The Email That Could Cost You Everything: Your Essential Guide to Recognizing Phishing in 2024
Oct 07
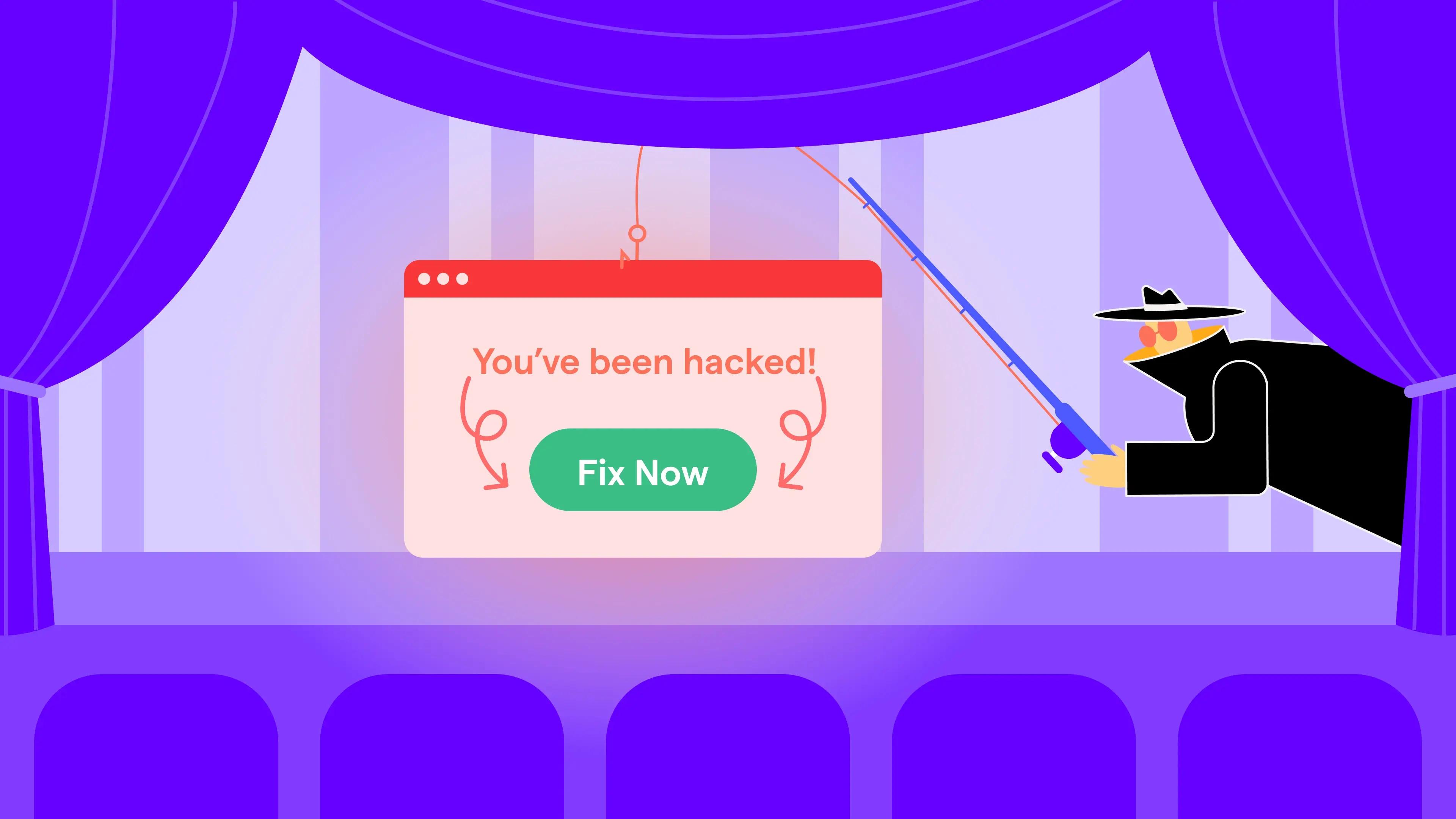
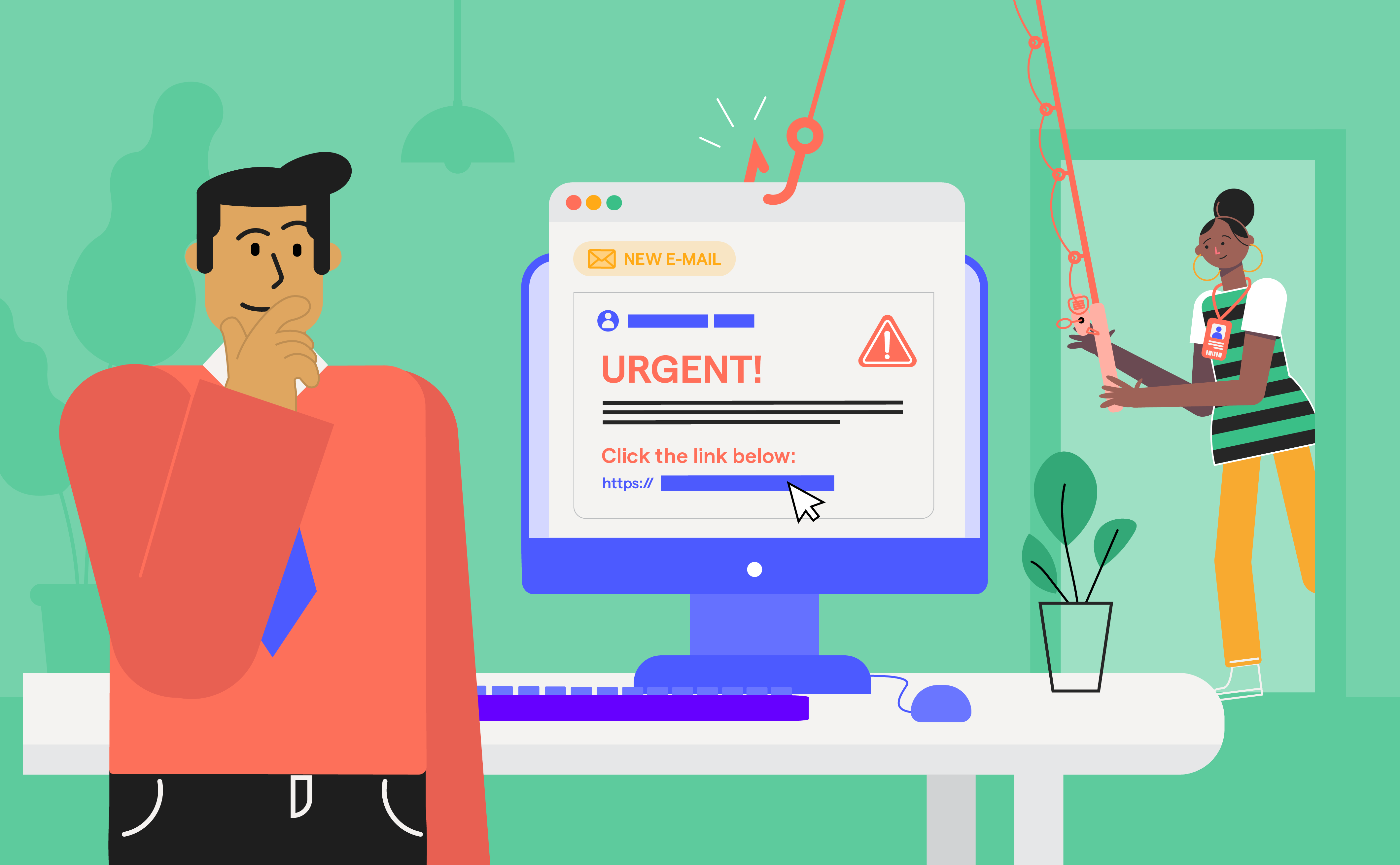
Experience OutThink
Picture this scenario: At 2:47 PM on a Tuesday, a marketing director clicks what appears to be a routine message from her bank. By 3:15 PM, the company's financial systems are locked by ransomware. The resulting damage includes $250,000 in recovery costs and three weeks of halted operations.
