What Makes a Human Risk Management Platform Effective in 2026
Feb 20

Missing title
The question for modern HRM is no longer whether employees completed training, but whether their everyday decisions reduce or amplify organisational risk. Human risk surfaces in routine moments: approving a request under time pressure, trusting a familiar identity, or following established workflows when nothing appears unusual. With around 95% of data breaches rooted in human actions, effective HRM requires a dedicated capability to identify, measure, and reduce behavioural risk at the individual level, rather than simply delivering awareness at scale.
In 2026, the most effective Human Risk Management platforms are distinguished not by the amount of content they deliver, but by their ability to measure behaviour, detect patterns of decision failure, and intervene at the point where risk appears. This analysis evaluates HRM platforms through that behavioural lens, outlining the capabilities that separate basic awareness systems from behaviour-driven risk management.
How human risk emerges under pressure
You probably believe that most employees already know the rules. They don’t click strange links, don’t reuse passwords, and always report anything suspicious. Yet incidents continue to happen, not because people are unaware, but because real work rarely looks like a training slide. Decisions are made while juggling deadlines, responding to authority, or clearing inboxes at speed, and in those moments, behaviour quietly takes over from intention.
This is why the conversation around human risk has shifted. Instead of treating breaches as isolated “user mistakes,” researchers increasingly focus on how behaviour emerges from usability, context, and organisational pressure. The problem is no longer just what people know, but how they act when conditions are messy and time is short.
Much of this shift is rooted in the work of Dr Angela Sasse, whose research in human-centred security showed that systems designed against people tend to fail in practice. When controls feel slow, confusing, or misaligned with real work, employees adapt their behaviour to stay productive, and those adaptations often introduce risk.
There are several core ideas that shape this perspective:
Human-centred security prioritises behaviour over compliance
Human-centred security starts from a simple idea: usability shapes behaviour. When security controls interrupt work, people adapt to get their jobs done, often through shortcuts and workarounds. Dr Sasse’s research shows that systems designed without human needs in mind consistently produce insecure behaviour, even when policies are clear
Traditional awareness training fails to address motivation
Dr Sasse’s work demonstrates that awareness alone rarely changes behaviour. Employees often know the “right” action but choose differently when motivation, confidence, or perceived relevance is low. Training that focuses on recall ignores attitudes, intent, and perceived friction, which are the real drivers of behaviour in daily work.
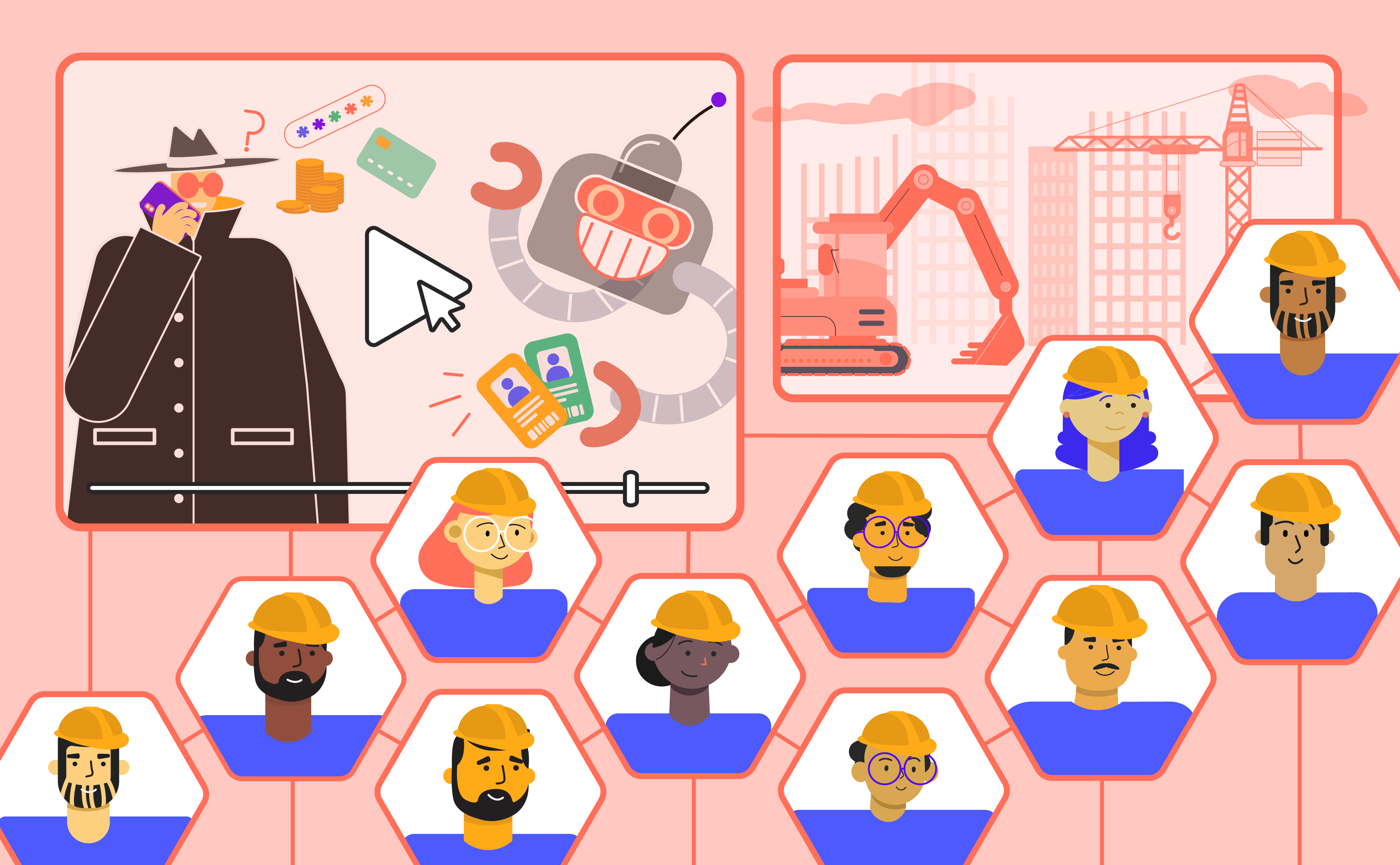
People are not homogeneous, and risk is unevenly distributed
