5 Alternatives to Adaptive Security: Choosing a Modern Human Risk Management Platform in 2026
Dec 22

Discover a smarter approach to human risk management - OutThink today.
Introduction
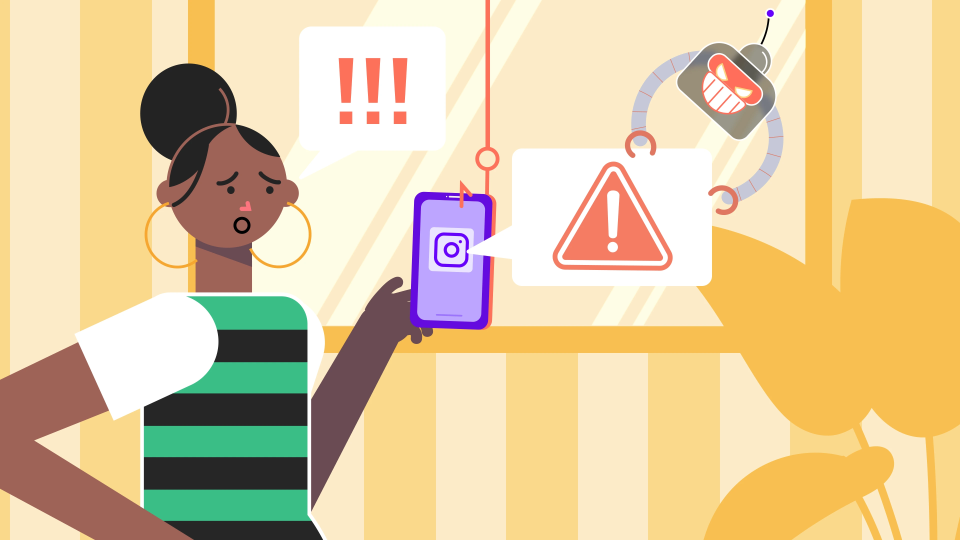
Human-centric attacks are no longer limited to phishing emails. From deep-fake-enabled vishing and SMS fraud to highly targeted social engineering, attackers are increasingly exploiting human behavior rather than technical vulnerabilities.
Platforms like Adaptive Security have emerged in response to this shift, modernizing security awareness with AI-generated content and highly realistic, multi-channel simulations designed to prepare employees for today’s threat landscape. By personalizing content, generating lifelike scenarios, and adapting difficulty based on user responses, AI-driven training platforms have significantly improved awareness and preparedness against modern attack techniques.
However, as security programs mature, many organizations begin to question whether improving awareness alone is enough. Increasingly, leaders are asking whether security platforms should simply deliver better training - or actively reduce human risk as it occurs. This reflects a broader industry transition from AI-driven training to risk-driven Human Risk Management (HRM). While training-first platforms focus on how learning is delivered, HRM platforms focus on when and why intervention happens. They measure risk at individual, team, and organizational levels, closing the loop between detection, response, and prevention.
In this article, we explore five leading alternatives to Adaptive Security in 2026 - focusing on platforms that extend beyond AI-driven simulations toward real-time intervention, operational alignment, and measurable behavior change. We’ll compare their strengths, ideal use cases, and how they differ from Adaptive Security’s training-first model, helping you choose the right fit for your organization.
Why Consider Alternatives to Adaptive Security?
Adaptive Security is widely recognized for advancing security awareness through AI-generated content and highly realistic attack simulations by its use of deepfake‑style media, smishing and vishing scenarios. For many organizations, this represents a major step up from legacy SAT platforms. However, as human risk management evolves, some teams find limitations when moving from training effectiveness to real-world risk reduction:
- Training-first rather than alert-first
Adaptive Security’s interventions are primarily driven by simulations and learning campaigns. While effective for preparedness, risky actions detected in live environments do not always trigger immediate, personalized intervention. Public reviews frequently describe Adaptive Security as a sophisticated training and simulation platform rather than a fully operational HRM system with continuous risk scoring and signal-driven automation. - Executive-centric focus
Adaptive Security places notable emphasis on OSINT‑driven scenarios and executive‑focused features such as deepfake simulations and exposure monitoring. While these capabilities are valuable for high‑risk leadership and corporate teams, the platform’s marketing and examples are geared toward white‑collar environments, which may feel less aligned for organizations with considerable frontline or blue‑collar workforces. - Limited SOC-native depth
While Adaptive Security offers standard workplace integrations, enterprises with Microsoft‑centric or SOC‑driven security operations generally expect tighter alert pipelines, richer contextual telemetry, and frictionless orchestration. This expectation is reflected in the broader market landscape: solutions that surface as “Adaptive Security Alternatives” on Gartner, for example, commonly specialize in deep behavioral analytics and SOC‑grade integrations, underscoring what customers in these environments value most.