This illustrative example isn't unique - similar situations occur in offices worldwide every day. As we observe Cybersecurity Awareness Month 2024, CISA and the National Cybersecurity Alliance have made one thing crystal clear: recognizing and reporting phishing isn't just a security best practice, it's survival in our digital-first world.
The good news? This nightmare scenario could be prevented with knowledge anyone can learn in five minutes.
Phishing Today: Not Your Grandfather's Email Scam
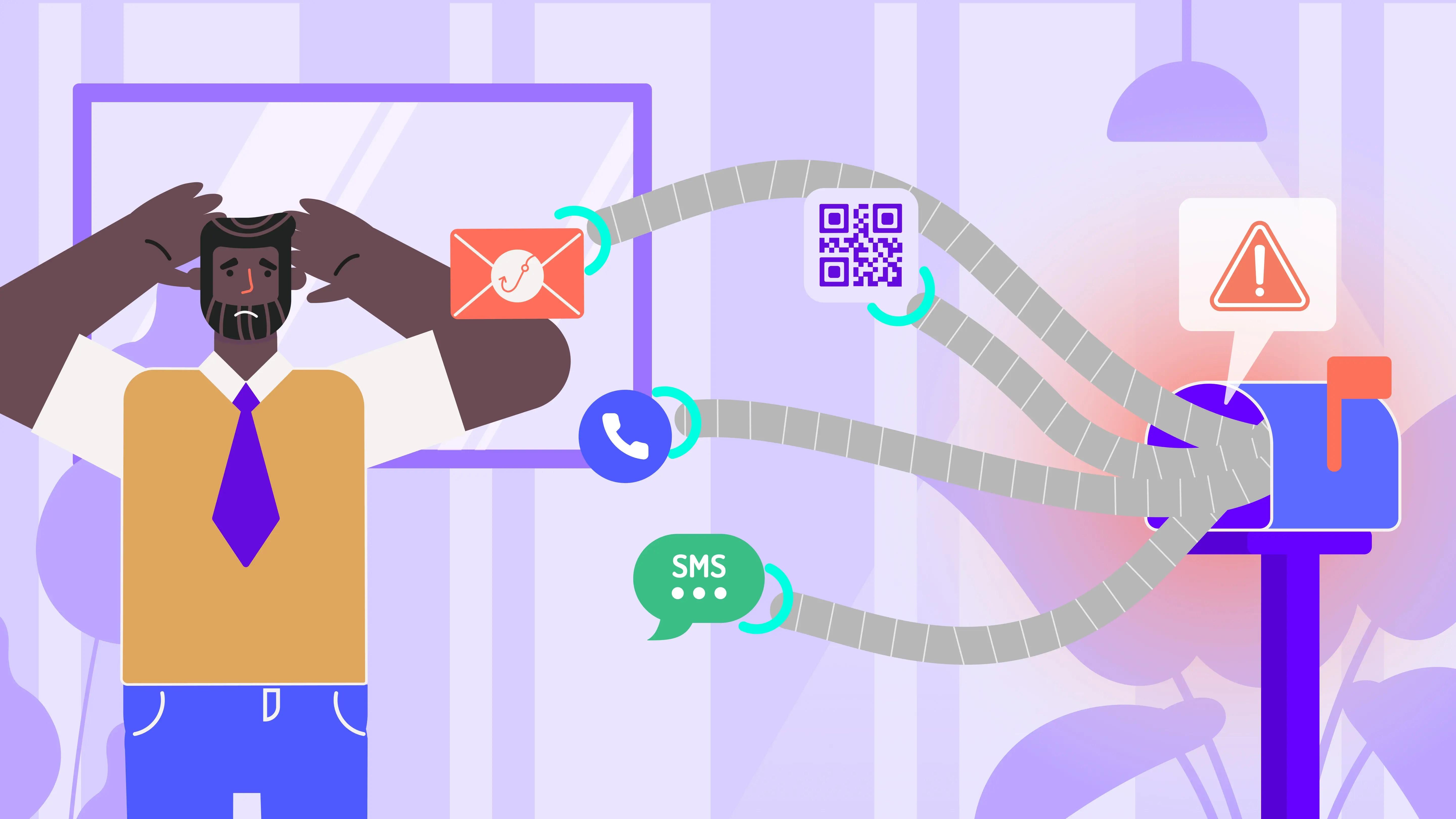
Modern cybercriminals don't just cast wide nets hoping to catch anyone. They research their targets on LinkedIn, craft emails that reference actual projects, and create fake websites so convincing that even IT professionals do double-takes.