Human risk varies widely across individuals. Some users are cautious, others are impulsive; some trust systems, others resist them. Treating the workforce as a single risk group hides these differences. Behavioural segmentation provides far more actionable insight than one-size-fits-all training or role-based assumptions
Emotional response strongly influences secure behaviour
Security decisions are emotional as well as rational. Affective security, which means how people feel about controls and guidance, influences whether secure habits stick. Frustration, anxiety, or mistrust can lead to avoidance or bypassing, while systems that feel supportive are more likely to be followed consistently.
Real work conditions shape security choices
Security decisions are made under time pressure, cognitive load, and workflow constraints. Research in human-centred security shows that people rely on habit and automation when busy, not policy recall. Controls that assume ideal conditions fail to reflect how decisions are actually made in the workplace.
Behavioural models make human risk measurable
Models like the Behavioural Security Grid, developed by Dr Sasse and her team at UCL, translate behavioural science into measurable insight. Rather than relying on simple click metrics or compliance checkboxes, the grid maps users along two core axes: risk understanding (how well someone recognises and perceives security risk) and affective security (how positively or negatively they respond emotionally to security guidance and policies). By combining these dimensions into 16 distinct segments - from enthusiastic Champions to disengaged Abdicators, and from cautious responders to habitual Rule Breakers - the grid surfaces patterns of behaviour that standard awareness metrics miss.
For example, someone may understand threats well but feel frustrated or blocked by controls, while another might feel confident but lack awareness of specific risks. These differences help explain why two people can face the same situation and respond very differently in practice.
Behavioural profiles correlate with real security outcomes
Research shows that behavioural tendencies, such as impulsivity, disengagement, or overconfidence, correlate with higher incident rates. Risk clusters around behaviour patterns rather than job title or seniority, making behaviour a stronger predictor of exposure than traditional organisational attributes.
More recent research has tried to model human risk in a more structured way, rather than treating incidents as isolated mistakes. One such effort is a framework called MORPHEUS, which stands for Multidimensional Framework for Modeling, Measuring, and Mitigating Human Factors in Cybersecurity, developed to explain how different human factors combine to shape security behaviour.
Instead of blaming single bad choices, it models risk as the interaction of more than 50 cognitive, emotional, behavioural, and organisational factors that influence how people act in security-critical situations. These include pressures such as stress, urgency, fatigue, cognitive overload, trust in authority, habit, and overconfidence, which often align to push people toward automatic rather than reflective decision-making.