For organizations prioritizing measurable reductions in human risk - not just improved awareness - these factors often prompt a search for alternatives.
The 7 Non-Negotiable Criteria for Choosing a “Better” HRM or SAT Platform
Before comparing vendors or alternatives, it’s critical to define what “better” really means in the context of a modern HRM or SAT platform. Based on an analysis of the top 100 enterprise RFPs we reviewed in the past year, these seven key criteria (listed in order of importance and RFP weight factor) consistently rank as the most important for security teams:
Research Highlights:
- Data Management ranked #1 with about 25% average weight
- Behaviour Change and Engagement both scored above 20% by average weight on most items
- Integration Depth and Adaptive Training are now table stakes
1) Data Management
Enterprises demand transparency on how user data is collected, stored, and ultimately destroyed. Compliance with GDPR, CCPA, PDPA, and ISO standards is non-negotiable. This category carries the highest weight because privacy, audit readiness, and governance are under intense scrutiny. Platforms that demonstrate strong security controls and clear retention policies earn trust; and with regulators tightening, this is now a board-level concern.
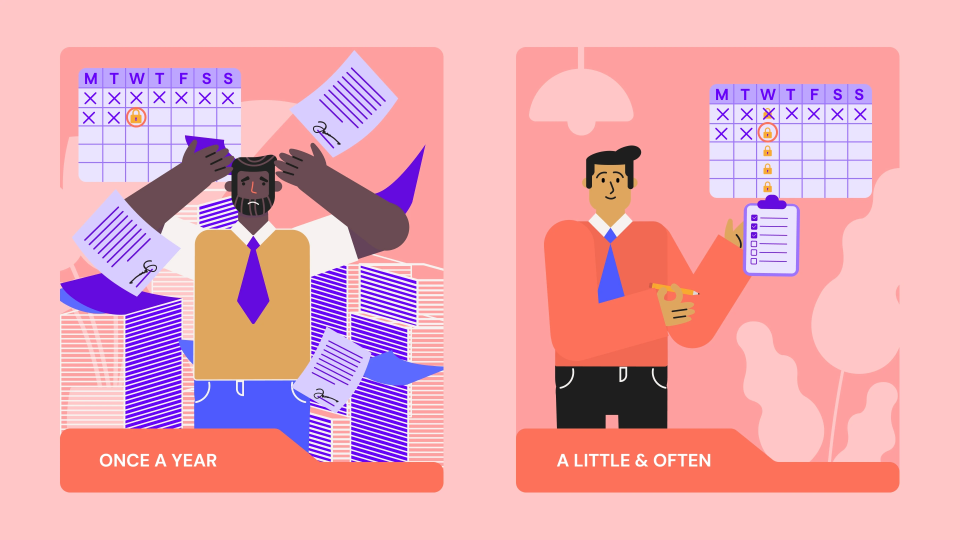
2) User Engagement
Training can’t feel like a checkbox exercise. Buyers want platforms that make learning engaging through gamification (leaderboards, challenges), nudges via Teams or email, and multi-language support for global teams. Engagement analytics help identify low performers and drive targeted interventions. Vendors leading in this space use behavioral science and gamified UX to build security culture, not just awareness.
3) Behaviour Change
Awareness alone isn’t enough; organizations want proof of real-world impact. Platforms should measure actual security behaviors, diagnose why risky actions occur, and automatically deliver tailored training when needed. Continuous nudges keep security top-of-mind. The industry is shifting from static courses to adaptive, behavior-driven HRM, where success is measured by improved risk posture, not completion rates.
4) Technology Fit
Deployment must be frictionless. Buyers expect seamless integration with productivity and security stacks like Microsoft 365, Gmail, SIEM/SOAR, and support for SSO via AD or Okta. Mobile and browser compatibility are essential for hybrid workforces. Integration depth is now table stakes; HRM platforms should embed into daily workflows and security operations without disruption.
5) Phishing Simulations
Phishing remains the top attack vector, so simulations need to be realistic and adaptive. Enterprises prefer AI-driven templates powered by live threat intelligence and OSINT, not static libraries. They also expect root-cause analysis and personalized remediation for users who fail. Leaders are moving toward alert-triggered training loops, aligning phishing defense with SOC workflows for measurable impact.
6) Reporting & Insights
CISOs need more than participation stats; they need actionable intelligence. RFPs call for dashboards that show risk scores, engagement metrics, and APIs for custom reporting. Visibility at user, team, and organizational levels is critical. Platforms that link training outcomes to measurable risk reduction are gaining traction as security becomes a board-level KPI.