The statistics paint a sobering picture: CISA reports that phishing remains the entry point for most successful cyberattacks. But here's what the statistics don't show: the human cost. The late nights fixing systems, the uncomfortable conversations with clients, the stress of wondering if customer data was compromised.
As CISA emphasizes, "If you suspect phishing, resist the urge to click any links or download attachments." This isn't just policy, it's your digital lifeline in a sea of increasingly convincing deception.
Why Traditional Security Training Falls Short (And What Actually Works)
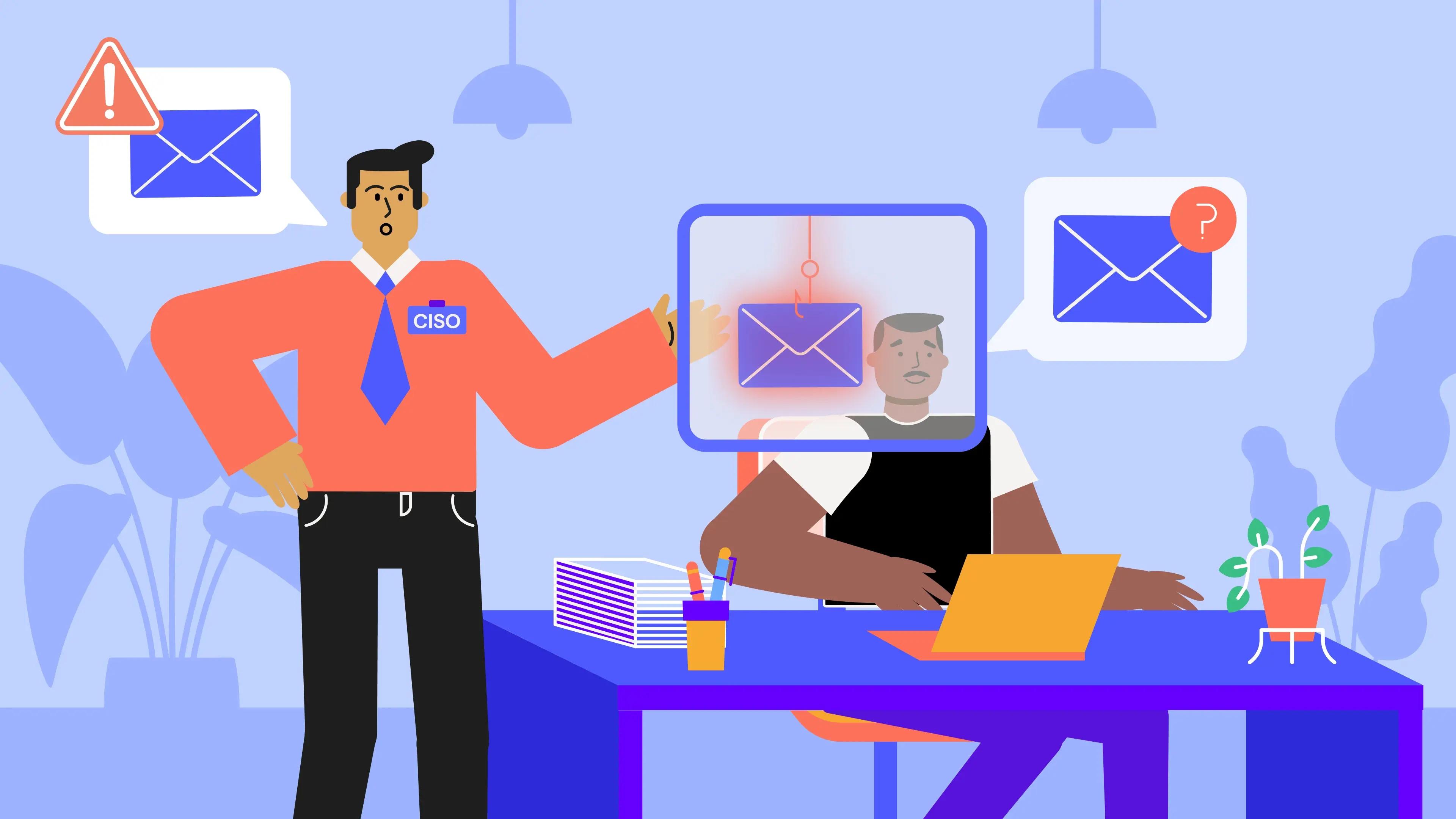
Consider this hypothetical analysis: A Fortune 500 CISO reviewing breach data discovers that employees who completed traditional phishing training were still falling victim to attacks at alarming rates. The realization: "We were teaching them what to look for, but not how to think about threats."
This insight highlights the need for a more sophisticated approach to phishing defense. Instead of treating employees as weak links to be fortified with rules, effective programs recognize them as intelligent humans who can become your strongest security allies - if you understand their psychology.
