The Best Cofense Alternatives & Competitors in 2026
Dec 22

Discover the best human risk management platform - OutThink.
Introduction
Phishing continues to be the most effective initial access vector for cyberattacks-powering credential theft, ransomware, and business email compromise (BEC). Despite advances in technical defenses, attackers increasingly succeed by exploiting human behavior rather than system vulnerabilities.
Platforms like Cofense have played an important role in helping organizations respond to phishing threats after delivery. With strong user-reported phishing workflows and SOC-centric triage, Cofense has long been trusted by security teams focused on detection and containment.
However, as security programs mature, many organizations are reassessing whether post-delivery response alone is sufficient. Today’s security leaders are looking beyond phishing triage toward Human Risk Management (HRM) platforms that reduce risky behavior before incidents escalate.
In this article, we explore five leading alternatives to Cofense in 2026; focusing on platforms that extend beyond phishing response into behavior change, adaptive learning, and measurable human risk reduction. We’ll compare their strengths, ideal use cases, and how they differ from Cofense’s incident-response-first model.
Why Consider Alternatives to Cofense?
Cofense is widely respected for its strength in phishing detection and response. Its focus on user-reported phishing, post-delivery triage, and SOC workflows makes it a strong choice for organizations prioritizing rapid containment of email threats.
That said, when evaluated through a broader human risk management lens, some limitations emerge:
1. Post-incident focus rather than prevention
Cofense excels after a phish lands, mobilizes users to report, triages on the go, and finally quarantines. That’s valuable, but prevention‑first programs aim to reducethe incidence ofhigh‑risk events , not just clean up faster.
Why this is critical:
- Social‑engineering clicks happen within minutes, which compresses response windows; halving dwell time is good, but preventing potentially riskybehaviour is even better.
- Gartner guidance for security leaders emphasizes measuring behavior change (not just compliance completion) and driving secure decisions in the flow of work; a prevention‑oriented posture that reduces incident rates over time.
This means that Cofense’s post‑delivery containment remains valuable, but if your KPI is fewer risky behaviors and fewer incidents across channels, you need pre‑emptive, behavior‑shaping controls and just‑in‑time coaching rather than a fast response/cleanup.
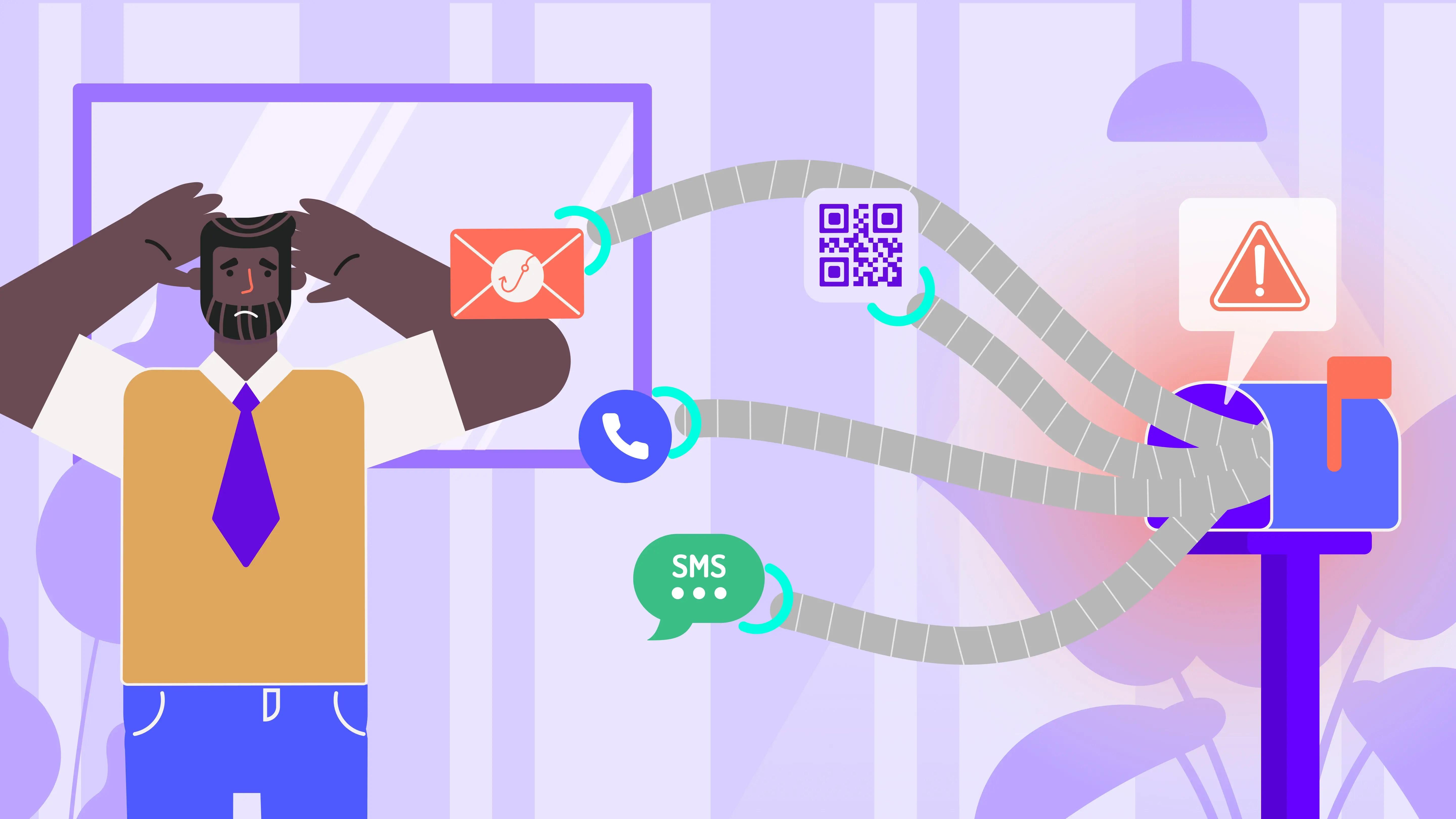
2. Limited training adaptation
Cofense PhishMe is primarily described as email phishing simulations with campaign analytics. Public buyer guides and profiles focus on simulated emails and reporting, not on automatic learning thattriggers from live, non‑email risk signals (e.g., risky file sharing, identity events in collaboration tools).
