How Adaptive Security Awareness Training Drives Better Cybersecurity Outcomes: The Science
Mar 11

Missing title
Imagine you had the budget to hire an expert one-on-one cybersecurity tutor for every single person in your organization.
Would it be worth it?
The science of learning suggests that it would. For almost as long as we’ve been studying human learning, we’ve known that one-on-one tuition is by far the most effective form of education. A set of pivotal studies in the 1980s found that even compared with optimal group-learning conditions, personalized tuition generates outcomes two standard deviations better for the average student. Advances in our understanding of classroom education since the 80s have done little or nothing to erode this enormous gap.
If you’ve ever experienced one-to-one teaching or mentorship, you’ll have a strong intuition why this is. In an individual teacher-student relationship, every aspect of the learning experience can be customized to the learner’s needs, from pacing to content, teaching style, motivational methodology and more.
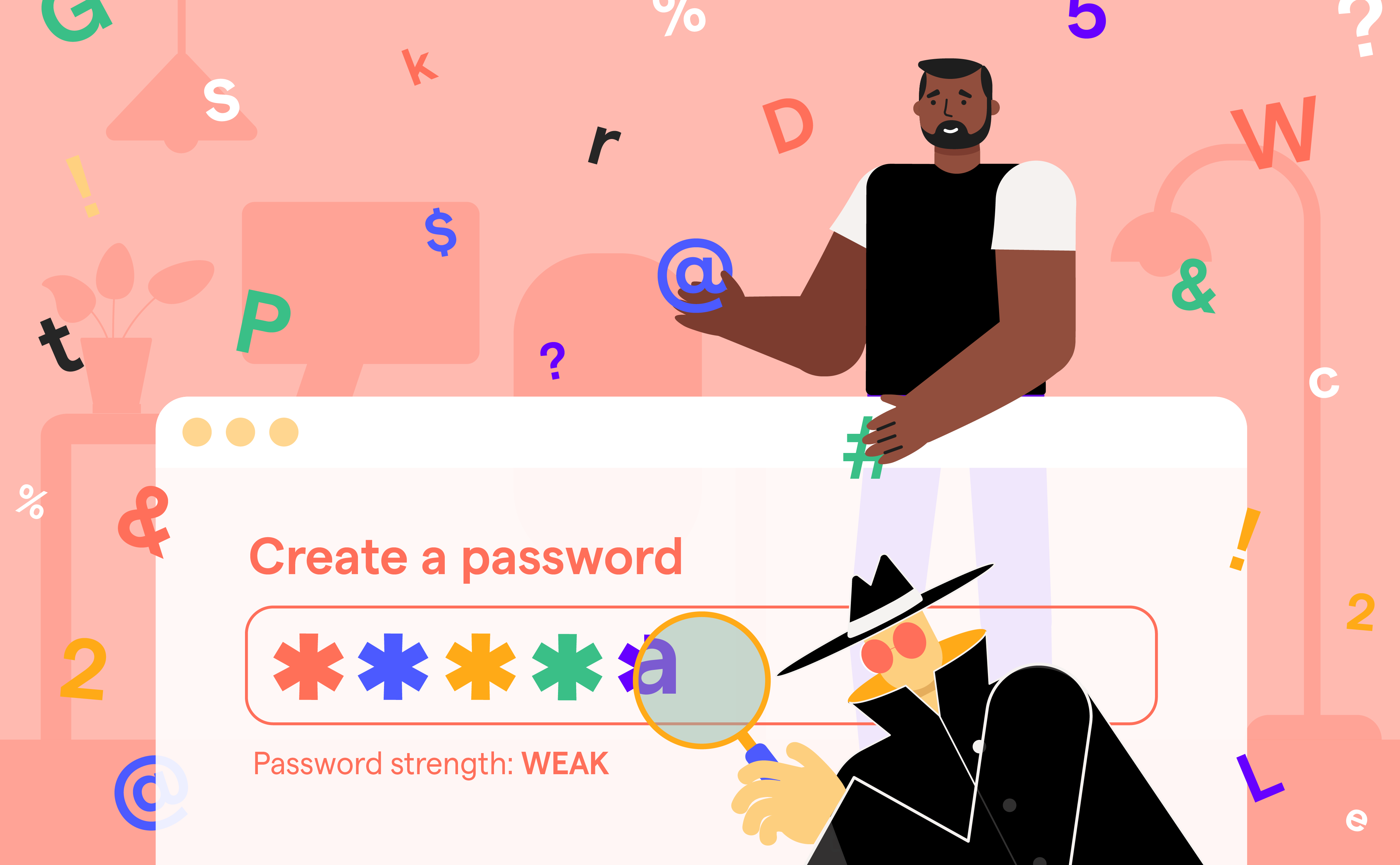
A student with a personal tutor need never be left behind, or insufficiently challenged, or forced to sit through material that isn’t relevant to her. Or, to put it in SAT terms: she can’t just click “next,” skip the video, and ask her colleague for the answers to the assessment quiz!