OutThink's phishing simulations don't just test knowledge; they analyze behavior patterns. When someone clicks a simulated phishing link, the best programs don't shame them - they understand why they clicked and tailor training to address that specific vulnerability.
Research consistently shows that context matters more than content. For example, a finance employee might be vulnerable to invoice phishing, while HR staff may fall for fake resume attachments. Generic training misses these crucial nuances.
This personalized approach transforms how organizations think about phishing defense, moving from fear-based compliance to genuine understanding and skill-building.
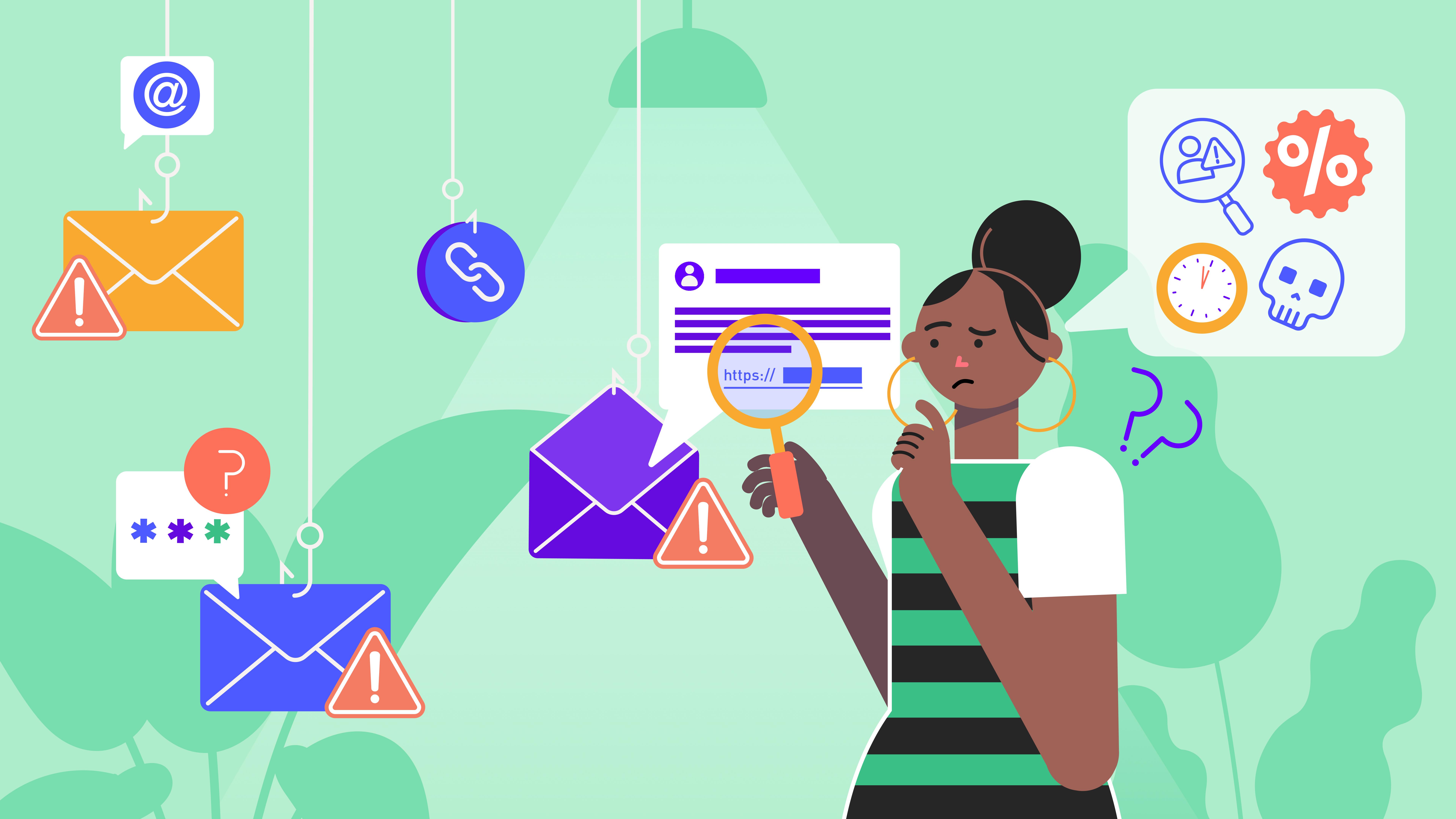
Your Phishing Detective Checklist: What Actually Works
Forget memorizing long lists of technical indicators. Here's what real security professionals look for when scanning their inboxes:
The "Gut Check" Method
Before analyzing any email technically, pause and ask: "Was I expecting this?" Often, your intuition catches what your logical mind misses.
The Three-Second Scan
The Sender Reality Check: Does "bank@mybank-security.com" really look right when you know your bank is "mybank.com"? Attackers count on you reading quickly.
The Emotion Test: Is this email trying to make you panic? Creating urgency ("Account closing in 24 hours!") or fear ("Suspicious activity detected!") are classic manipulation tactics.
The Link Preview: Hover before you click. That "Review Account" button might lead to a suspicious domain instead of your actual bank.
The Devil's in the Details
- Notice generic greetings? Real companies typically use your actual name, not "Dear Customer"
- Check for mismatched information - like a PayPal email discussing a Netflix charge
- Question unexpected attachments, especially if they're .zip files or executables
Remember: Modern phishing emails often have perfect grammar and professional design. Don't assume professionalism equals legitimacy.
Why Reporting Matters: You're Part of a Bigger Battle
Imagine this scenario: An office manager receives a suspicious email and chooses to report it rather than delete it. Unbeknownst to her, that same phishing email had been sent to all 200 employees. Her quick reporting allows IT to block the malicious domain before anyone else can fall victim.
This example illustrates why reporting phishing isn't just about protecting yourself - you're protecting colleagues who might be less suspicious or simply having a bad day. That innocent-looking "IT Security Update" email you report could be the same one targeting your distracted coworker dealing with a family emergency.
