Domain Spoofing: The Cyber Trick You Can’t Afford to Ignore
Mar 10
Experience OutThink
What Is Domain Spoofing and Why Should You Care?
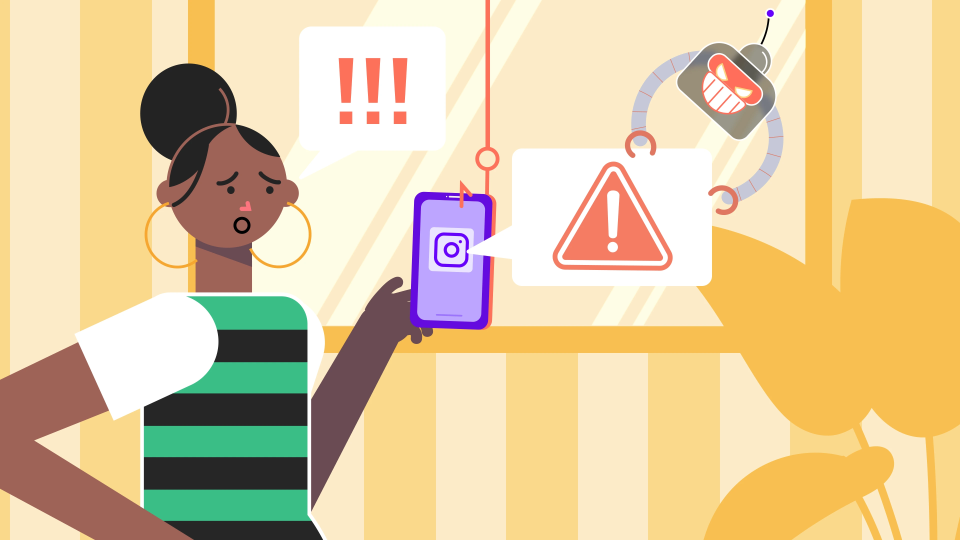
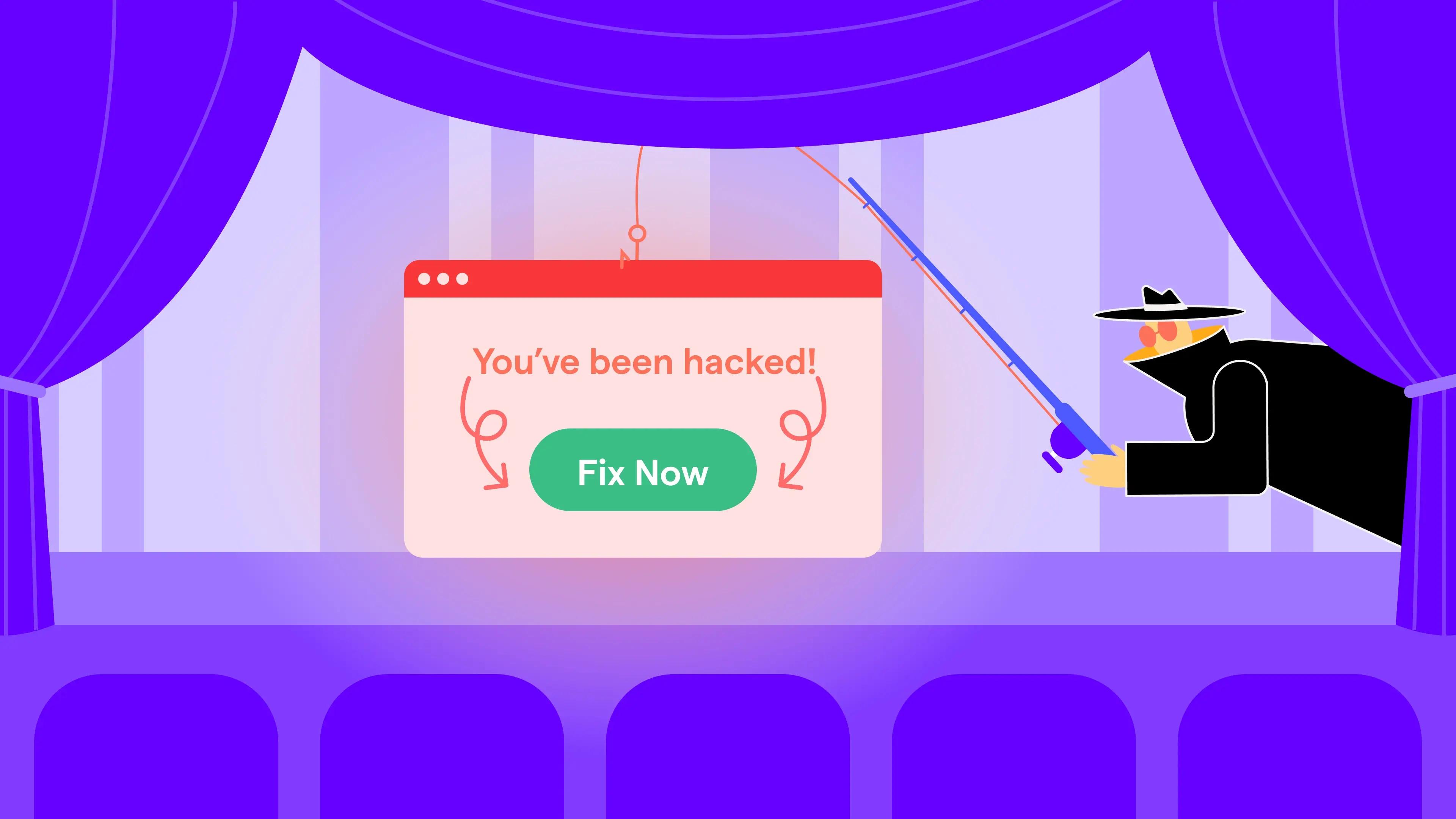
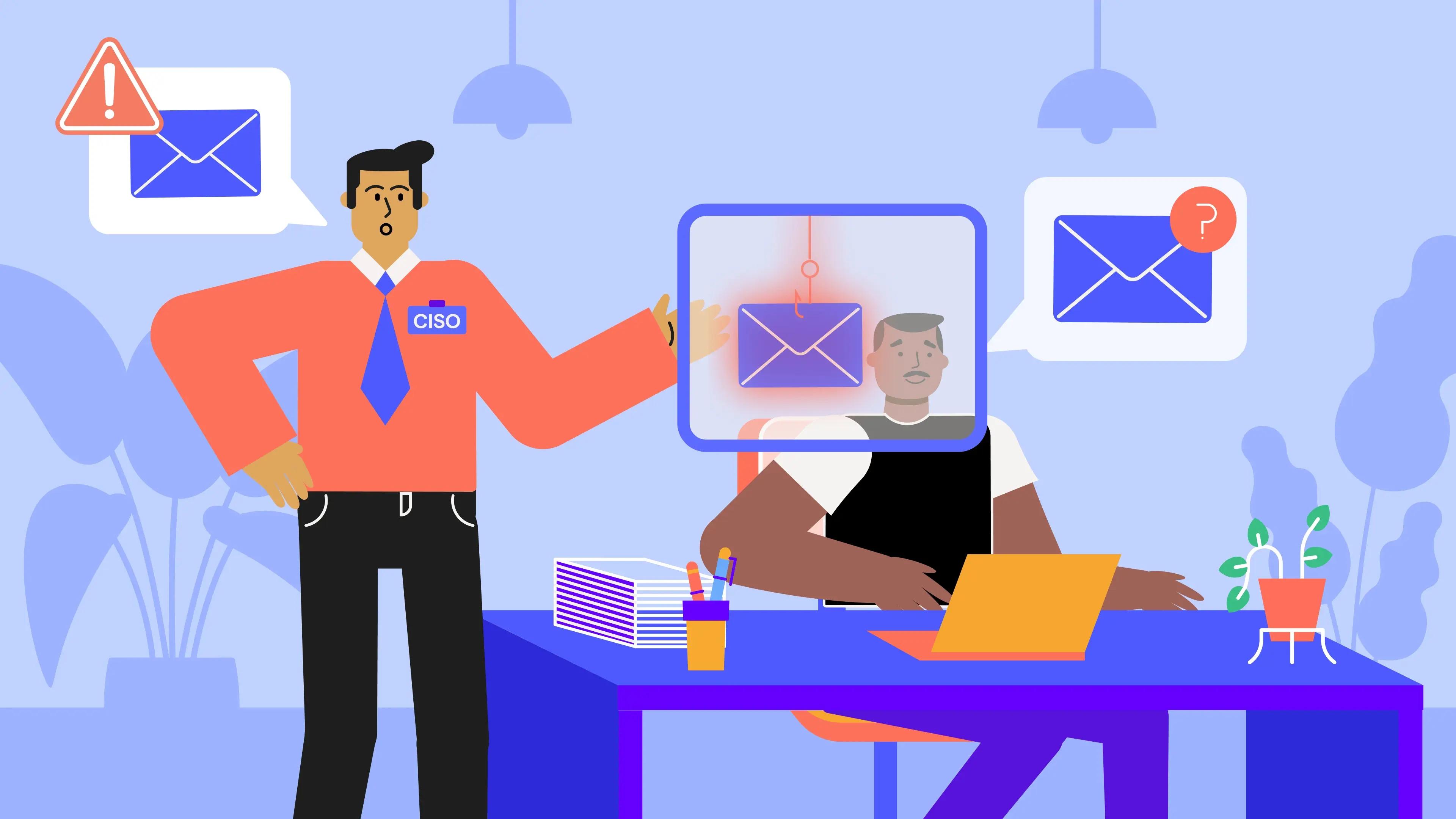
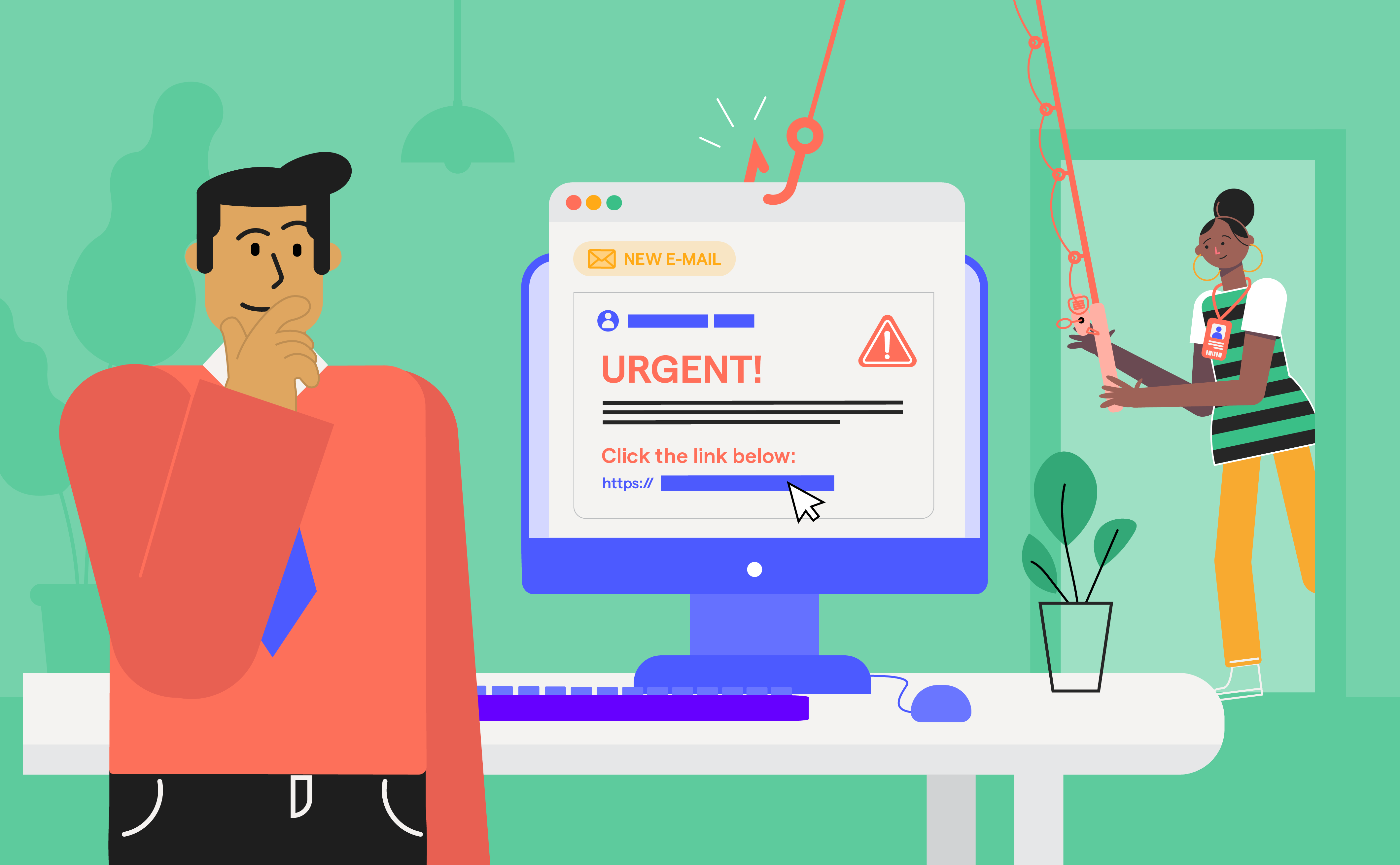
Cybercriminals' phishing techniques are getting more sophisticated and one of the most deceptive tactics they’re using today is domain spoofing. This involves faking trusted email addresses or website domains to impersonate legitimate organizations. The aim? To trick individuals or employees into clicking dangerous links, sharing sensitive information, or unknowingly downloading malware.