So of course personalized cybersecurity tuition would be more effective than traditional training, whether delivered online or in person. Unfortunately, no organization has the budget for it.
That’s where Adaptive SAT comes in.
What is Adaptive Security Awareness Training?
Given the strong evidence that personalized learning beats group learning every time, it’s not surprising that learning technologists’ Holy Grail is a computer-based learning experience which mimics personal tuition and can deliver some of the same benefits.
Adaptive training, or adaptive e-learning, is the most promising advance in this area. It deploys a range of technologies to create learning experiences which can “self-customize” to meet the individual needs of each learner.
We don’t have the space here to dive into the full range of possibilities opened up by adaptive e-learning, but a few quick examples should give a sense of the potential of this technology. Almost every aspect of digital training is potentially customizable, including content, format, presentation, interactivity, and language. So an adaptive training experience can automatically deploy finance-relevant content for learners who work in Accounts, or replace written text with diagrams for visual learners.
How Data Enhances Adaptive Security Awareness Training
The more data a training system can gather about learners, the more powerfully adaptive it becomes. For example, adaptive training which leads with questions designed to assess each learner’s current knowledge can then deploy only the content each learner actually needs, at the level of detail appropriate for them. Imagine how much that could cut down your organization’s time-in-training!
Historically, this adaptivity has largely been “designed”: that is, customization happens according to rules pre-determined by human educators. This approach already opens up a lot of potential for a single educator to build personalization into a training syllabus or program. However, it’s limited by the capacity of the educator. One person can only take so many variables into account when designing training content.
With the advent of machine learning, however, algorithmic adaptivity has become possible. This machine-mediated adaptivity can take into account a much larger array of learner data and make many more adjustments than would be feasible for a human educator. Modern AI Security Training Platforms leverage these capabilities to deliver truly personalized learning experiences at scale.
Why Human Oversight Augments Adaptive Security Awareness Training
This approach, while powerful, places restrictions on human oversight which are not currently acceptable in most training contexts. The technology is fast improving - and the culture of training is shifting to meet it - but for the time being the most effective adaptive training approaches combine elements of designed and algorithmic adaptivity, aiming for the best of both approaches.
Adaptive learning technology is in its infancy, but it has already proven effective. Studies have found that it is particularly effective for professional training, and for boosting engagement in learner populations.
These strengths make adaptive learning a powerful ally to cybersecurity awareness teams in the form of Adaptive Security Awareness Training.
How Does Adaptive SAT Change Cybersecurity Behaviors?
We all know that cybersecurity training frequently doesn’t engage users: people take the training, but simply don’t pay enough attention for it to stick. While a number of other factors affect training outcomes, this is widely agreed to be the current limiting factor for most awareness teams.
The challenge is: how can cybersecurity training be made more engaging? Until recently, the potential answers to this question have been frustratingly limited by what’s actually feasible. To take just one example: it’s technologically and organizationally feasible to switch from text to video-based training for all users; so these formats have frequently been compared, as if the key to “engagement” were simply a matter of the mode of content delivery.
While video-based training is indeed often found to be “more engaging,” it’s difficult to have much confidence in this data. For a start, video has usually been the “new” format, and novelty generates engagement—until it wears off. Secondly, as learning researchers have known for a long time, there are always going to be learners who prefer text (or audio, or interactive learning). Thirdly, there is evidence to suggest that while learners generally report a preference for video, they don’t actually retain more information from video than from text—and they likely retain less when the video is subtitled. Finally, in the absence of cues to engage actively with the material, video-based learning can be highly passive, which is known to be ineffective.
Adaptive Security Awareness Training Improves Learner Engagement With Cybersecurity
From these observations alone, we can already see how adaptive learning can overcome the limitations of the “delivery mode” approach to boosting engagement. Imagine cybersecurity training which monitors how much video a learner has seen, and delivers video content only when it will be welcomed as a novelty. Or training which delivers video to learners who learn more easily from video, but text to learners who prefer that format.
However, adaptive training offers a far more powerful antidote to disengagement than this. Studies suggest that disengagement is driven substantially by a sense that cybersecurity training is irrelevant to learners. Of course, we know that it’s not! But it’s not difficult to imagine how this perception arises. Of necessity, an organization-wide training program will include a lot of information that is largely or entirely irrelevant to any given individual user.
Most learners only need to encounter irrelevant information once or twice before they begin to feel that the whole training is simply not aimed at them.
Meet Your Users Where They Are With Adaptive Security Awareness Training
Adaptive Security Awareness Training offers a complete solution to this challenge. With sufficient data points about each learner, adaptive training can remove all the irrelevant content from each learner’s program. Furthermore, adaptive training can be customized to specific aspects of each learner’s role, making cybersecurity training more relevant than it has ever been.
If you could survey your organization to ask them whether they want either: more videos, more gamification, or shorter and more relevant training, which do you think they would choose?
Learn more about how to implement Adaptive Security Awareness Training by checking out the Adaptive Security Awareness Training playbook.