HRM‑native approaches tie training to real behaviors as they happen (the “nudge in the moment”), so people learn at the exact point of risk and the organization can measure behavior change, not just course completion. That alignment to real‑world signals is what improves prevention metrics. While Cofense has recently announced Smart Reinforcement (AI‑assisted, adaptive reinforcement) which is a positive step, public coverage still centers on email‑centric workflows.
3. Usability, Customization & Integration Gaps
a) Customization limits (scenario content, certificates, reporting layouts).
- Verified reviews praise Cofense overall but mention friction shaping industry‑specific or threat‑specific scenarios and generating the exact reports teams want without extra work/APIs.
- When you can’t tailor lures to your users’ real exposure (e.g., logistics invoices, specific SaaS apps, regional brands), you test the wrong behaviors, which weakens resilience measurement and blinds you to pockets of risk. Similarly, if reporting isn’t flexible, CISOs struggle to prove risk reduction to the board and auditors.
b) Reporting friction
- If behavior metrics (who clicked, who reported, who improved, where, and why) aren’t readily visible, you can’t target interventions or demonstrate behavior change-the metric that modern HRM programs (and Gartner) ask leaders to track.
c) Integration gaps for a multi‑channel world
- Cofense integrates with email and core security tooling; however, buyers still describe silos or extra glue work when they want one view that merges email, collaboration, identity, and endpoint signals.
- Social engineering now hits SMS, voice, and collaboration apps; If your training/telemetry remain email‑bound, you miss where peopleactually get duped and your resilience score is inflated
Overall, if your goal is faster phishing cleanup, Cofense is a strong fit. If your goal is measurable reduction of human risk across channels-with real‑time, behavior‑triggered coaching and analytics that link behaviors to risk reduction-you may need to augmentCofense with HRM‑native capabilities or evaluate platforms built formulti‑channel prevention and resilience, not just post‑delivery response.
What Enterprises Really Want: The 7 Non-Negotiable Criteria for Choosing a “Better” HRM or SAT Platform
Before comparing vendors or alternatives, it’s critical to define what “better” really means in the context of a modern HRM or SAT platform. Based on an analysis of the top 100 enterprise RFPs we reviewed in the past year, these seven key criteria (listed in order of importance and RFP weight factor) consistently rank as the most important for security teams:
Research Highlights:
- Data Management ranked #1 with about 25% average weight
- Behaviour Change and Engagement both scored above 20% by average weight on most items
- Integration Depth and Adaptive Training are now table stakes
1) Data Management
Enterprises demand transparency on how user data is collected, stored, and ultimately destroyed. Compliance with GDPR, CCPA, PDPA, and ISO standards is non-negotiable. This category carries the highest weight because privacy, audit readiness, and governance are under intense scrutiny. Platforms that demonstrate strong security controls and clear retention policies earn trust; and with regulators tightening, this is now a board-level concern.