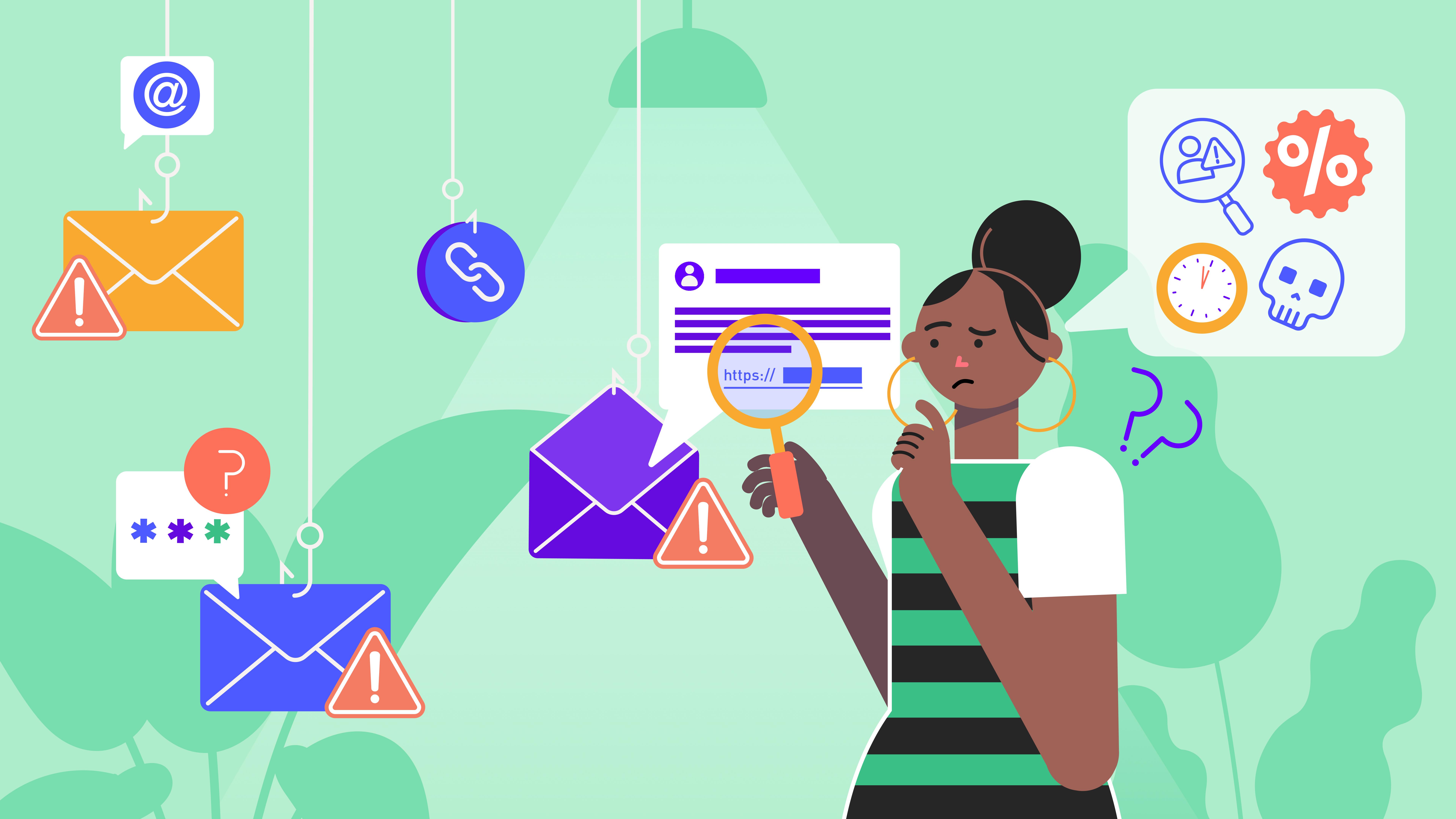
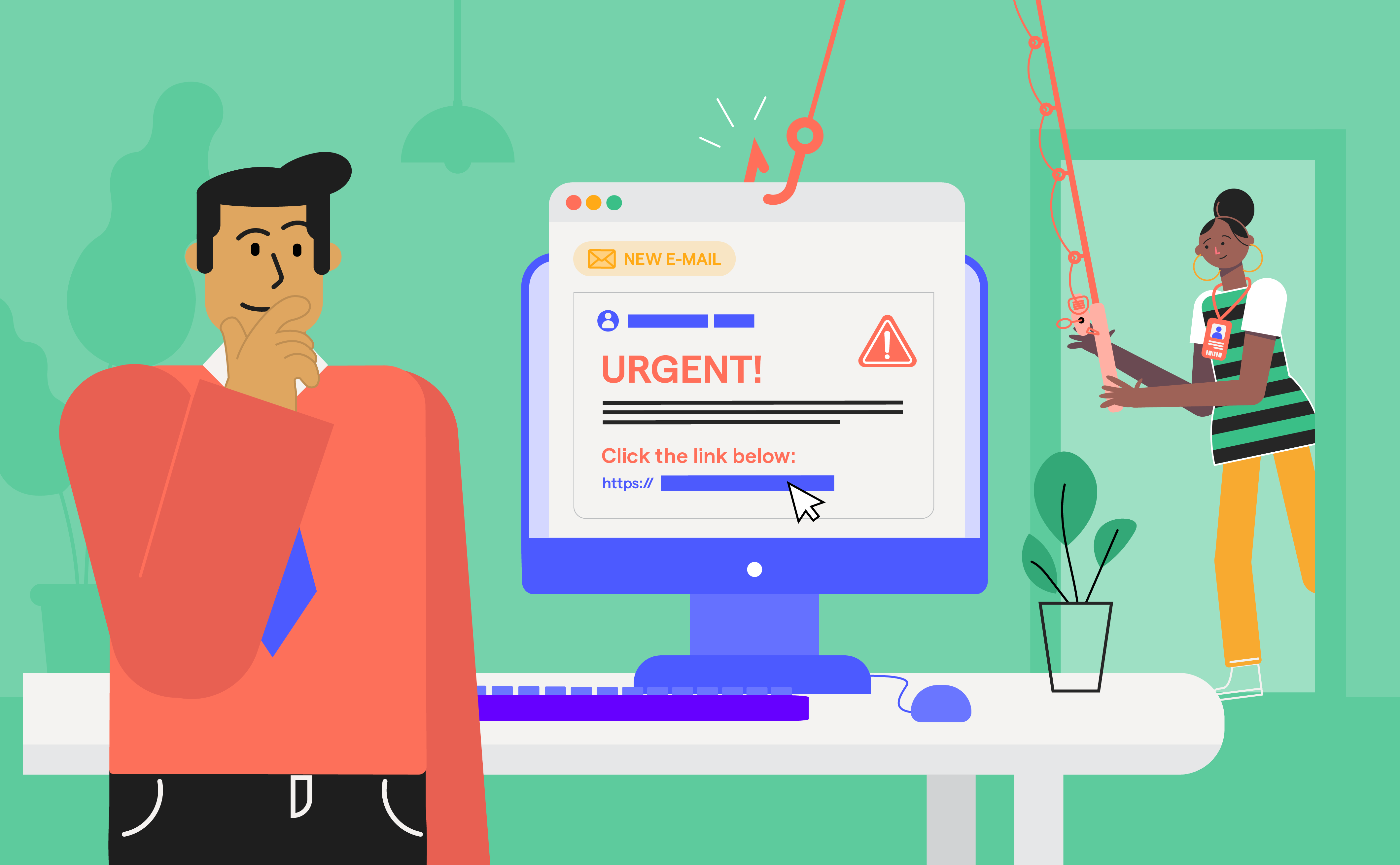
Why traditional security awareness and phishing simulation hit a behavioural ceiling
Traditional security awareness training and phishing simulations often focus on whether employees can recognise a crafted suspicious email, but research shows that this approach misses the deeper human factors that drive real-world risk. Traditional phishing simulations focus on whether a user recognises a malicious artefact. Behavioural research shows the greater risk lies elsewhere: how people respond to legitimate-looking requests embedded inside normal workflow. Authority cues, routine language, and workflow familiarity rarely trigger classic phishing signals, yet they strongly influence decision speed and verification behaviour - signals that SAT platforms do not measure.
Think about this: your colleague rushes to meet a deadline and approves a financial request which has been framed in familiar language and appearing to come from a senior manager. Such risk often surfaces without a malicious link. Approval requests framed as routine business, sent through familiar channels, may never register as “phishing” and these predictive risk signals remain invisible to traditional phishing metrics.
Similarly, someday you might hesitate to report an unusual message because it looks like it has been sent from your office's internal team and comes under social pressure to avoid false alarms. Traditional tests measure only reporting rates or click rates, but they can’t detect hesitation, uncertainty, or social influence, factors identified in human factor research as key drivers of susceptibility.
What human risk management really measures
HRM focuses on measuring behaviour that creates or reduces risk, rather than tracking training completion or awareness alone. This is where HRM shifts the question from what did people learn? to what did people actually do?
Instead of relying on periodic assessments, HRM platforms collect behavioural signals continuously and relate them to outcomes, building risk profiles at both the individual and group level. In practice, behaviour is measured as a pattern over time by observing how users act across repeated situations. HRM identifies risk by observing how consistently users apply judgment across repeated situations, rather than analysing isolated incidents.
So what kinds of behavioural signals can HRM platforms actually track?
Vulnerability behaviours (likelihood of error): Actions that show exposure to manipulation or routine risk-taking, such as repeated phishing clicks, credential submission, or policy bypassing. Behavioural research links these patterns to habit, trust cues, and cognitive overload rather than lack of knowledge.