Phishing scams are becoming more convincing and domain spoofing has turned into a serious cybersecurity concern, especially for businesses that rely on digital communication and brand trust. This blog explores what domain spoofing is, why it’s such a growing threat, and how OutThink’s upcoming domain spoofing scanner can help organizations stay protected before attacks even reach the inbox.
A Closer Look: How Domain Spoofing Works
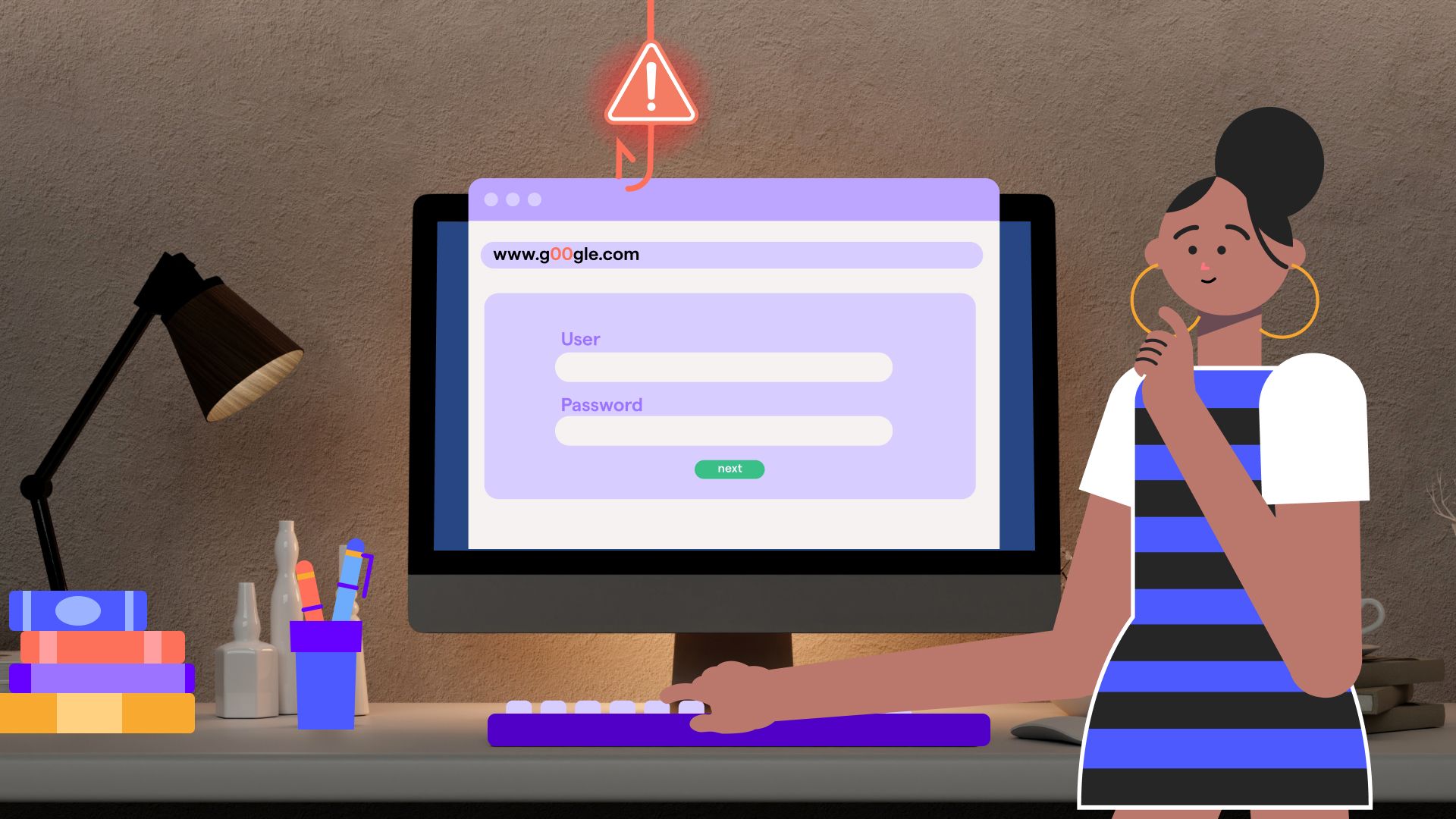
Domain spoofing is a cyber deception technique where attackers tweak email sender addresses or website domains to appear authentic, close enough to fool even vigilant users.
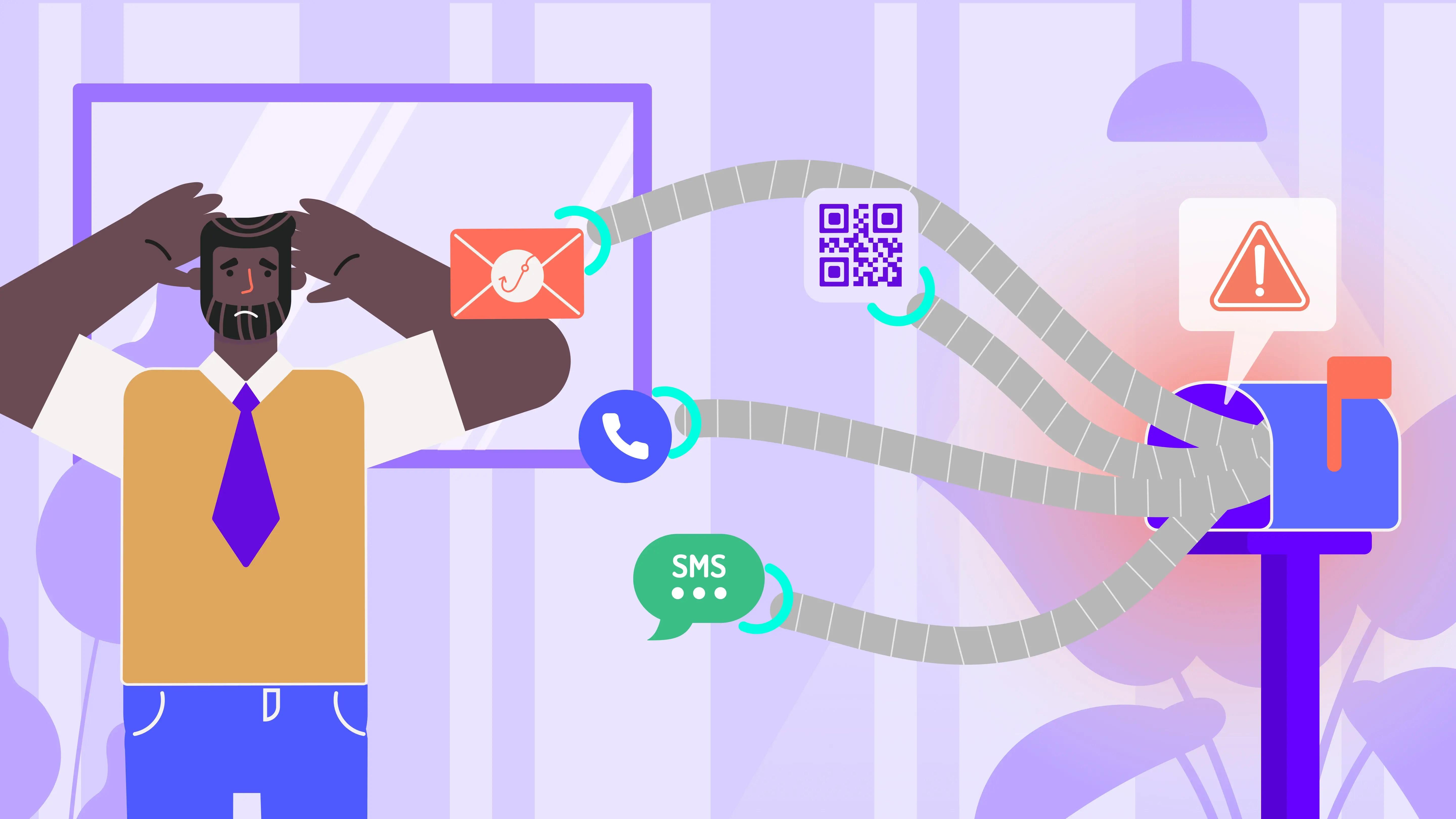
There are two primary types of domain spoofing:
- Email Spoofing: Attackers forge email sender addresses to mimic trusted contacts or institutions and send phishing emails containing malicious links or requests for sensitive data.
- Website Spoofing: Fraudsters create fake websites that resemble real ones to steal login credentials or financial details. These fraudulent domains often slightly alter characters (e.g: g00gle.com instead of google.com) to mislead users.
How Cybercriminals Use Domain Spoofing
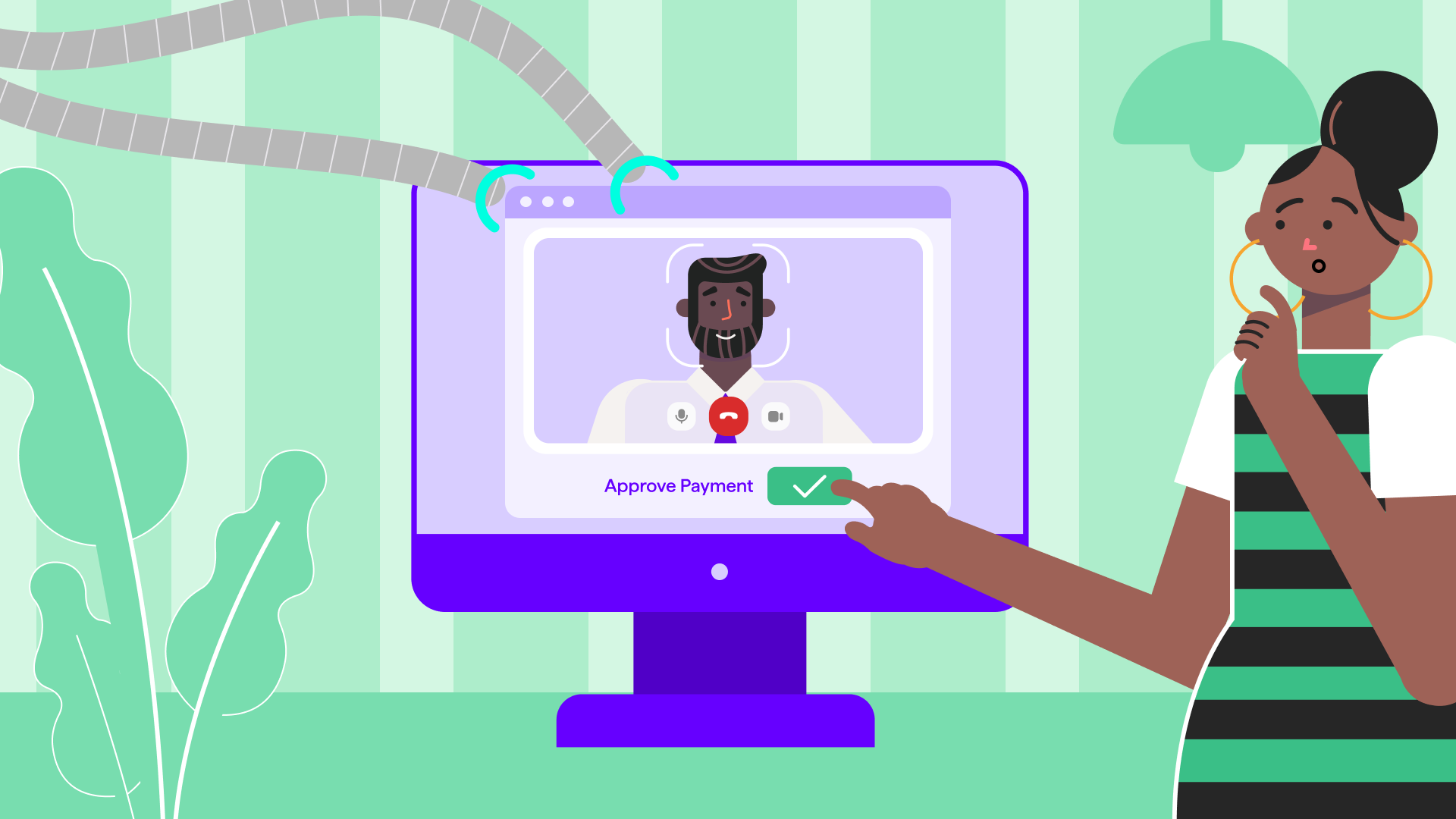
- Business Email Compromise (BEC): Attackers pose as company executives or third-party vendors to initiate fake payment requests.
- Fake Customer Support Scams: Spoofed domains mimic official help desks to steal account credentials.