2) User Engagement
Training can’t feel like a checkbox exercise. Buyers want platforms that make learning engaging through gamification (leaderboards, challenges), nudges via Teams or email, and multi-language support for global teams. Engagement analytics help identify low performers and drive targeted interventions. Vendors leading in this space use behavioral science and gamified UX to build security culture, not just awareness.
3) Behaviour Change
Awareness alone isn’t enough; organizations want proof of real-world impact. Platforms should measure actual security behaviors, diagnose why risky actions occur, and automatically deliver tailored training when needed. Continuous nudges keep security top-of-mind. The industry is shifting from static courses to adaptive, behavior-driven HRM, where success is measured by improved risk posture, not completion rates.
4) Technology Fit
Deployment must be frictionless. Buyers expect seamless integration with productivity and security stacks like Microsoft 365, Gmail, SIEM/SOAR, and support for SSO via AD or Okta. Mobile and browser compatibility are essential for hybrid workforces. Integration depth is now table stakes; HRM platforms should embed into daily workflows and security operations without disruption.
5) Phishing Simulations
Phishing remains the top attack vector, so simulations need to be realistic and adaptive. Enterprises prefer AI-driven templates powered by live threat intelligence and OSINT, not static libraries. They also expect root-cause analysis and personalized remediation for users who fail. Leaders are moving toward alert-triggered training loops, aligning phishing defense with SOC workflows for measurable impact.
6) Reporting & Insights
CISOs need more than participation stats; they need actionable intelligence. RFPs call for dashboards that show risk scores, engagement metrics, and APIs for custom reporting. Visibility at user, team, and organizational levels is critical. Platforms that link training outcomes to measurable risk reduction are gaining traction as security becomes a board-level KPI.
7) Human Risk Intelligence
Modern HRM platforms are expected to provide dynamic, predictive risk scoring based on behavioral signals, phishing results, and training history. Buyers want transparency: users should see their score and get guidance to improve, while security teams gain predictive insights for proactive intervention. This capability reflects the industry’s move toward behavioral analytics and adaptive security.
Top Cofense Alternatives (2026 Edition)
To help security leaders quickly assess the landscape, the table below summarizes how leading Cofense alternatives compare across human risk maturity and operational focus. A detailed breakdown of each platform follows.
Quick Comparison Table
| Vendor | Core Strength | HRM Maturity | Best For |
|---|---|---|---|
| OutThink | Real-time HRM with AI-driven Human Risk Index (HRI); Microsoft-native integrations | Very High | Predictive risk reduction; M365-centric security teams |
| CybSafe | Research-backed HRM; behavior insights; governance alignment | Medium | Enterprises prioritizing academic rigor and compliance frameworks |
| Hoxhunt | Engagement & gamification; adaptive phishing at scale | High | Culture-led programs focused on report-rate lift and habit formation |
| SoSafe | Behavioral-science microlearning; privacy-first HRM OS | Medium–High | Multinationals with localization and privacy requirements |
| Right-Hand Security | Alert-to-training automation; SOC-aligned risk analytics | High | Teams prioritizing SIEM/SOAR workflows and faster MTTD/MTTR |
1. OutThink
OutThink is an HRM-first platform built to treat human risk as a real-time security signal rather than a byproduct of phishing campaigns. Instead of anchoring training to reporting workflows, OutThink continuously adapts learning and nudges based on live user behavior and security telemetry.
Key Differentiators
- OutThink delivers behavior-triggered coaching directly inside everyday tools like Teams, Outlook, and Gmail, ensuring interventions happen in the flow of work.
- Its Human Risk Index (HRI) aggregates behavioral, technical, and contextual signals into a single, actionable risk score across users, teams, and departments.
- Deep Microsoft ecosystem alignment enables automation at scale while reducing operational friction for security teams.
Why It Outperforms Cofense
Cofense excels at phishing detection and triage, but OutThink extends beyond response into prediction and prevention. By using real-time signals to trigger adaptive interventions, OutThink reduces risky behavior before incidents escalate, rather than training users only after a phishing event.
Ideal For
Mid-market and/or large enterprise organizations seeking measurable behavior change, predictive risk visibility, and Microsoft-native HRM automation.
2. CybSafe
CybSafe frames human risk management through academic rigor and governance alignment, positioning HRM as a structured, evidence-based discipline.
Key Differentiators
- Its approach draws on behavioral research and formal models to diagnose why risky behaviors occur, linking training outcomes to governance and compliance reporting.