Resilience behaviours (defensive action): How people respond when something feels wrong, measured through reporting rate and speed of response. Studies show that early reporting and interruption significantly reduce impact and attacker dwell time, making response behaviour a key indicator of real resilience.
Culture and repetition patterns (habit formation): Stable behaviour over time, such as repeated risky actions by the same users or voluntary engagement with security tasks. Human-centred security research shows that risk is not evenly distributed and often clusters around consistent behavioural tendencies.
To connect these behaviours to organisational exposure, HRM platforms use composite Human Risk Indicators, which combine vulnerability behaviours, resilience actions, and contextual factors into dynamic risk scores. Behavioural frameworks such as MORPHEUS support a pattern-based approach to human risk, validating composite indicators over single-event metrics.
Various research suggests that behaviour is most likely to change when feedback is tied to real situations rather than abstract rules. Sasse’s work argues that reducing friction and cognitive load in security processes is more effective than increasing instruction alone, while behavioural studies show that repeated contextual feedback helps shift habits over time.
These behavioural indicators form the basis on which HRM platforms can be meaningfully evaluated. If HRM is defined by how it measures behaviour, then the next question becomes how we judge whether a platform does this well.
The evaluation framework for modern HRM platforms
To be considered best in class, a modern Human Risk Management (HRM) platform must be evaluated on how effectively it reduces human-driven risk. And therefore, evaluation focuses on how platforms transform training activity into measurable behavioural risk signals.
What distinguishes modern HRM platforms in 2026 is how these elements are operationalised: whether simulations and training produce behavioural data, whether that data is interpreted in context, and whether insights translate into timely intervention. Evaluation, therefore, shifts from activity metrics, such as course completion and click rates, to evidence of behavioural change, risk prioritisation, and sustained impact over time.
1. Behavioural Signal Capture & Analytics
Modern HRM platforms are evaluated on whether they can capture real user behaviour in real time, such as how people respond to suspicious messages, how quickly they report issues, or whether they repeatedly bypass controls. These behavioural signals are then converted into dynamic risk indicators that reflect actual decision patterns rather than static knowledge.
A real-world example of this type of risk occurred when a senior US government cybersecurity official uploaded sensitive internal documents into a public AI chatbot for convenience, triggering internal security reviews. No phishing or malware was involved - the risk came purely from a human decision under time pressure. A modern HRM platform would treat this as a behavioural risk signal, not just a policy breach.
2. Adaptive & Personalised Training
Modern HRM platforms are assessed on whether training adapts to how individuals actually behave, rather than delivering identical content to everyone. This includes personalised simulations and coaching based on behavioural risk profiles, job roles, and past actions, as well as context-aware nudges triggered at the moment risky behaviour occurs.
For example, employees across healthcare and government agencies have been found using public AI tools to summarise sensitive data, despite clear policies forbidding it. The risky action is similar, but the motivation differs - speed, workload, or lack of alternatives. Adaptive HRM platforms respond differently to these behaviours, providing targeted guidance instead of repeating generic awareness modules.
3. Risk Visibility & Context Integration
HRM platforms are also judged on whether they combine behaviour with business and identity context, rather than analysing actions in isolation. This includes correlating behaviour across email, endpoints, identity systems, and collaboration tools, and factoring role and access level into risk scoring.
4. Attack Realism vs Decision Realism
In 2026, HRM platforms will be evaluated less on how realistic simulated attacks look and more on whether they measure decision-making under ambiguity and stress. High-fidelity phishing, vishing, and deepfake simulations still matter, but platforms are expected to assess how users behave when situations are unclear, internal-looking, or routine.
The “Signalgate” case involved senior officials inadvertently disclosing sensitive military operational details in an encrypted messaging app, illustrating how governance gaps and human misuse can create significant risk even without external attacks.