Here's the reporting reality: Most people don't report because they're embarrassed ("I should have known better") or worried about being seen as paranoid ("What if it's legitimate?"). But security teams consistently say they'd rather investigate 10 false alarms than miss one real threat.
CISA recommends reporting to both your internal IT team and external agencies like the FTC. This dual reporting helps not just your organization but contributes to national threat intelligence that protects everyone.
Modern security platforms make this easy with one-click reporting tools that remove the friction from doing the right thing. No lengthy forms, no technical knowledge required - just click, report, and get back to your day knowing you've made everyone safer.
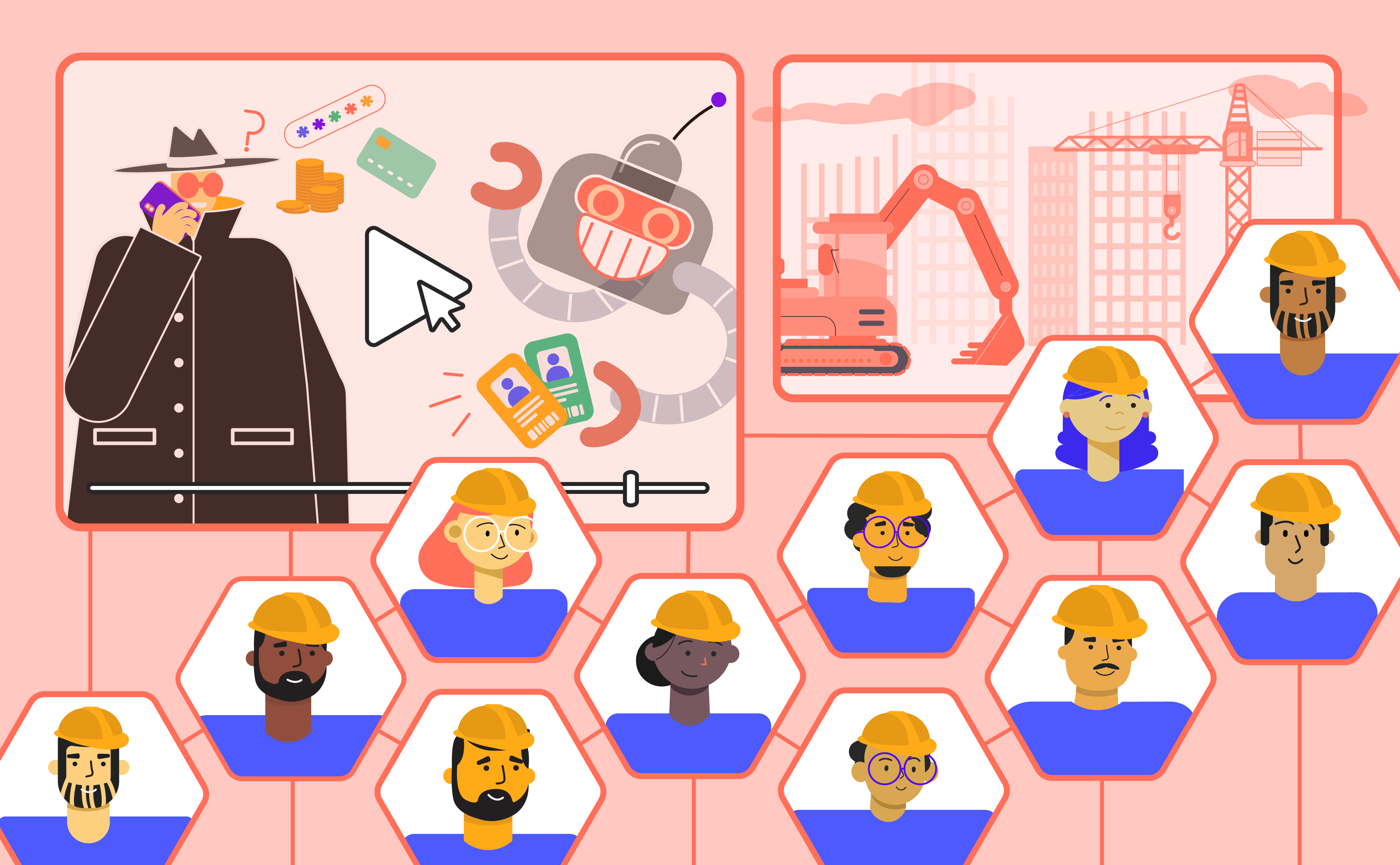
Learning by (Almost) Failing: Why Phishing Simulations Work
Consider this educational example: An engineering manager who prides himself on technical savvy receives a phishing simulation - a convincing "software update" notification. He clicks immediately.