- Dashboards emphasize insight and accountability rather than operational response metrics.
Why It Outperforms Cofense
Compared to Cofense’s operational focus on phishing response, CybSafe provides stronger support for policy alignment, governance frameworks, and audit-ready reporting grounded in behavioral research.
Ideal For
Enterprises seeking compliance-aligned HRM with academic credibility and structured governance oversight.
3. Hoxhunt
Hoxhunt approaches human risk through motivation and habit formation, focusing on sustained engagement rather than episodic training moments. Its platform is designed to keep security top-of-mind through continuous micro-interactions.
Key Differentiators
- Gamified phishing challenges, progression mechanics, and real-time nudges drive participation across large workforces.
- Learning is delivered through familiar channels like Teams, Slack, and email, helping embed secure behaviors into daily routines.
- Strong multilingual support enables consistent engagement across global deployments.
Why It Outperforms Cofense
Where Cofense centers on phishing response workflows, Hoxhunt focuses on long-term behavior change. Organizations looking to increase reporting rates and build durable security habits often find Hoxhunt’s culture-first model more effective than response-anchored training.
Ideal For
Organizations prioritizing employee engagement, culture change, and global participation over SOC-driven automation.
4. Right-Hand Security
Right-Hand Security is built for security teams that want human risk remediation to operate with the same rigor and automation as technical controls.
Key Differentiators
- The platform connects alert ingestion directly to targeted training and risk score updates, creating closed-loop workflows across SIEM, SOAR, and DLP environments.
- Granular analytics provide visibility into risk trends at the user, team, and organizational level, helping SOCs reduce manual follow-ups and accelerate response times.
Why It Outperforms Cofense
Cofense focuses primarily on phishing reporting and triage, while Right-Hand Security automates the full response lifecycle. This makes it better suited for environments where reducing MTTD/MTTR and SOC workload is a top priority.
Ideal For
Mature SOC teams seeking automation, operational efficiency, and signal-driven human risk remediation.
5. SoSafe
SoSafe positions itself as a Human Risk OS that blends behavioral science, modern UX, and AI assistance to drive organization-wide behavior change.
Key Differentiators
- Short, role-relevant learning journeys, gamification, and an AI assistant (“Sofie”) support high adoption without overwhelming users.
- A privacy-first design and strong localization capabilities make SoSafe particularly attractive for multinational enterprises operating under strict regulatory regimes.
Why It Outperforms Cofense
SoSafe emphasizes proactive behavior shaping rather than reactive training tied to phishing events. For organizations balancing engagement, privacy, and scalability, this approach often delivers broader workforce impact than Cofense’s phishing-centric model.
Ideal For
Multinationals seeking fast rollout, high participation, and privacy-conscious HRM programs.
How to Choose the Right Cofense Alternative
Choosing a Cofense alternative isn’t about replacing phishing detection - it’s about deciding how broadly you want to manage human risk.
- If your priority is predictive behavior change and continuous risk reduction, HRM-native platforms like OutThink provide deeper visibility and real-time intervention beyond phishing workflows.
- If engagement and reporting rates are your biggest challenge, Hoxhunt or SoSafe offer culture-led approaches that embed learning into daily work.
- For SOC-driven environments, platforms like Right-Hand Security align human risk remediation directly with SIEM and SOAR workflows, reducing operational burden.
- Organizations prioritizing governance, compliance, and research-backed programs may find CybSafe orOutThink better aligned with their reporting and policy needs.
Before committing, run a structured 90-day pilot with clear KPIs such as reporting rates, failure-rate reduction, MTTD/MTTR improvement, and risk-score movement. Use this period to confirm that dashboards reflect genuine behavior change - not just training completion - and assess the vendor’s roadmap for long-term HRM maturity.
Conclusion
Cofense remains a strong choice for phishing detection and response, but as human behavior becomes the primary attack surface, many organizations are expanding beyond response-centric models.
The center of gravity in enterprise security has shifted: human behavior is now the dominant attack surface, and programs that only clean up after the phish will inevitably plateau. The organizations winning in 2026 are the ones that prevent risky actions before they happen, measure risk at user/team/org levels, and coach in the flow of work across email and collaboration channels.
Platforms like OutThink,Hoxhunt, Right-Hand Security,SoSafe, andCybSafe represent the next phase of human risk management- each optimized for different maturity levels and operational priorities. If you’re still optimizing primarily for inbox cleanup, you’re optimizing the symptom, not the cause. Make 2026 the year you replatform to HRM, measure the delta in human risk, and let SOC automation handle the noise.