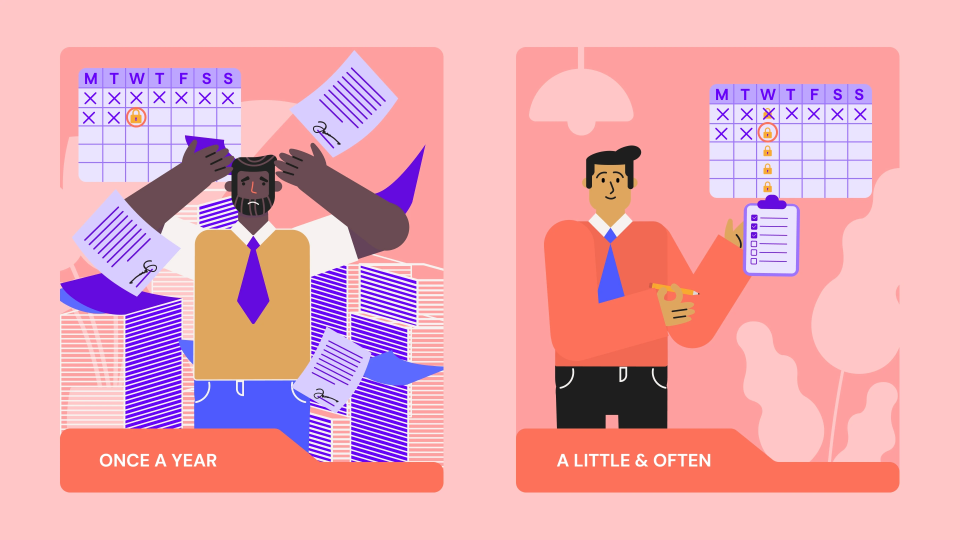
5. Continuous Risk Reassessment & Outcome Tracking
Finally, modern HRM platforms are evaluated on whether they treat human risk as dynamic, not static. This means reassessing behavioural risk metrics continuously, tracking trends over time, and detecting emerging clusters of risky behaviour rather than relying on annual snapshots.
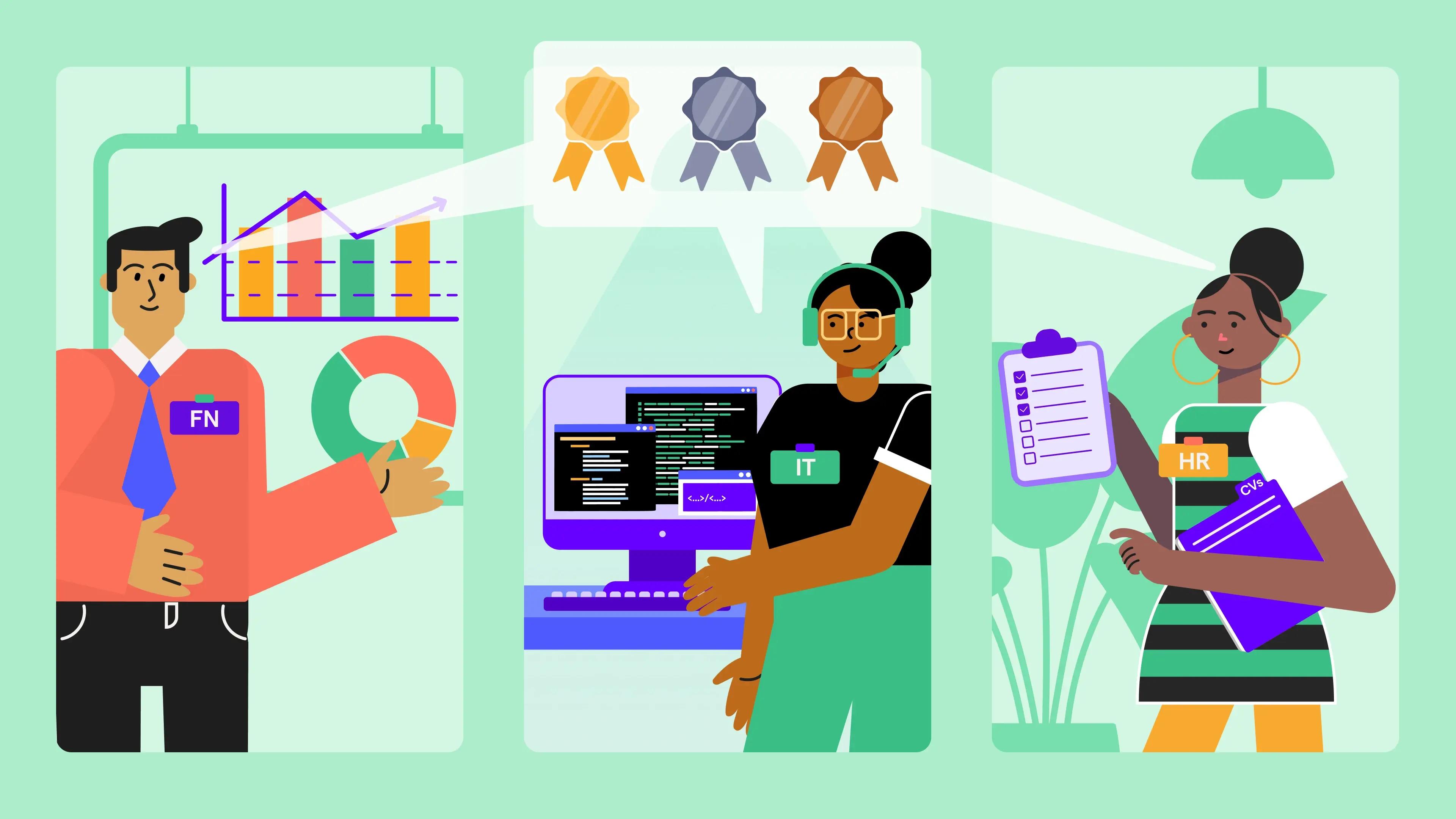
Best HRM Platforms in 2026 (Comparison)
To understand how these ideas translate into real platforms, let’s look at how leading Human Risk Management vendors in 2026 differ in what they measure, how they intervene, and who they are built for. The comparison below highlights how each platform approaches user behaviour, risk reduction, and practical deployment.