- Malware Distribution: Malicious websites trick users into downloading harmful software.
According to Infoblox Threat Intel (2024), these tactics are increasingly common in phishing campaigns targeting banks, retailers, and government agencies alike.
Why Is Domain Spoofing More Dangerous Than You Think
1. Financial and Reputational Damage
It takes just one successful spoofing attack to cause serious damage. That could mean direct financial loss, regulatory penalties, and worst of all, loss of trust. When fake emails or cloned websites result in customer data breaches, the reputation you’ve worked hard to build is on the line.
2. Bypassing Traditional Security Measures
Even with standard email authentication protocols (eg: SPF, DKIM, and DMARC) in place, spoofing can still slip through your defenses, especially when attackers use lookalike domains that are nearly impossible to spot.
3. Increased Targeting of Employees
Cybercriminals are crafting smarter, more convincing phishing emails aimed directly at employees at all levels. Even cybersecurity-savvy individuals can fall victim to carefully crafted phishing emails that appear genuine.
How to Spot and Stop Domain Spoofing
1. Enforce Email Authentication Protocols
Email security protocols like SPF (Sender Policy Framework), DKIM (Domain Keys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance) help authenticate email senders and prevent spoofing attempts.
2. Train Employees to Stay Alert
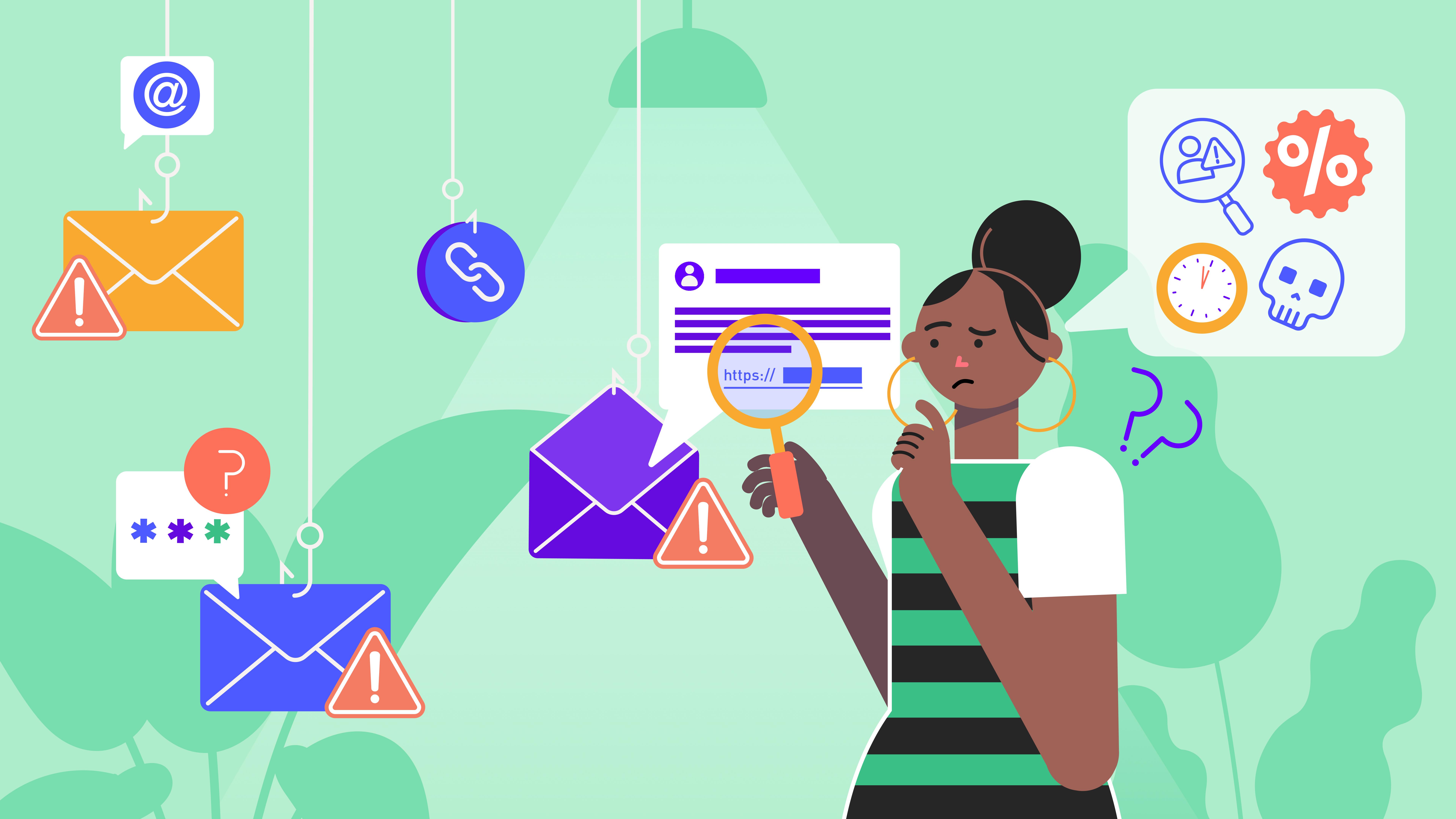
Security awareness training should teach employees to identify red flags in emails, such as:
- Unusual sender addresses
- Urgent requests for sensitive data
- Links that redirect to suspicious websites
3. Use a Domain Spoofing Check Tool
Automated tools can scan for fraudulent domains, detect impersonation attempts, and flag suspicious activity in real time.
OutThink’s Domain Spoofing Scanner: A Game-Changer in Cybersecurity
OutThink is preparing to launch a powerful domain spoofing scanner on its website designed to help organizations detect and stop spoofing threats before they escalate. This solution will:
- Spot Lookalike Domains: Identify fraudulent variations that closely resemble your brand’s official domain.
- Detect Email Impersonation: Analyze incoming messages for signs of spoofing or phishing.
- Deliver Real-Time Insights: Provide actionable threat intelligence to strengthen your overall cybersecurity strategy.
By integrating this domain spoofing check into your cybersecurity framework, organizations can proactively protect employees, customers, and digital assets from emerging threats.
Cultivate These Practices to Protect Your Organization
- Monitor Domain Activity Regularly: Use WHOIS databases and monitoring tools to detect unauthorized registrations and suspicious domain behavior.
- Enable Multi-Factor Authentication (MFA): Add an extra layer of protection to prevent account takeover, even if credentials are compromised.
- Block Similar Domains: Use filters to flag or block emails from domains that closely mimic your own, reducing the chance of impersonation slipping through.
Be Proactive, Not Reactive - Guard Against Domain Spoofing
Domain spoofing is only getting more sophisticated. To stay ahead, organizations must combine strong technical controls with human awareness and real-time threat detection.
Implementing robust email protocols, training employees to recognize phishing tactics, and adopting advanced tools like OutThink’s domain spoofing scanner can go a long way in preventing fraud and safeguarding your brand’s digital reputation.