7) Human Risk Intelligence
Modern HRM platforms are expected to provide dynamic, predictive risk scoring based on behavioral signals, phishing results, and training history. Buyers want transparency: users should see their score and get guidance to improve, while security teams gain predictive insights for proactive intervention. This capability reflects the industry’s move toward behavioral analytics and adaptive security.
Top Adaptive Security Alternatives (2026 Edition)
To help security leaders evaluate their options, the table below summarizes how leading Adaptive Security alternatives compare across human risk maturity and primary focus areas. A detailed breakdown for each platform follows.
Quick Comparison Table
| Vendor | Core Strength | HRM Maturity | Best For |
|---|---|---|---|
| OutThink | Risk-driven HRM | Very High | Real-time, behavior-based risk reduction |
| Hoxhunt | Engagement & culture | Medium–High | Participation and security culture |
| Right-Hand Security | Automation-first HRM | High | SOC-aligned risk automation |
| SoSafe | UX-led HRM | Medium | Fast rollout and adoption |
| Proofpoint | Stack consolidation | Medium | Proofpoint-centric enterprises |
1. OutThink - Best Overall Adaptive Security Alternative
AI-powered Adaptive Human Risk Management platform for real-time, behavior-driven security.
OutThink is frequently shortlisted by organizations seeking to move beyond AI-driven training toward continuous human risk reduction. Rather than leading with content realism, OutThink is built around live security signals, risk scoring, and automated intervention.
Key Differentiators
- Real-time, alert-triggered intervention: Learning nudges and micro-training activate based on actual security alerts and risky behavior - not just simulations or schedules.
- Human Risk Index (HRI): A transparent, measurable risk model providing visibility at individual, team, and organizational levels.
- SOC-aligned workflows: Designed to reduce human-related incidents without adding manual burden to security teams.
- Microsoft-native depth: Deep integrations with Microsoft Defender, Graph API, Outlook, Teams, and Microsoft 365.
- Federated risk visibility: Ability to ingest data from third-party simulation tools into a unified risk score.
Where It Outperforms Adaptive Security
- Alert-driven interventions vs simulation-led learning
- Risk scoring based on live behavior vs training performance metrics
- HRM-first architecture vs AI-driven awareness design
Ideal For
Microsoft-heavy enterprises and SOC-led security teams seeking measurable behavior change, reduced incident volume, and real-time visibility into human risk.
2. Hoxhunt
Hoxhunt approaches human risk from a behavioral and motivational perspective, with a strong emphasis on sustained engagement, participation, and security culture across large and distributed workforces. By focusing on motivation and participation, Hoxhunt aims to make security behaviors feel routine and achievable rather than episodic or compliance-driven.
Key Differentiators
- Highly gamified user experience: Hoxhunt uses points, progression, and challenges to encourage ongoing participation, helping prevent the fatigue that often accompanies traditional awareness programs. This approach supports long-term engagement rather than one-off campaign success.
- Personalized nudges across collaboration tools: Targeted nudges are delivered through everyday platforms such as Microsoft Teams, Slack, and email, allowing learning moments to occur naturally within daily workflows rather than in separate training environments.
- Strong multilingual support: With extensive language coverage, Hoxhunt is well suited for global organizations that need consistent engagement across regions, cultures, and geographies.
Why It Outperforms Adaptive Security
Hoxhunt tends to outperform Adaptive Security in environments where engagement and participation are the primary success metrics. While Adaptive Security emphasizes highly realistic simulations and AI-driven scenarios, Hoxhunt focuses on habit formation and long-term culture change. Organizations that value steady participation across the entire workforce often find this approach more effective than realism-heavy training that may resonate most strongly with specific user groups.
Ideal For
Organizations prioritizing employee engagement, security culture development, and global adoption-particularly those seeking consistent participation across large workforces rather than deep SOC-level automation or alert-driven interventions.
3. Right-Hand Security
Right-Hand Security is designed for security teams that want human risk management to operate as part of day-to-day security operations, not as a parallel training program. Its value lies in reducing the manual effort required to follow up on human-driven alerts and ensuring that risky behavior is addressed immediately and consistently through automated workflows.
Key Differentiators
- End-to-end automation across the risk lifecycle: Alerts triggered by risky user behavior can automatically initiate targeted training or interventions, followed by immediate updates to risk scores-removing the need for manual coordination between tools or teams.
- Deep integration with security operations tooling: Right-Hand Security connects directly with SIEM, SOAR, and DLP platforms, allowing human risk events to be managed alongside technical alerts within existing SOC workflows.
- Granular, role-based analytics: Security teams gain visibility into risk patterns at the user, team, and departmental levels, supporting more precise prioritization and operational decision-making.