| Vendor | User Behaviour Measurement | Primary Focus | Key Technology / Feature | Best Suited For |
|---|---|---|---|---|
| OutThink | ⭐⭐⭐⭐⭐ | Human risk behaviour & adaptive HRM | AI-powered human risk management, real-time risk scoring & adaptive phishing/training based on behaviour | Enterprise & technical teams seeking deep, behaviour-driven insight and predictive risk reduction |
| KnowBe4 | ⭐⭐⭐⭐ | Human risk management + awareness | HRM+ platform with AI-driven simulated phishing, training library & defense agents | Global enterprises need a wide suite with strong training content and anti-phishing integration |
| Hoxhunt | ⭐⭐⭐ | Behavioural engagement & adaptive learning | Gamified phishing sims, behavioural analytics & adaptive risk nudges | Enterprises focused on engagement-driven behaviour change and culture-led security resilience |
| Guardey | ⭐⭐⭐ | Habit formation & engagement | Microlearning, challenge-driven storylines & gamified experiences | SMBs / teams wanting a lightweight, engaging platform (less enterprise behavioural analytics) |
| Usecure | ⭐⭐⭐ | MSP-friendly automated HRM | uLearn auto-enrol training, phishing tests, policy manager & breach indicators | MSPs and IT teams looking for easy deployment, automation & compliance reporting |
| Arctic Wolf | ⭐⭐⭐ | Managed security services & awareness | Managed Security Awareness that pairs microlearning with phishing simulations & SOC expertise | Large enterprises wanting integrated security ops + awareness & managed delivery |
| Phished | ⭐⭐ | Automated phishing & risk scoring | Behavioural Risk Score (BRS) and automated continuous simulations (not fully HRM-native) | Teams needing an automated, scalable phishing + training platform |
| Proofpoint | ⭐⭐⭐⭐ | Broad threat protection & HRM integration | Nexus AI with threat intel + user behaviour analytics and phishing simulations | Fortune 100 / global corps requiring a complete, integrated security stack |
OutThink
OutThink is designed around a simple but powerful premise: human risk is driven by behaviour, not knowledge gaps. Instead of measuring people by whether they pass training, OutThink models how they actually make decisions under pressure and uses that insight to predict, prioritise, and reduce risk over time. Its platform is built to operationalise behavioural science inside security operations, turning user behaviour into a measurable and manageable risk domain.
Why OutThink stands out in HRM:
- Behavioural segmentation based on risk understanding and emotional alignment, not just click outcomes
- Real-time human risk scoring driven by observed decisions across phishing, reporting, and policy-related behaviour
- Adaptive simulations and training mapped to behavioural profiles rather than roles alone
- Designed to surface who is risky, why they are risky, and what intervention will work, enabling predictive risk reduction
- Best suited for enterprises that want true behaviour-led Human Risk Management, not awareness programmes relabelled as HRM
KnowBe4
KnowBe4 offers one of the most widely adopted security awareness and human risk platforms, combining phishing simulations, training content, and behavioural risk indicators at enterprise scale. Its approach centres on improving awareness coverage while layering in behavioural insights derived from user interactions with simulated threats.
Key HRM strengths:
- Extensive phishing simulation capabilities across email-based attack scenarios
- Large and frequently updated training content library covering compliance, social engineering, and emerging threats
- SmartRisk™ Agent and user risk scoring to identify higher-risk users based on phishing interactions
- Strong scalability and administrative controls for large, globally distributed workforces
Hoxhunt
Hoxhunt focuses on behaviour change through engagement, using gamification and adaptive learning techniques to influence how users respond to security situations over time. Rather than static training, it prioritises sustained participation and motivation as drivers of safer behaviour.
Key HRM strengths:
- Gamified phishing simulations designed to encourage active participation
- Adaptive learning paths that evolve based on individual user responses
- Strong emphasis on positive reinforcement and reporting behaviour
- AI-generated content variations to prevent fatigue and pattern recognition
- Behaviour-focused dashboards highlighting engagement and response trends
Guardey
Guardey approaches human risk from a habit-formation perspective, using short, frequent interactions to reinforce secure behaviour. The platform relies on simplicity and storytelling to make security concepts easier to absorb during everyday work.