Instead of shame or punishment, he receives immediate, personalized feedback explaining exactly why the email was designed to fool technical professionals like him. Three months later, when a real attack uses similar tactics, he spots it immediately and reports it to the security team.
This illustrates the power of hands-on learning in a safe environment. Effective simulations don't just test whether you can identify obvious phishing - they challenge you with the same sophisticated tactics real attackers use.
The behavioral insights gathered help organizations understand their unique vulnerabilities. Maybe your accounting team is particularly susceptible to fake invoice emails, or your executives need focused training on CEO fraud attempts. This intelligence transforms generic security awareness into targeted, effective education.
Most importantly, simulation participants report feeling more confident about their ability to spot real threats. Knowledge builds confidence, and confident employees are more likely to trust their instincts and report suspicious activity.
Clicked Before You Thought? Your Emergency Response Guide
First, breathe. Even cybersecurity professionals sometimes click malicious links. What matters is how quickly and effectively you respond.
If You Clicked a Link but Entered No Information
- Don't panic - you're likely still safe
- Close the browser tab immediately
- Report to your IT team with the email and website details
- Run a quick virus scan if you're feeling nervous
If You Entered Credentials
- Change your password immediately on the real service
- Enable MFA if you haven't already
- Check your account for any unauthorised activity
- Report to both IT and the legitimate service provider
If You Downloaded an Attachment
- Don't open it (if you haven't already)
- Disconnect from your network temporarily
- Run a full antivirus scan before reconnecting
- Contact IT immediately for guidance
The Golden Rule
When in doubt, report it. Your IT team would rather investigate 100 false alarms than deal with one successful attack. Modern reporting systems make this as simple as clicking a button - no judgment, no hassle, just protection for everyone.
Remember: Reporting doesn't make you the problem; it makes you part of the solution.
Your Role in the Fight Against Phishing
As one security professional noted: "I used to think phishing was an IT problem. Now I realize it's a business survival skill." This perspective is increasingly common. In our interconnected world, every click, every email decision, and every report contributes to our collective security.
This Cybersecurity Awareness Month, CISA and the National Cybersecurity Alliance aren't just asking you to be aware, they're asking you to be active. Phishing attacks succeed because they only need to fool one person, one time. But defensive success comes from every person, every time, choosing vigilance over convenience.
Effective security awareness programs prove that when we understand the psychology behind both attacks and defenses, we can build genuinely resilient organizations. The best platforms don't just train they transform security awareness from a compliance checkbox into a shared cultural value.
Take Action Today
- Forward this article to a colleague who needs to read it
- Check if your organization has phishing simulation training
- Report that suspicious email sitting in your folder right now
- Set a monthly reminder to review your team's phishing awareness
Together, we're not just recognizing and reporting phishing - we're building a more secure digital world, one informed decision at a time.
Quick Reference: Suspicious Email Checklist
Before clicking any link or attachment, ask yourself:
- Do I know this sender personally?
- Am I expecting this type of message?
- Does the tone match how this person/company usually communicates?
- Is there any pressure to act immediately?
- Do the links go where I expect them to go?
If you answered "no" to any question, report before interacting.
Take the time to educate your team on how to recognize and report phishing. With the right tools and training, everyone can contribute to a safer, more secure digital environment.