisations evaluating how to build or mature such programs, the key question is no longer whether to move beyond awareness, but how quickly secure behaviour can be embedded into everyday operations without disrupting productivity. Platforms designed specifically for human risk management, such as OutThink, aim to support this transition by helping organisations measure, influence, and sustain secure behaviour at scale.
Sources
- https://arxiv.org/abs/2506.19899
- https://informatik.rub.de/veroeffentlichungenbkp/syssec/veroeffentlichungen/2021/pdfs/2021_Spotlight_on_Phishing__A_Longitudinal_Study_on_Phishing_Awareness_Trainings_.pdf
- https://www.nist.gov/publications/user-context-explanatory-variable-phishing-susceptibility
- https://www.sciencedirect.com/science/article/pii/S1071581918303628
- https://arxiv.org/abs/2106.14701
- https://archive.blogs.harvard.edu/jeanlouprichet/files/2022/07/Developing-a-cybersecurity-culture-to-influence-employee-behavior-1.pdf
- https://computerfraudsecurity.com/index.php/journal/article/view/689
- https://www.gartner.com/en/cybersecurity/insights/drive-secure-employee-behaviors
- https://www.nsi.org/securitysense/engagement-behavior-change/
- https://www.cyberdaily.au/security/7681-shift-from-security-awareness-to-improving-behaviour-and-culture
- https://hoxhunt.com/guide/security-awareness-training
- https://hoxhunt.com/blog/4-essential-phishing-metrics
- https://www.mdpi.com/2786112
- https://arxiv.org/abs/2510.27298
- https://www.gartner.com/en/cybersecurity/insights/drive-secure-employee-behaviors
- https://www.gartner.com/en/conferences/apac/security-risk-management-australia/featured-topics/human-factors-in-cybersecurity
- https://outthink.io/gartner-cybersecurity-insights
- https://www.gartner.com/en/newsroom/press-releases/2024-02-22-gartner-identifies-top-cybersecurity-trends-for-2024