Key HRM strengths:
- Narrative-driven microlearning experiences
- Gamified challenges that reinforce repetition and recall
- Regular, low-friction touchpoints rather than long training sessions
- Focus on embedding security into daily routines
- Visual progress tracking to support continued engagement
Usecure
Usecure provides an automated human risk and security awareness platform designed to reduce administrative overhead while maintaining consistent coverage. It combines training, phishing simulation, and policy management within a unified workflow.
Key HRM strengths:
- Automated user onboarding and recurring training cycles
- Phishing simulations linked to simplified behavioural risk indicators
- Integrated policy distribution, acknowledgement, and tracking
- Centralised dashboards for visibility across users and risk levels
- Reporting aligned to compliance and audit needs
Arctic Wolf
Arctic Wolf incorporates security awareness and human risk into a broader managed security operations model. Human behaviour insights are contextualised alongside detection, response, and monitoring activities.
Key HRM strengths:
- Managed phishing simulation and awareness programmes
- Human risk data aligned with SOC monitoring and threat response
- Continuous guidance delivered as part of an ongoing security service
- Integration between user behaviour signals and incident handling
- Emphasis on operational outcomes rather than standalone training
Phished
Phished concentrates on continuous phishing exposure measurement, using automation to test and score user behaviour at scale. Its platform is designed to surface behavioural trends through repeated interaction rather than periodic assessments.
Key HRM strengths:
- Always-on phishing simulations with minimal manual setup
- Behavioural Risk Score (BRS) based on user interaction patterns
- Automated campaign orchestration across the organisation
- Focus on trend-based exposure measurement
- Simple dashboards highlighting behavioural shifts over time
Proofpoint
Proofpoint embeds human risk management within its broader enterprise threat protection ecosystem. Behavioural signals are enriched by threat intelligence and technical security telemetry to provide context-aware insight into user risk.
Key HRM strengths:
- Human risk analytics powered by Nexus AI
- Phishing simulations informed by real-world threat intelligence
- Correlation of user behaviour with email and identity threats
- Integration across email security, DLP, and identity protection
- Enterprise-scale reporting aligned with security operations
The real future of human risk
The future of human risk management is not about reacting after something goes wrong, but about recognising risk while it is still forming. Instead of waiting for a bad click or a policy breach, HRM platforms begin to surface early warning signs such as repeated near-misses, rushed decisions, or growing reliance on habit and authority. These signals appear long before an incident does, shifting human risk from something that is investigated after the fact to something that can be managed in advance.
Risk scores also evolve. They stop being occasional check-ins and become living indicators that update continuously based on real employee behaviour. Their purpose is no longer just to describe exposure, but to guide action. When risk rises, the response moves beyond “do more training” and focuses on fixing the reason behind the behaviour itself, whether that is workload pressure, unclear workflows, or friction in secure processes.
Support becomes situational rather than delayed. Instead of arriving weeks later in a course, it shows up at the moment of decision, helping employees pause, verify, and choose more safely. Over time, human risk data even begins to shape technical controls, influencing when extra approval or authentication is needed based on how people actually behave.
Training tells you what to know. Risk reveals what you do. The difference defines resilience.
Sources
- https://www.upguard.com/blog/human-factors-in-cybersecurity
- https://arxiv.org/abs/2512.18303
- https://www.mdpi.com/2079-8954/13/4/280
- https://www.researchgate.net/publication/386747842_Human_Factor_in_Cybersecurity_Behavioral_Insights_into_Phishing_and_Social_Engineering_Attacks
- https://dl.acm.org/doi/10.1145/3613904.3642432
- https://www.paccsresearch.org.uk/blog/effective-computer-security-human-centred-approach/
- https://www.csoonline.com/article/4124320/cisa-chief-uploaded-sensitive-government-files-to-public-chatgpt.html
- https://www.insurancejournal.com/news/international/2025/11/21/848596.htm
- https://kymatio.com/
- https://www.infosecinstitute.com/resources/security-awareness/beyond-awareness-human-risk-management/
- https://papers.ssrn.com/sol3/papers.cfm?abstract_id=5481946
- https://www.tech-channels.com/hubfs/KnowBe4/Q22025/Critical-Capabilities-Evaluating-HRM-WP_EN-US.pdf
- https://outthink.io/community/thought-leadership/CHRM-report/#the-behavioral-segmentation-grid-for-human-risk-management
- https://outthink.io/community/thought-leadership/blog/human-risk-management-the-eight-dimensions-of-secure-behavior-segmentation/
- https://www.sciencedirect.com/science/article/pii/S1877050924026383