Why It Outperforms Adaptive Security
Right-Hand Security outperforms Adaptive Security in environments where speed, automation, and operational alignment are more critical than training experience or simulation realism. While Adaptive Security focuses on improving awareness through advanced simulations, Right-Hand Security is optimized for acting on live signals, enabling security teams to respond to human risk as it emerges rather than after scheduled training cycles.
Ideal For
Mature SOC teams that prioritize efficiency, signal-driven response, and automated human risk remediation-particularly those seeking to manage human risk within existing security operations rather than through standalone awareness programs.
4. SoSafe
SoSafe positions itself as a Human Risk Operating System (HR OS) that blends behavioral science, modern user experience design, and AI-assisted learning. The platform is built to make security education feel intuitive and approachable, lowering friction for employees while supporting organization-wide behavior change.
Key Differentiators
- Intuitive, user-friendly design: SoSafe emphasizes simplicity and clarity, making it easy for employees to understand expectations and complete learning without fatigue or confusion.
- Gamified learning journeys: Structured, progressive journeys encourage ongoing participation and reinforce positive security habits rather than one-off training events.
- AI-assisted guidance: The built-in AI assistant, “Sofie,” helps guide users through learning paths, answer questions, and support consistent engagement across the workforce.
Why It Outperforms Adaptive Security
SoSafe outperforms Adaptive Security in environments where ease of deployment, employee experience, and sustained participation are more important than highly realistic or executive-focused simulations. SoSafe prioritizes accessibility and habit-building, making it easier for organizations to achieve broad adoption across diverse employee groups.
Ideal For
Enterprises seeking fast deployment, high participation rates, and a modern learning experience-especially those looking to establish or mature human risk programs with a strong focus on usability and employee engagement, alongside evolving HRM capabilities.
5. Proofpoint
Proofpoint typically enters Human Risk Management conversations through security stack consolidation rather than as a standalone awareness or training platform. Its strength lies in embedding human risk signals into broader enterprise security operations, particularly in organizations already using Proofpoint for email, data loss prevention, or insider threat protection.
Key Differentiators
- Deep security stack integration: Proofpoint connects awareness and user behavior insights with DLP, insider threat management, and SaaS security, enabling human risk to be viewed alongside data and identity risk.
- Enterprise-grade reporting and compliance tooling: The platform offers robust dashboards, audit-ready reporting, and governance capabilities designed to meet the needs of highly regulated environments.
- Strong insider risk workflows: Proofpoint excels at correlating user behavior with sensitive data access and policy violations, supporting investigation and response workflows within security operations teams.
Why It Outperforms Adaptive Security
Proofpoint outperforms Adaptive Security in organizations where operational integration and centralized security management are more important than training realism or simulation-led programs. By embedding awareness and human risk insights directly into enterprise security workflows, Proofpoint extends beyond Adaptive Security’s training-centric model and enables security teams to act on human risk within the same systems they already use to manage technical threats.
Ideal For
Large, complex enterprises that are already invested in the Proofpoint ecosystem and want to manage human risk as part of a unified, enterprise-wide security strategy rather than as a separate awareness initiative.
How to Choose the Right Adaptive Security Alternative
Choosing an Adaptive Security alternative isn’t about replacing AI-driven training - it’s about aligning your platform with how human risk is addressed.
- If your goal is training realism and executive threat exposure, Adaptive Security may remain sufficient.
- If your priority is measurable behavior change, platforms like OutThink,Hoxhunt, and Right-Hand Security focus on reducing risky actions over time.
- If your security team operates within SOC-driven workflows, integration depth matters. OutThink, Right-Hand Security, and Proofpoint allow human risk to be managed alongside technical risk.
- If employee engagement has been a challenge, platforms such as Hoxhunt,SoSafe, and OutThink embed learning into daily workflows through nudges and micro-interventions.
Before committing, run a structured 90-day pilot with clearly defined KPIs such as phishing reporting rates, failure reduction, time-to-contain (MTTD/MTTR), and overall risk score improvement. Use this period to validate whether dashboards and analytics reflect genuine behavioral change rather than simple course completion, and assess the vendor’s roadmap for long-term HRM maturity and scalability.
Conclusion
Adaptive Security represents a meaningful evolution in security awareness, particularly in preparing organizations for AI-enabled threats. However, as human risk becomes inseparable from operational security, training realism alone is no longer enough.
Platforms such as OutThink,Hoxhunt, Right-Hand Security,SoSafe, and Proofpoint reflect the industry’s shift toward behavior-driven, signal-aware Human Risk Management - each addressing different stages of security maturity.
For organizations seeking the most comprehensive, real-time approach to human risk reduction, OutThink stands out as the strongest Adaptive Security alternative.